Why Standard Security Tools Fail SAP Environments — and What SAP Guardian Does Differently
SAP ERP systems are the operational backbone of most large enterprises — processing financial transactions, managing payroll and HR data, controlling procurement and supply chain, and storing the most sensitive business intelligence your organization holds. This makes SAP environments one of the highest-value targets for both external attackers and malicious insiders. Yet most organizations protect SAP with tools never designed for it.
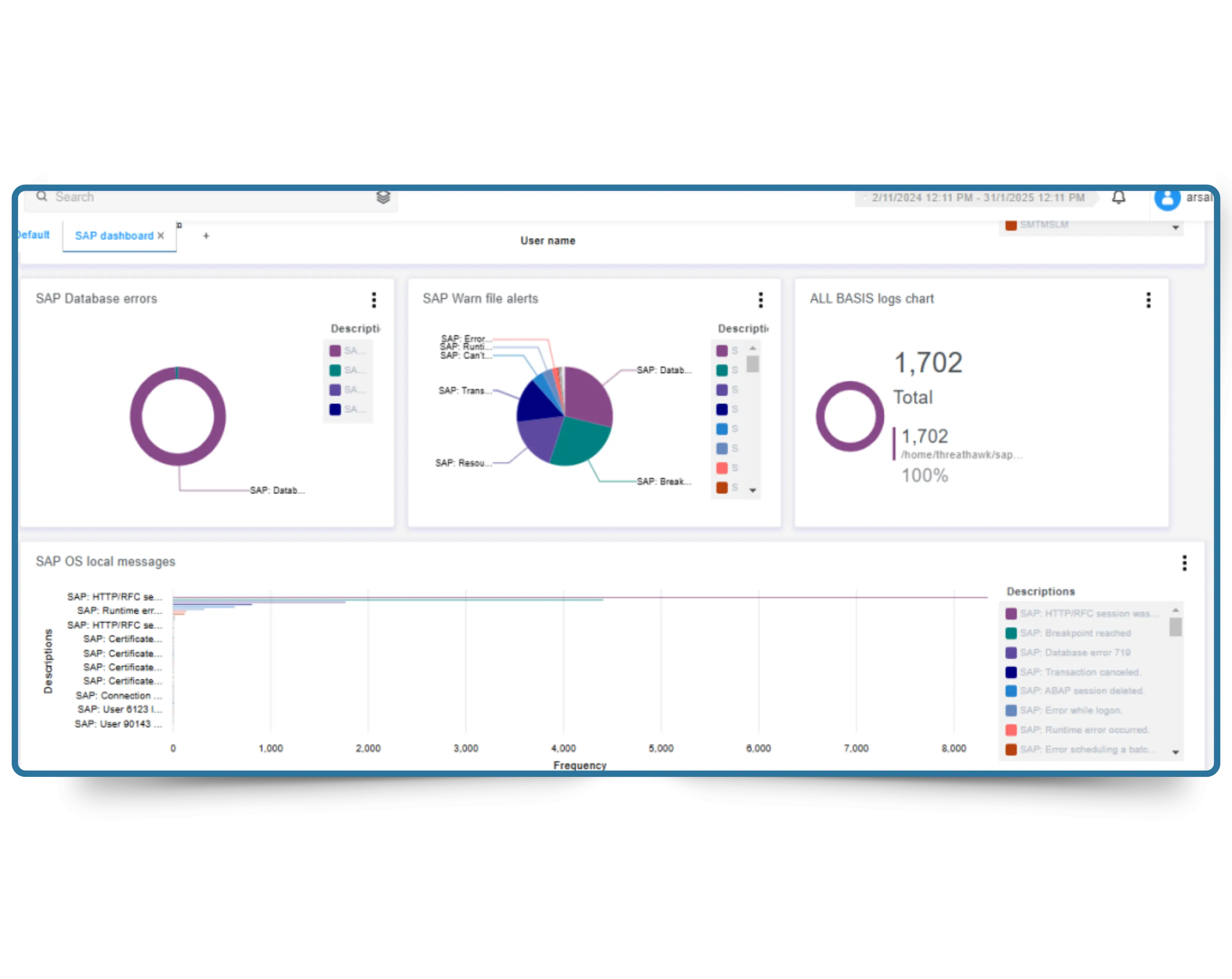
Standard SIEM platforms can ingest SAP logs, but without SAP-native context — transaction code awareness, authorization object understanding, and RFC protocol parsing — they generate enormous volumes of meaningless alerts while missing the SAP-specific attack patterns that actually matter. An unauthorized SU01 access, an abnormal BAPI call, or a suspicious RFC destination change looks like noise to a generic SIEM but is a high-severity threat signal to someone who understands SAP architecture.
