What Is Agentic SOC AI — and Why Is It Different from Traditional SOC Automation?
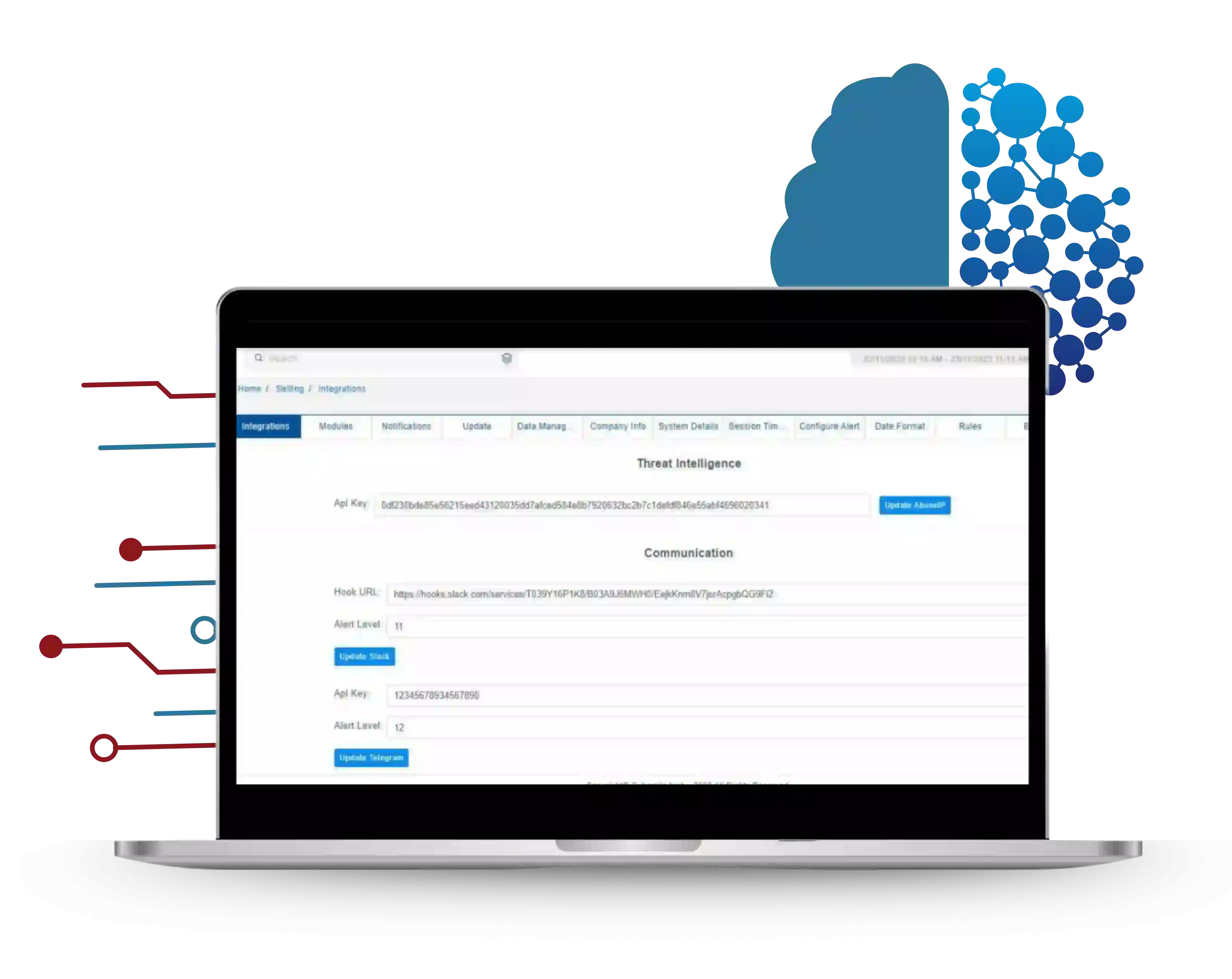
Agentic SOC AI is an autonomous security operations platform where AI agents independently execute Security Operations Center (SOC) tasks — threat triage, alert investigation, contextual enrichment, and incident response — without requiring constant analyst instruction. The term "agentic" distinguishes this approach from traditional SOC automation: agentic systems reason about novel threats and adapt autonomously, while traditional SOAR platforms execute predefined playbooks for known scenarios only.
