What Are CIS Benchmarks & CIS Controls — and Why Does Automated Assessment Matter?
CIS Benchmarks are the globally recognized secure configuration guidelines published by the Center for Internet Security (CIS) — providing specific, consensus-based hardening recommendations for operating systems, cloud platforms, applications, network devices, and databases. Over 100 CIS Benchmark documents cover everything from Windows Server and Linux to AWS, Azure, GCP, Docker, Kubernetes, and Cisco devices.
CIS Controls (v8) are the 18 prioritized cybersecurity best practices that form the strategic foundation — CIS Benchmarks are the technical implementation guides that verify CIS Controls are properly configured in your environment. Misconfiguration remains the single most common cause of enterprise security incidents, yet manually reviewing hundreds of configuration settings across thousands of assets is operationally impossible.
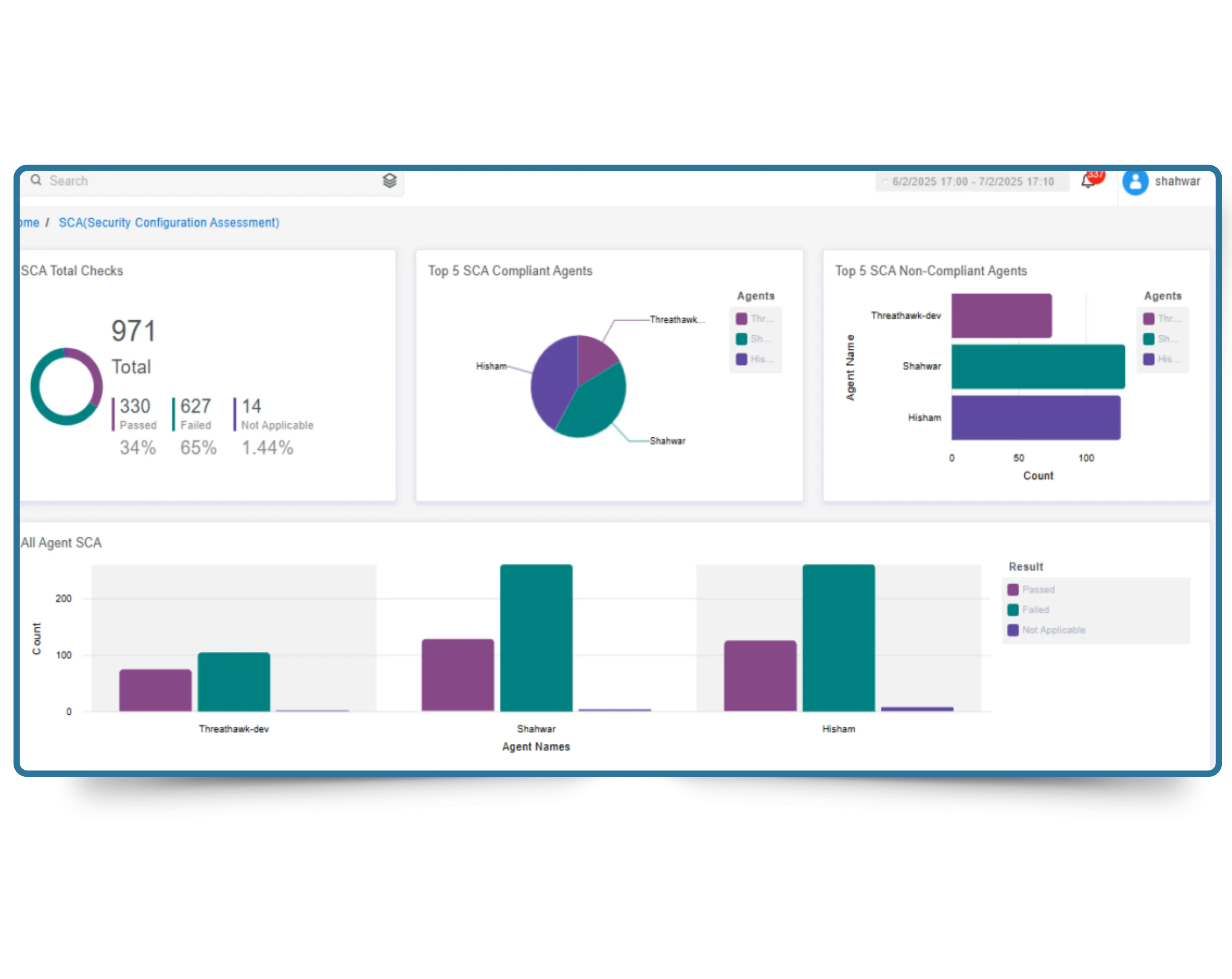
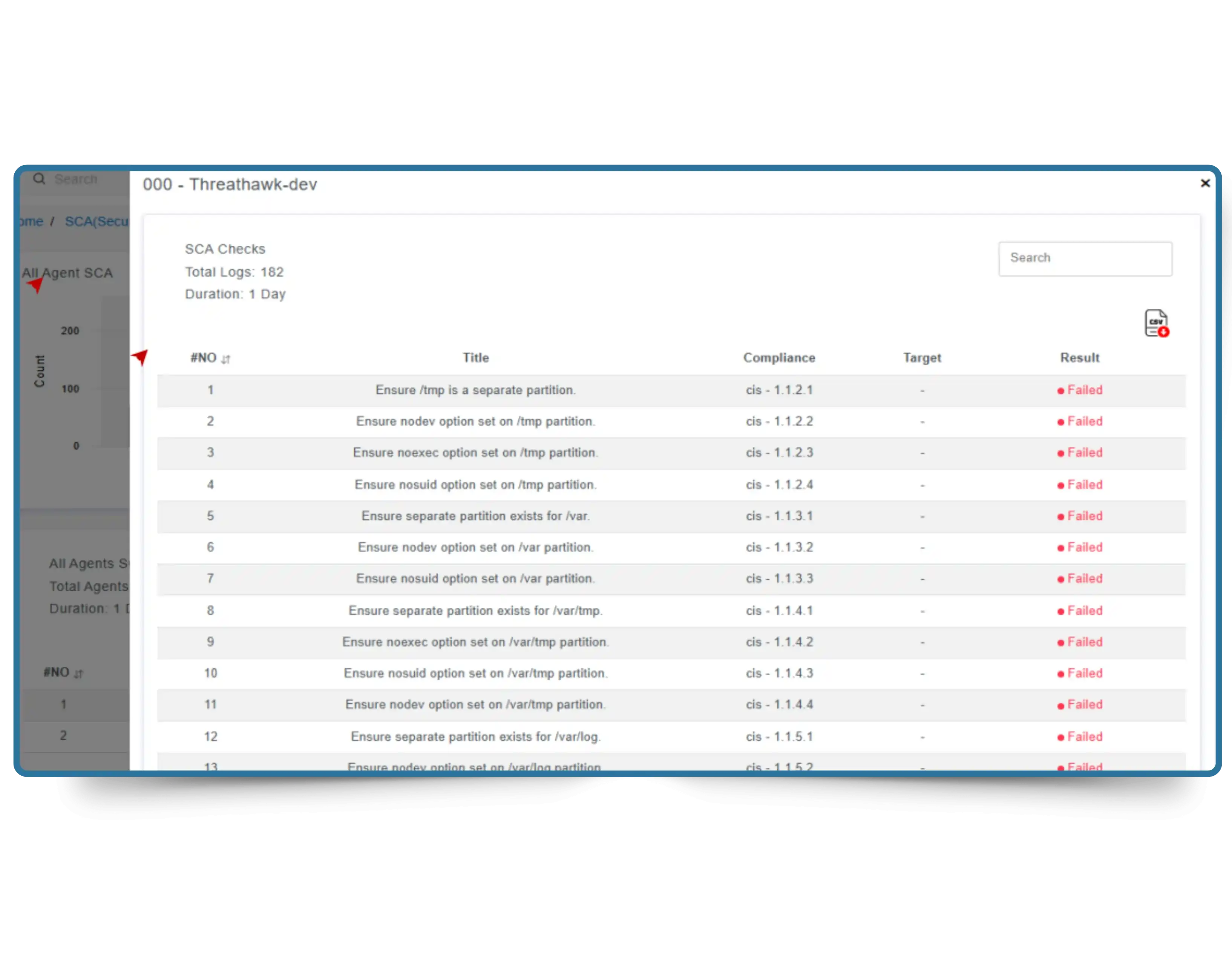
CyberSilo's CIS Benchmarking Tool automates this entirely — continuously scanning every asset, scoring compliance against the relevant CIS Benchmark, flagging deviations with prioritized remediation guidance, and generating audit-ready reports automatically. See how CyberSilo compares in our independent review of the top 10 CIS benchmarking tools available today, or understand how CIS assessment integrates with broader GRC compliance automation.
30%
Better Threat Detection with Hardened Baselines
40%
Faster Incident Response via SIEM Integration
25%
Fewer False Positives from Hardened Environments
Continuous
Configuration Drift Detection — No Manual Scans