Unified SIEM & SOAR Platform
What is ThreatHawk SIEM & SOAR?
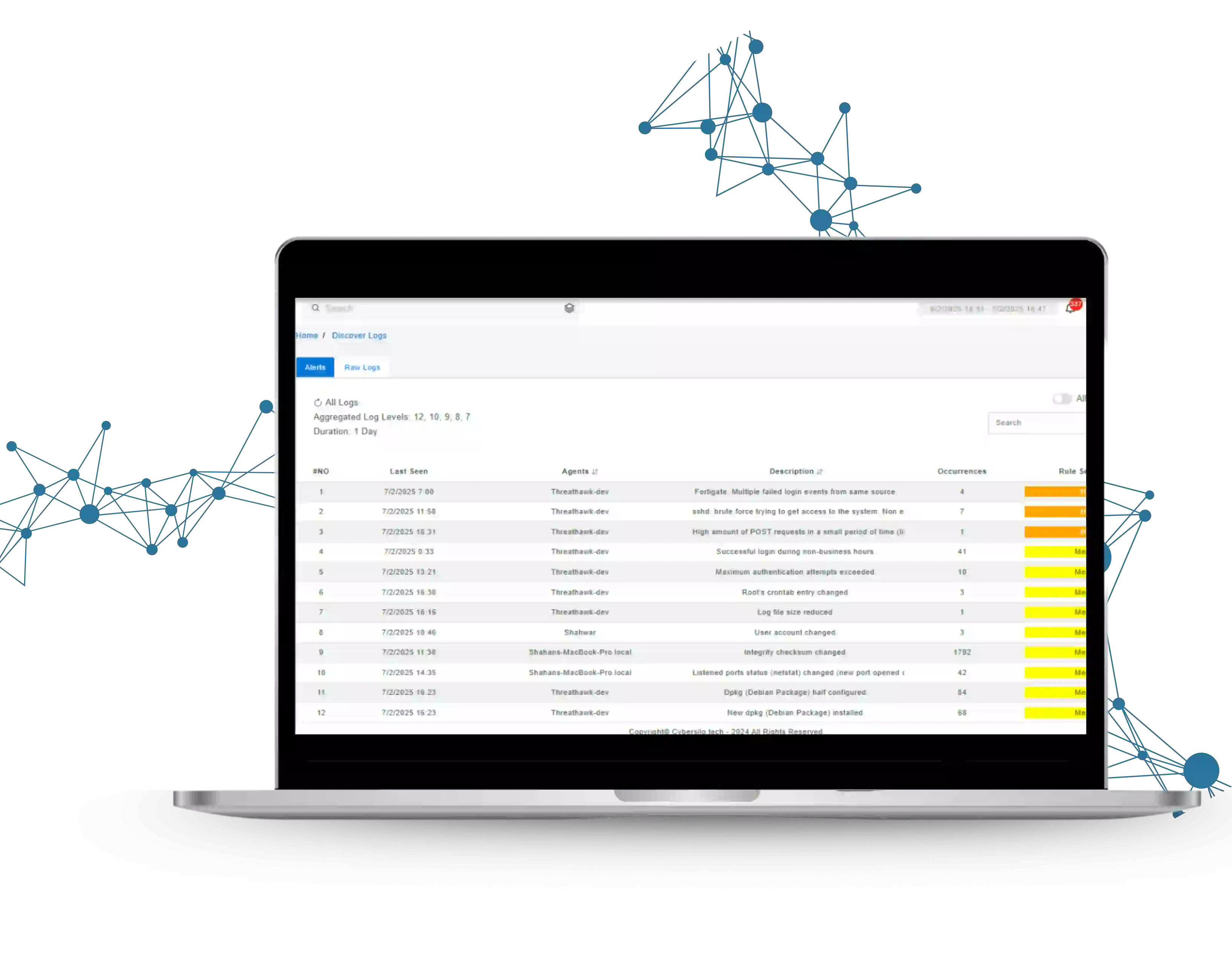
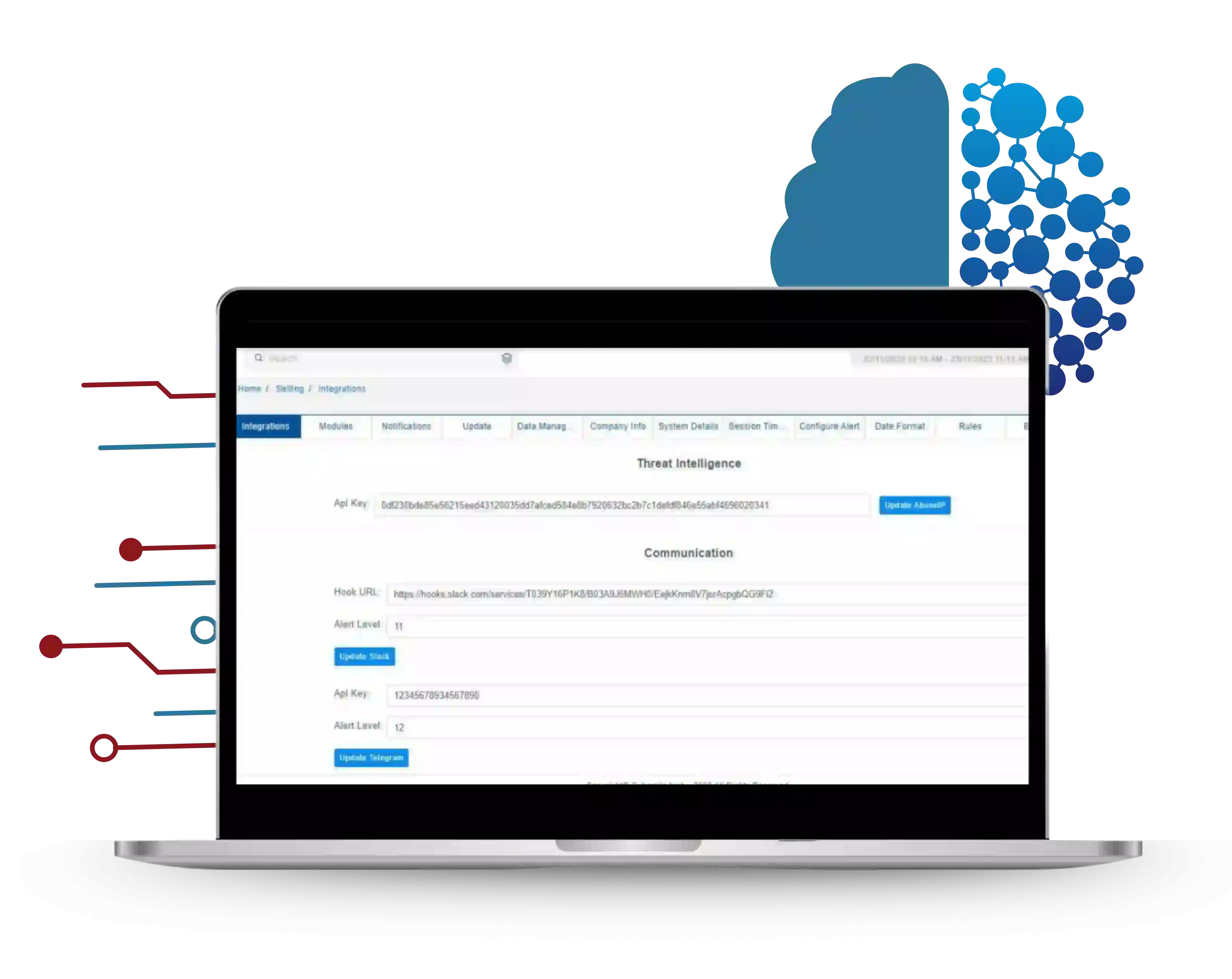
ThreatHawk SIEM & SOAR is CyberSilo's enterprise-grade platform combining Security Information and Event Management (SIEM) and Security Orchestration, Automation, and Response (SOAR) in one natively integrated product — not two tools stitched together. The SIEM detects threats using AI-powered behavioural analytics and 600+ MITRE ATT&CK-aligned rules; the SOAR responds automatically using customisable playbooks. Both share the same rule engine, alert data, and agent telemetry, eliminating the integration gaps that weaken standalone deployments.
Legacy SIEM platforms such as Splunk, QRadar, and Microsoft Sentinel require a separate SOAR licence and integration layer — adding cost, complexity, and latency to every incident response workflow. ThreatHawk's AI behavioural analytics and User and Entity Behavior Analytics (UEBA) deliver 600+ MITRE ATT&CK-aligned detections that catch zero-day attacks and advanced persistent threats, while the native SOAR engine reduces false positives by 70% and eliminates Tier-1 manual escalations entirely.
Security teams using ThreatHawk as their automated incident response platform consistently report a 68% reduction in mean-time-to-detect, a 54% drop in false positives within 90 days of deployment, and a 70% reduction in overall analyst workload. Drag-and-drop playbook creation means response automation requires no engineering support — your SOC team builds, deploys, and iterates on playbooks independently.
600+Detection Rules
200+Integrations
500K+Events/Second
70%Less Analyst Workload