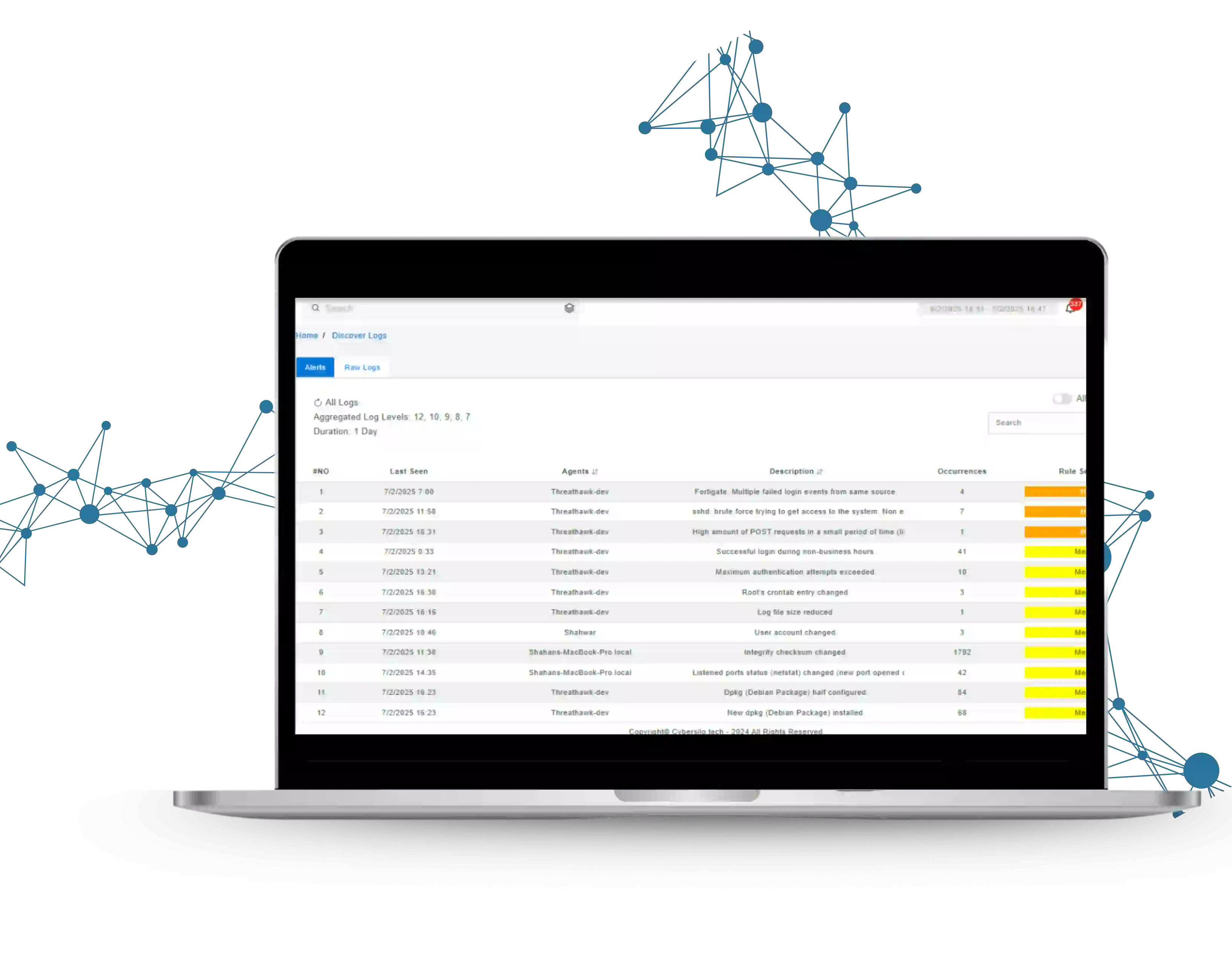
Traditional SOCs face a compounding crisis: alert volumes have grown 25% annually while analyst headcount has not kept pace. The result is alert fatigue — analysts reviewing hundreds of daily alerts, the majority of which are false positives, while genuinely critical threats get delayed or missed. CyberSilo Agentic SOC AI addresses this at the root by autonomously handling Level 1 and Level 2 triage, so analysts dedicate their expertise exclusively to complex, high-confidence threats.
The difference is measurable: 30% reduction in false positives reaching analyst queues, 50% faster MTTR on triaged incidents, and the ability to scale SOC capacity without linear headcount growth. See how CyberSilo ranks against competitors in the independent top 10 Agentic SOC AI platforms comparison, or explore how Agentic SOC AI integrates with ThreatHawk SIEM for a complete autonomous detection and response stack.
30%
Reduction in False Positive Alerts
50%
Faster Mean Time to Respond
30%
Smaller SOC Team Needed for L1–L2
24/7
Autonomous Monitoring — No Shift Gaps
Traditional SOC vs CyberSilo Agentic SOC AI
Traditional SOC
Agentic SOC AI
Manual alert triage — each alert reviewed individually
VS
AI-autonomous triage — correlated incidents, not raw alerts
Rule-based detection — misses novel attack patterns
VS
Behavioral ML — detects zero-day anomalies in real time
Manual playbook execution — analyst-dependent response
VS
Autonomous playbooks — response executes in minutes
High false positive rate — analyst fatigue and missed threats
VS
30% fewer false positives — analysts act on real threats
Shift-dependent — coverage gaps at night and weekends
VS
24/7 autonomous — no shift gaps, no coverage degradation
High headcount cost — scales linearly with alert volume
VS
30% smaller L1–L2 team — AI handles volume growth