Security Information & Event Management
What is ThreatHawk SIEM?
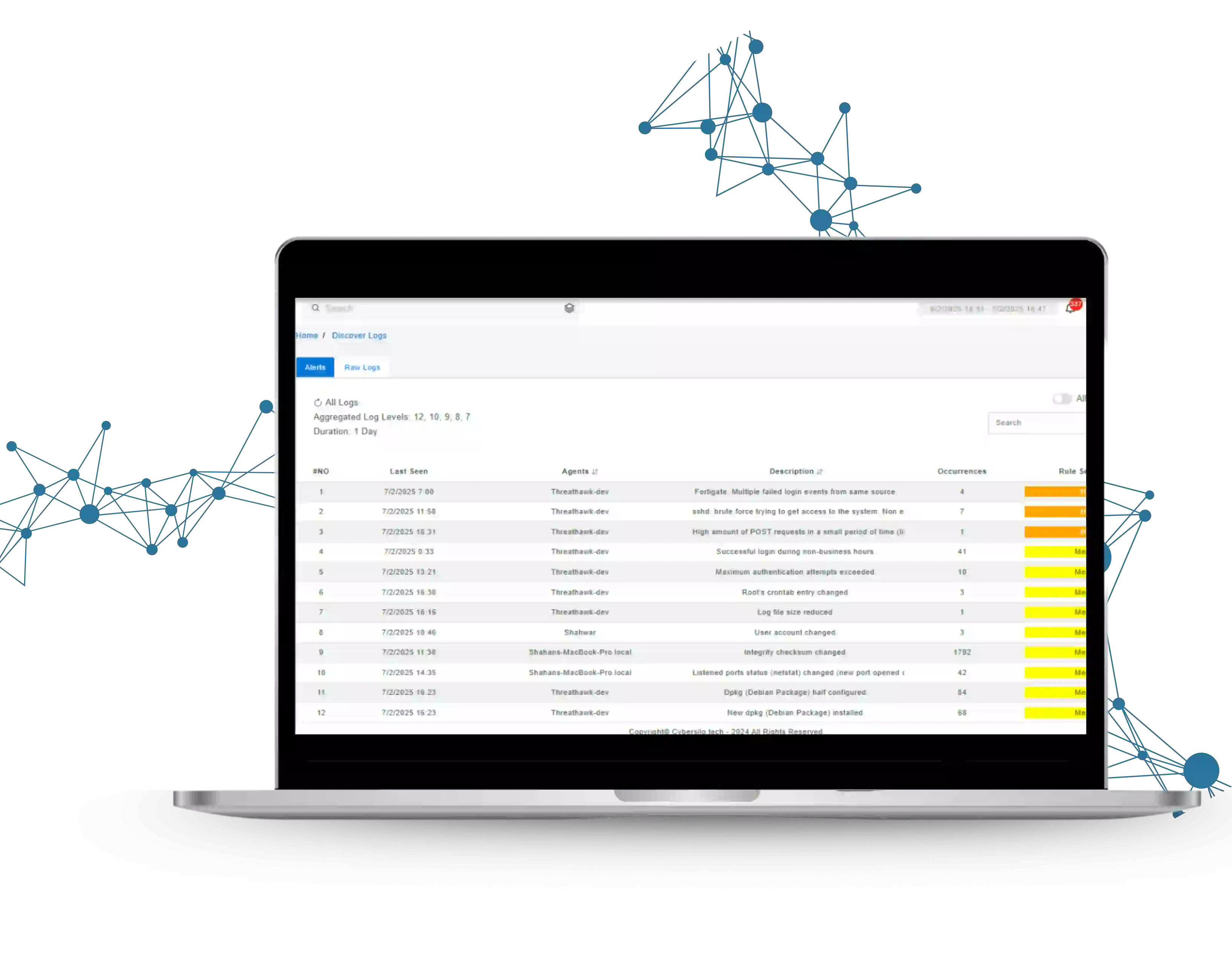
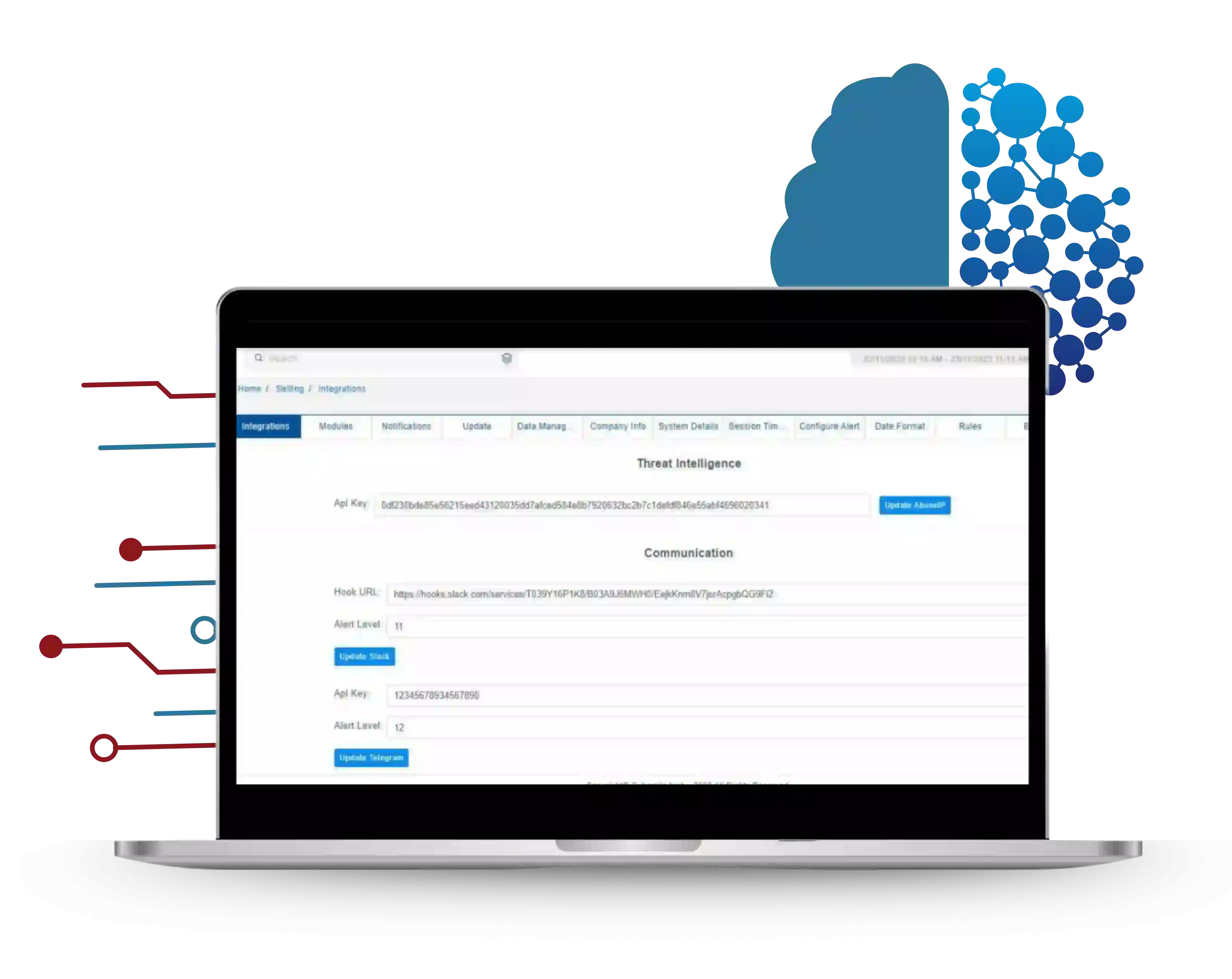
ThreatHawk SIEM is CyberSilo's enterprise-grade, AI-powered Security Information and Event Management (SIEM) platform. It collects, normalizes, and correlates security event data from every layer of your infrastructure — cloud, endpoints, network devices, and SaaS applications — into a single unified view, then applies machine learning and behavioral analytics to identify real threats with precision.
Unlike traditional SIEM tools that rely on static, rule-based detection and generate high false-positive rates, ThreatHawk SIEM uses User and Entity Behavior Analytics (UEBA) and MITRE ATT&CK-aligned detection logic to catch what others miss — including zero-day exploits, lateral movement, insider threats, and advanced persistent threats (APTs) — before damage is done.
The result: a security operations team that spends less time chasing noise and more time stopping real threats. Clients report a 68% reduction in mean-time-to-detect and a 54% drop in false positive alerts within 90 days of deployment.
600+Detection Rules
200+Integrations
500K+Events/Second
70%Less Analyst Workload