What Is a Threat Intelligence Platform — and What Makes ThreatSearch Different?
A Threat Intelligence Platform (TIP) is a security system that aggregates, normalizes, enriches, and operationalizes threat data from multiple sources — transforming raw indicators into actionable intelligence that security teams can act on in real time. Without a TIP, SOC analysts are drowning in unstructured, duplicate, and context-free data from dozens of disconnected feeds that individually tell them very little.
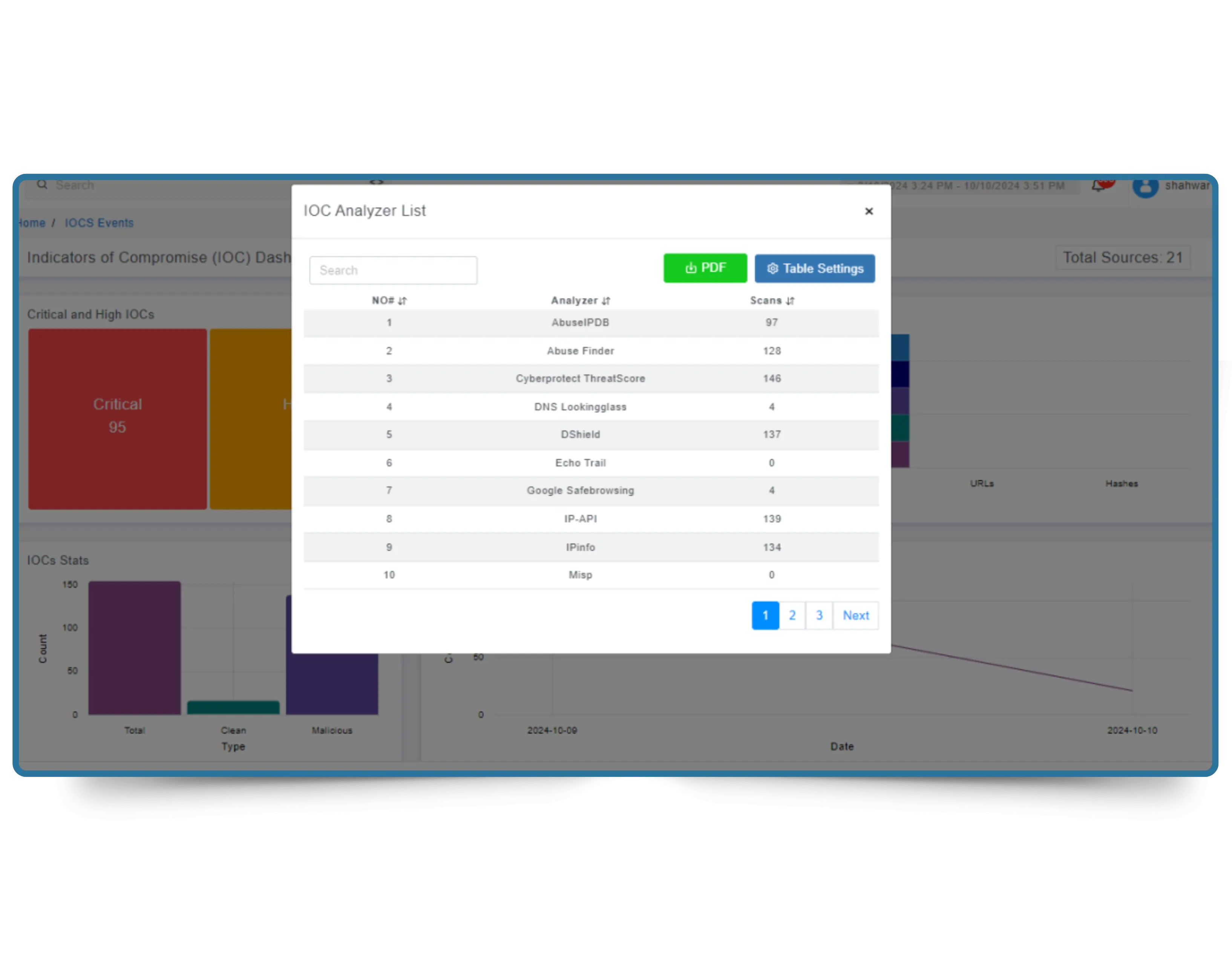
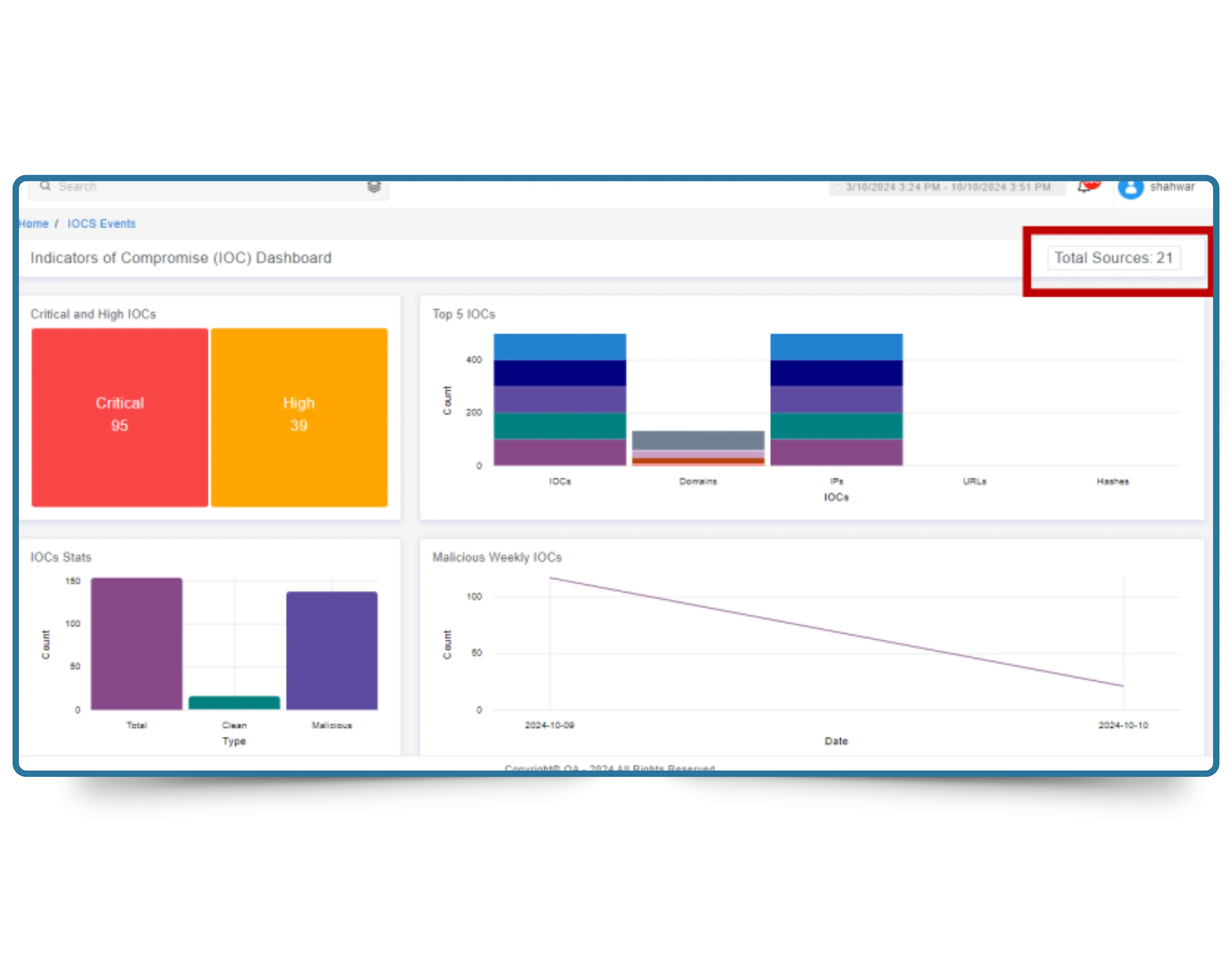
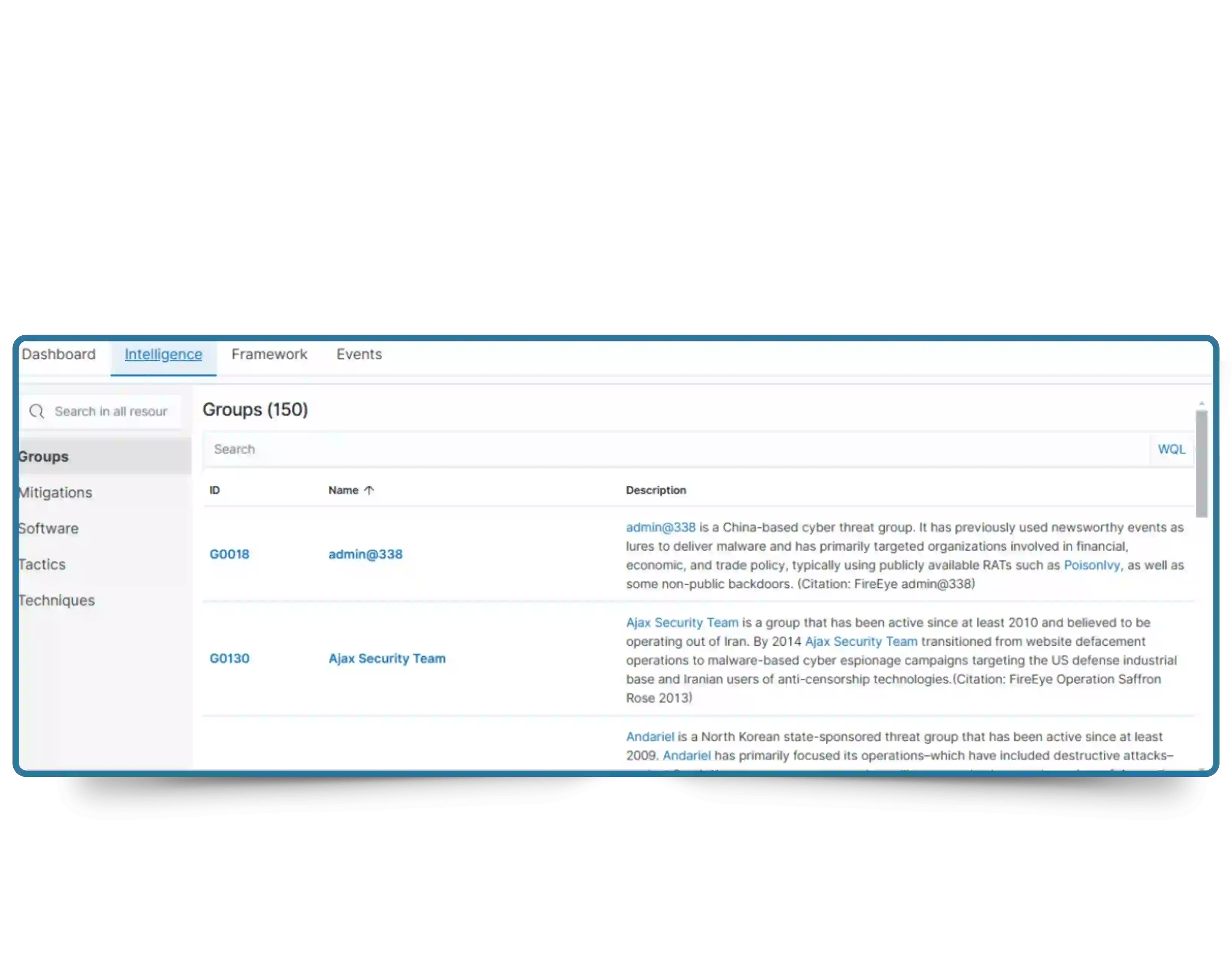
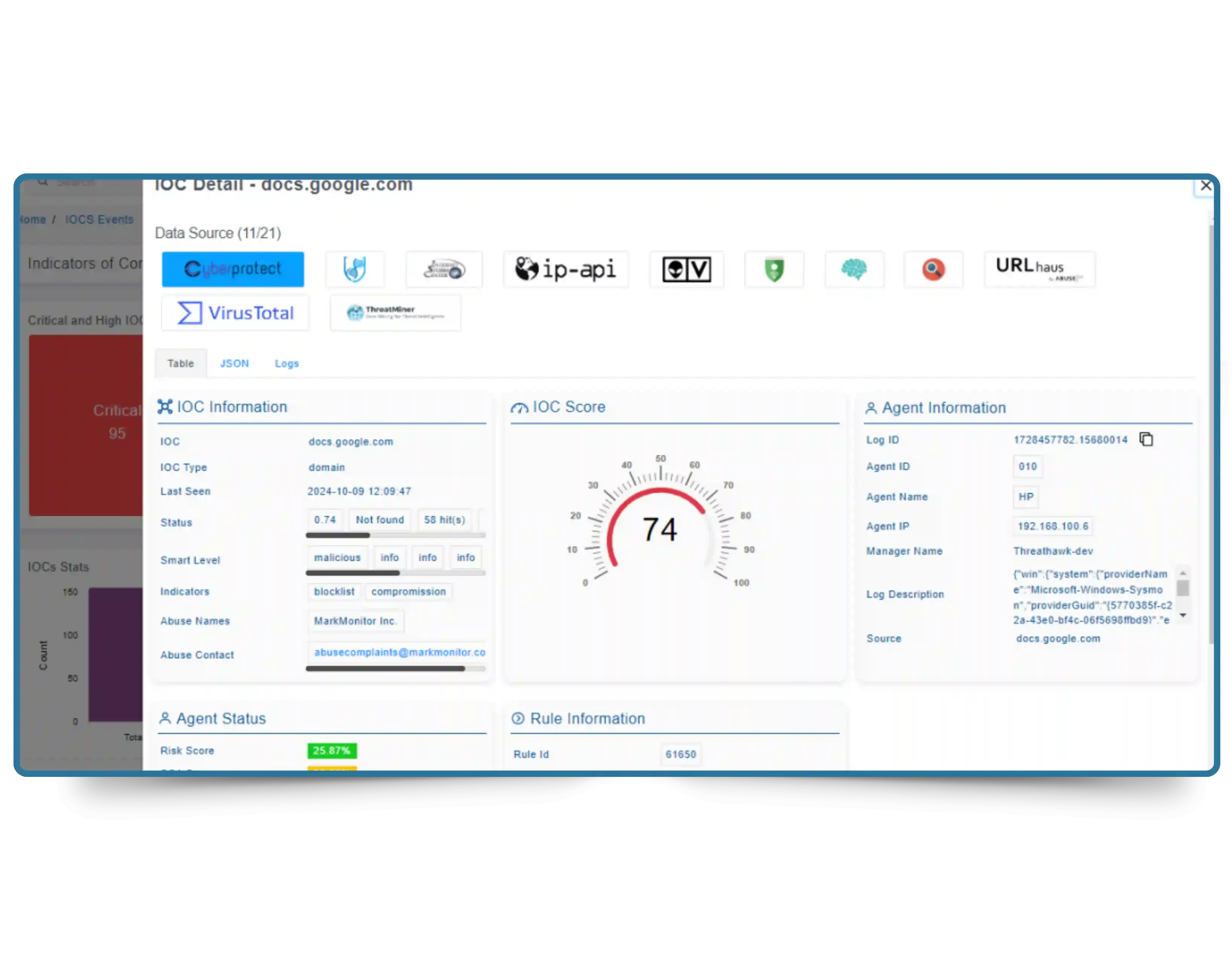
ThreatSearch TIP goes beyond simple data aggregation. It pulls from 24+ global, regional, and industry-specific sources — including open-source intelligence (OSINT), commercial threat feeds, Information Sharing and Analysis Centers (ISACs), dark web forums, and malware repositories — then applies multi-factor automated threat scoring, MITRE ATT&CK contextualization, and behavioral correlation to turn raw IOCs into prioritized, decision-ready intelligence.
The result flows automatically into ThreatHawk SIEM and any connected SIEM, EDR, firewall, or SOAR platform via native integrations and REST APIs. Your defenses update the moment new threat intelligence is discovered — not hours later after a batch sync. See how ThreatSearch compares to the top threat intelligence platforms available today.
24+
Global Threat Feed Sources
Real-Time
IOC Updates & Auto-Sync
Millions
IOCs Processed Per Minute
Zero
Manual Ingestion Required