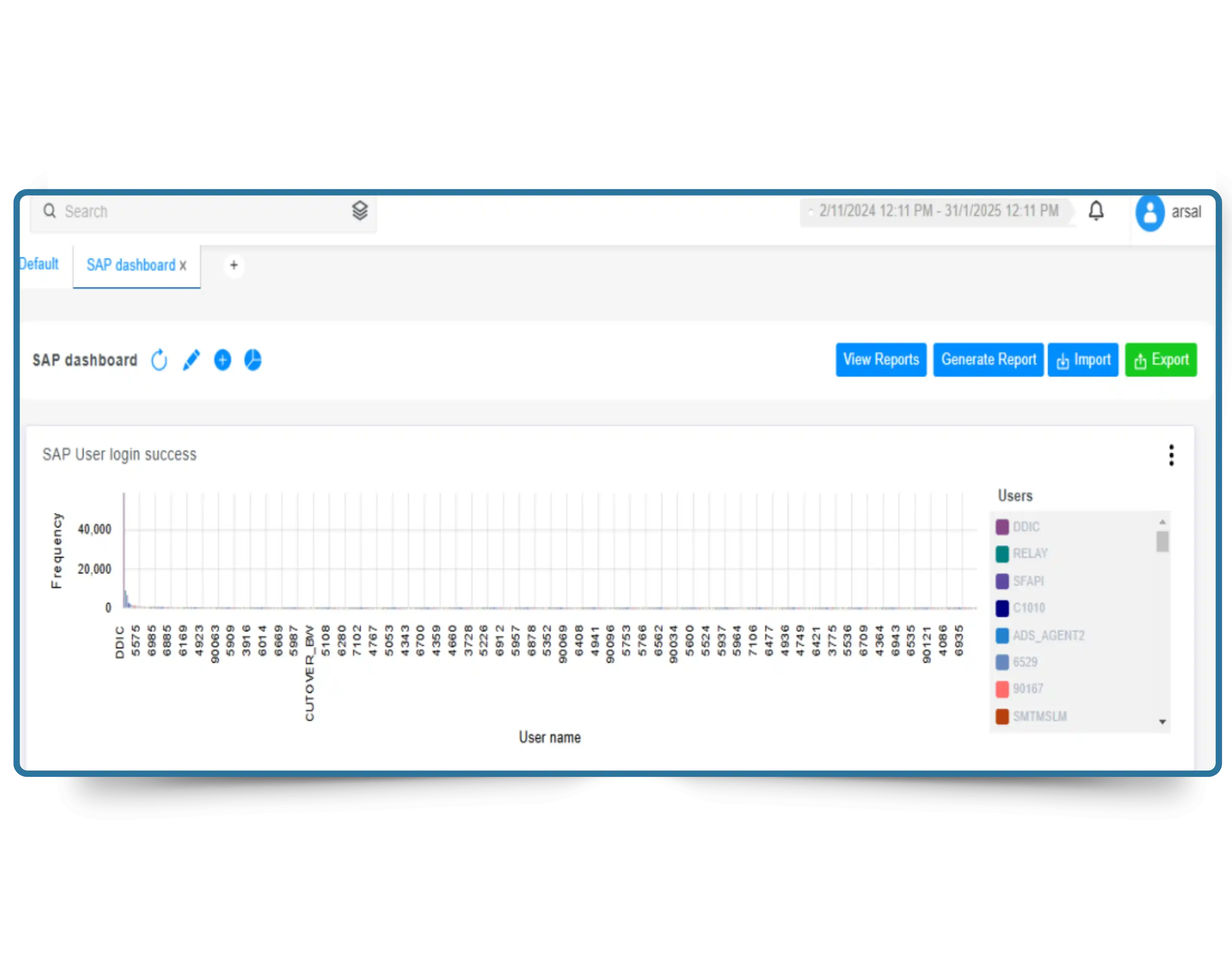
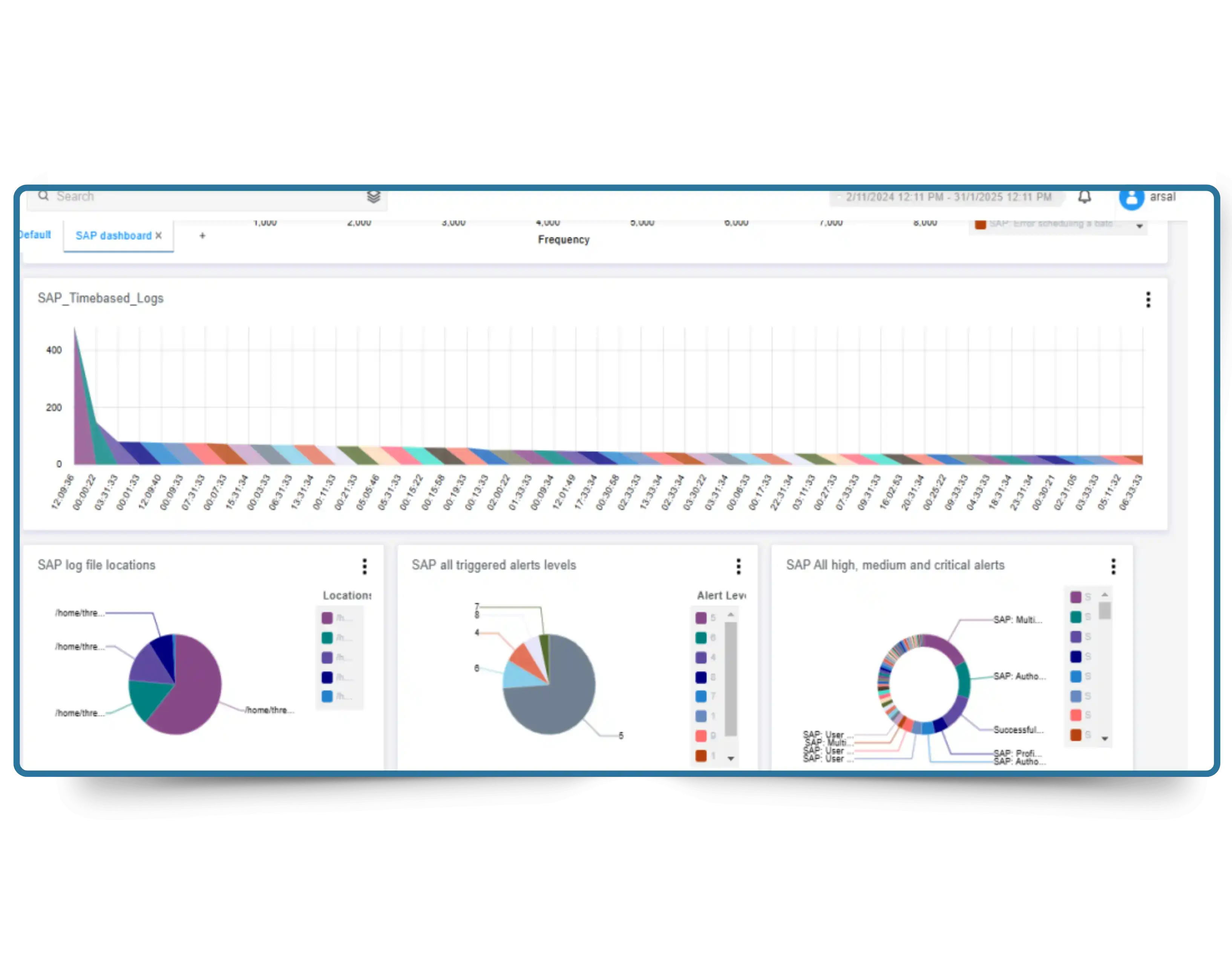
CyberSilo SAP Guardian is built by security professionals who understand SAP at the transaction level. It monitors 50+ native SAP log types — including HANA Audit, Security Audit Log, Gateway logs, and Read Access logs — with detection logic calibrated to real SAP attack patterns. The result is 90% fewer false positives compared to generic monitoring tools, and detection of the SAP-specific threats that others miss entirely. See how SAP Guardian integrates with CyberSilo's threat intelligence platform for real-time SAP-specific threat feed correlation.
50+
Native SAP Log Types Monitored
30%
Reduction in SAP Security Risk
80%
Reduction in Audit Prep Time
<2%
CPU Impact on SAP Systems