What Is Threat Exposure Management — and Why Is It Replacing Traditional Vulnerability Management?
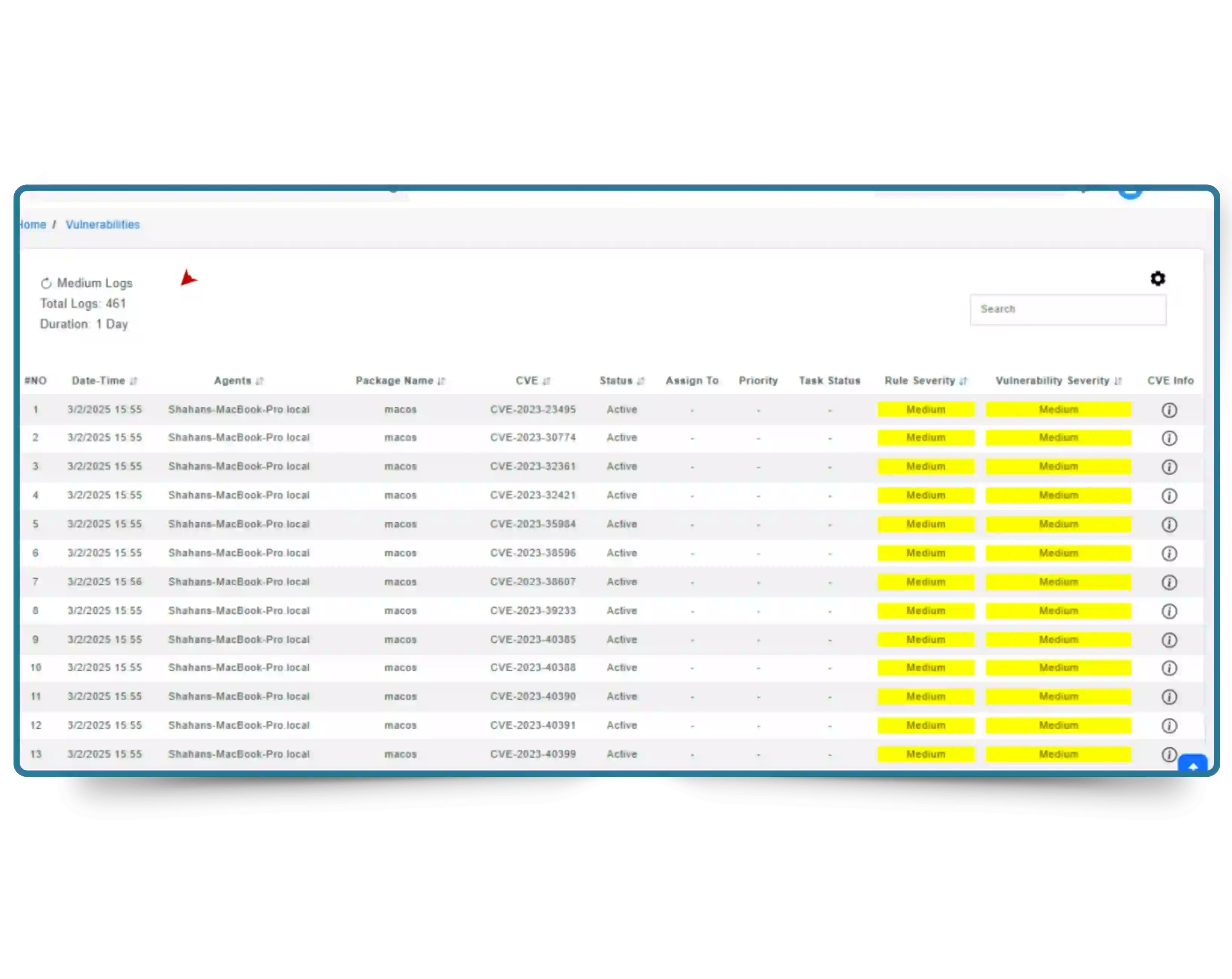
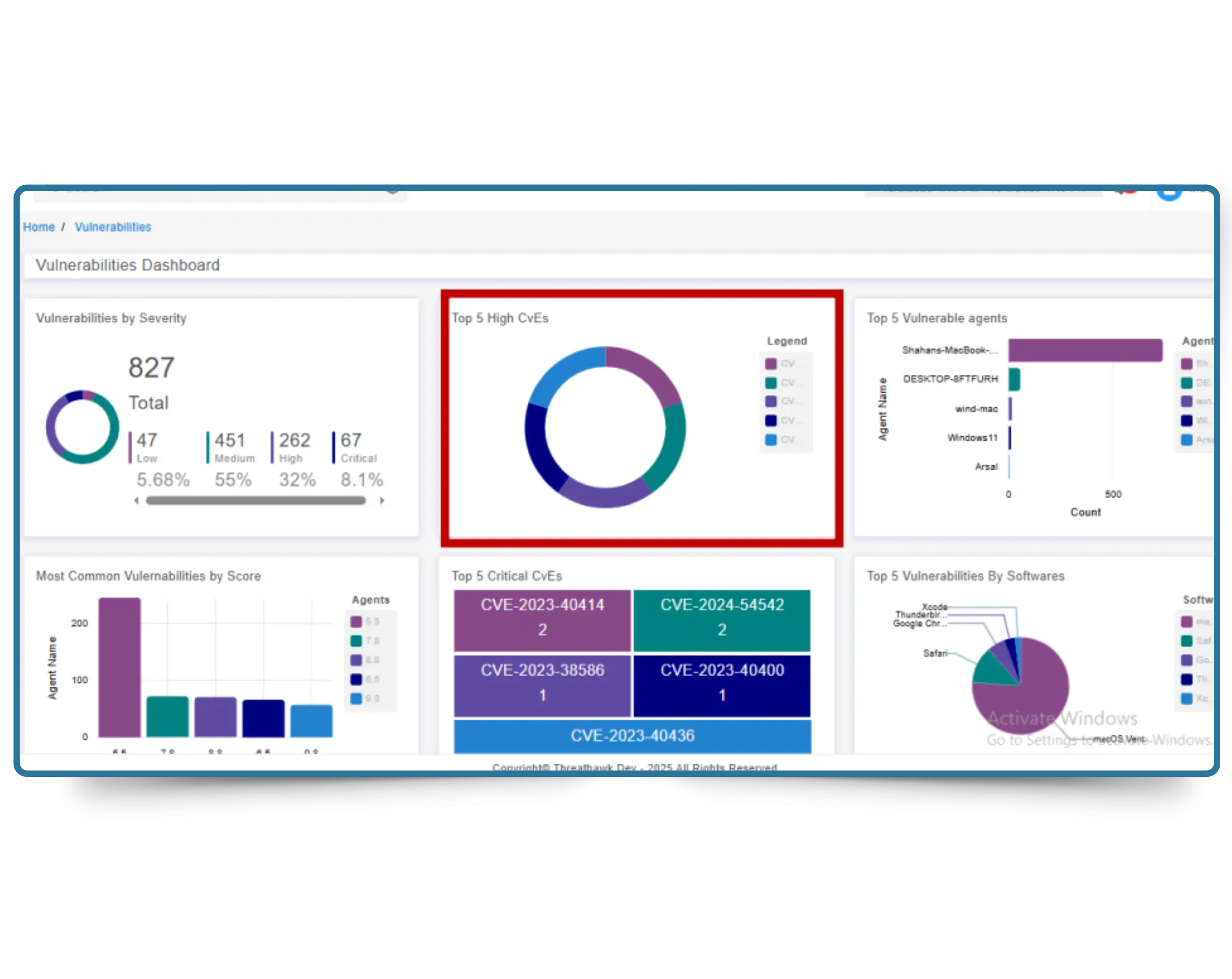
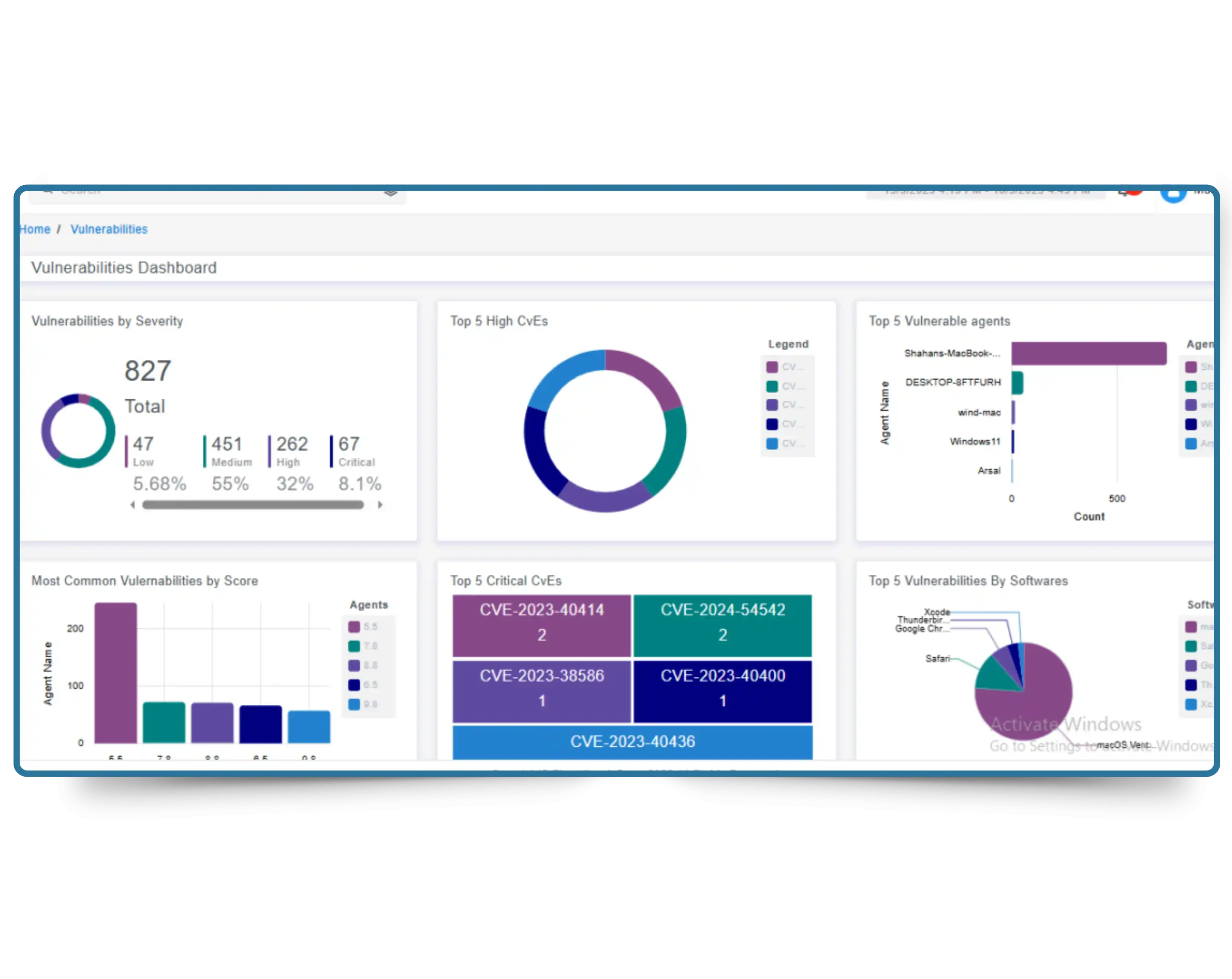
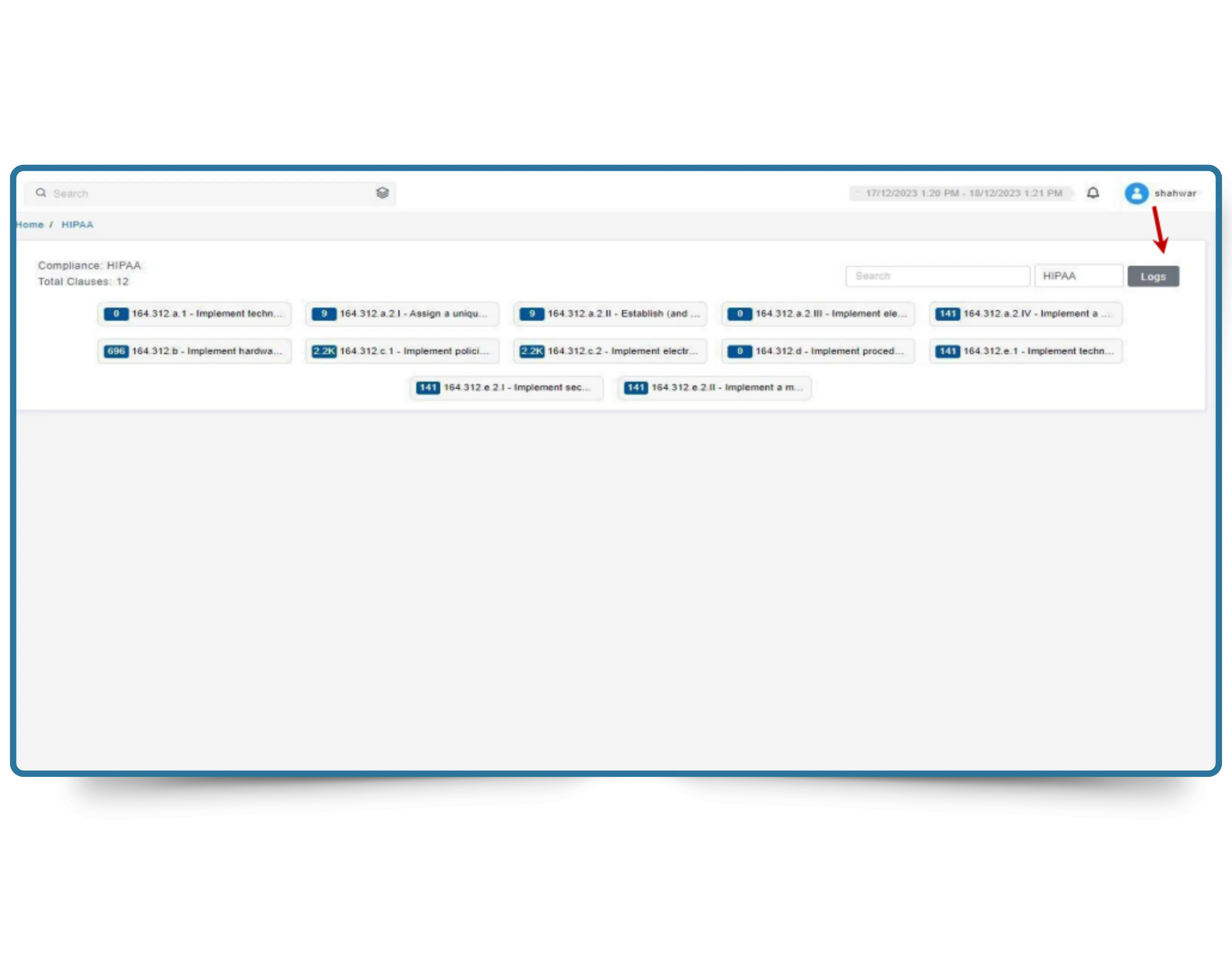
Threat Exposure Management (TEM) is a continuous cybersecurity practice that identifies, enriches, prioritizes, and remediates vulnerabilities and exposures across an organization's entire attack surface — endpoints, servers, network devices, cloud workloads, and external-facing assets — on an ongoing basis, not just during scheduled scan windows.
Traditional vulnerability management runs periodic scans and prioritizes findings by CVSS severity score alone. This creates a dangerous prioritization gap: teams spend months patching high-CVSS vulnerabilities that attackers never exploit, while actively weaponized lower-severity CVEs remain open. Gartner identified TEM as one of the top cybersecurity trends precisely because this gap is where breaches happen.
CyberSilo TEM closes this gap by combining continuous asset discovery, real-time CVE ingestion, and CVSS + EPSS combined scoring — so remediation effort is focused on the vulnerabilities attackers are actively exploiting right now, not those with the highest theoretical severity. See how TEM compares to the top threat exposure monitoring tools available today, or explore how ThreatHawk SIEM integration extends TEM's vulnerability context into real-time threat detection.
40%
Reduction in Exploitable Attack Surface
Continuous
Scanning — No Batch Windows
CVSS+EPSS
Combined Risk Prioritization
100%
Asset Coverage: Cloud, On-Prem, Hybrid