PISF vs ISO 27001 vs NIST: What Pakistani CISOs Need to Decide Now

Pakistani organizations face an immediate operational decision: adopt PISF as the national baseline, pursue ISO 27001 certification for international assurance, or align with NIST controls for detailed technical maturity. The choice is not academic — it shapes logging, monitoring, SOC design, evidence collection, and the security tooling roadmap. This comparison focuses on operational impact: what each framework demands from your SIEM, how they change SOC workflows, and how to eliminate cyber silos so detection and response are measurable, automated, and auditable. If your objective is both regulatory compliance and a live security posture, you need an implementation path that maps controls to telemetry, reduces MTTD, cuts MTTR, and produces defensible evidence for audits. Threat Hawk SIEM, built and operated by CyberSilo for enterprise SOCs, was designed to meet those exact demands across on-prem, hybrid, and cloud estates.
How Cyber Silos Form in Modern Pakistani Environments
Cyber silos are not a product of malice; they are the consequence of organizational growth, technology heterogeneity, and uneven risk prioritization. In Pakistan, typical contributors are:
- Shadow IT and cloud adoption without central logging policies — separate teams spin up services with local monitoring, causing telemetry fragmentation.
- Procured point products for specific problems (EDR, firewall, DLP) that forward alerts but not normalized logs, producing duplicated or missing signals.
- Organizational silos — legal, HR, OT, and development units maintain separate security responsibilities and tooling, creating gaps in cross-domain correlation.
- Compliance-driven paperwork without operational integration — controls get documented, but evidence (logs, alerts, incidents) is scattered or inaccessible.
- Resource constraints leading to minimal retention, limited parsing, and disabled telemetry due to ingestion cost concerns.
The result: inconsistent telemetry, alert fatigue in the SOC, and long detection chains where correlation across identity, network, endpoint, and cloud is manual or impossible. The damage is measurable in MTTD and MTTR and in the organization's inability to present tamper-evident evidence during audits or regulatory inquiries.
Why Fragmented Security Tooling Fails at Scale
Pakistan Information Security Framework (PISF 2025)
Official PISF 2025 framework document — complete control matrix, compliance requirements, and implementation guidelines for Pakistani organisations. Free to download.
Download PISF 2025 PDFFragmentation undermines detection fidelity and response speed. Operationally, broken toolchains create three primary failure modes:
- Blind spots — when logs are not ingested, detection rules cannot cover an attack surface area. Missing visibility into cloud workloads or legacy network devices is common in hybrid Pakistani infrastructures.
- Context starvation — an endpoint alert without corresponding network flows, identity logs, or application telemetry is hard to prioritize and remediate. Analysts spend hours hunting context rather than resolving incidents.
- alert overload and fatigue — multiple tools generate overlapping alerts with different severity scales and inconsistent scoring. SOC analysts waste cycles reconciling vendor noise rather than focusing on high-confidence incidents.
These failure modes increase operational cost and risk: longer mean time to detect (MTTD), slower mean time to respond (MTTR), higher false positive rates, and reduced SOC throughput. A centralized SIEM that performs real-time correlation and normalization is the only practical way to scale detection, reduce noise, and provide auditable evidence for compliance frameworks.
Eliminate Cyber Silos with Threat Hawk SIEM
Discover how centralized visibility and real-time correlation can transform your SOC operations and compliance readiness.
Explore Threat Hawk SIEMPISF ISO Comparison, NIST Pakistan: Framework Differences That Matter to Operations
High-level descriptions of PISF, ISO 27001, and NIST are plentiful; the operational differentiators are what govern your SIEM design, SOC staffing, and program cadence. Below is a practical comparison focused on controls, evidence, and SOC implications.
PISF — National Focus, Regulatory Alignment
PISF (Pakistan Information Security Framework) is oriented to national needs and regulatory alignment. Its strengths for Pakistani organizations are explicit alignment with local privacy and government requirements, and prescriptive expectations for critical sectors such as finance, telecom, and government agencies. Operational implications:
- Specific logging and retention expectations may be mandated by sectoral regulators; SIEM must support configurable retention and export formats for audits.
- Control sets prioritize threat detection for national threat vectors and critical infrastructure; this requires SOC playbooks tuned to local TTPs.
- Evidence that regulators expect often includes tamper-evident logs, chain-of-custody controls, and timely incident reporting; your SIEM must provide immutable storage and verifiable audit trails.

ISO 27001 — Management System and Certification Focus
ISO 27001 defines an Information Security Management System (ISMS) with Annex A providing a control catalogue. Its strengths are auditability and certification, making it attractive for organizations doing business internationally. Operational implications:
- ISO demands documented processes, risk assessments, continuous monitoring, and evidence of control operation — SIEM-generated reports and dashboards become central artifacts for audits.
- Annex A controls map to monitoring activities (access logging, cryptography, incident management) and typically require proof of control testing and improvement cycles; the SIEM must support scheduled evidence exports and control dashboards.
- Certification requires continuous improvement; detection engineering must be part of the ISMS lifecycle with measurable KPIs that SOC leadership reports to senior management.
NIST (CSF and SP 800-series) — Technical Depth and Mappings
NIST provides both high-level frameworks (CSF) and detailed controls (SP 800-53, 800-171). It is prescriptive on technical controls and widely used to raise technical maturity. Operational implications:
- NIST emphasizes control implementation and measurement; SIEM plays a role in Identify, Detect, and Respond functions of NIST CSF, requiring fine-grained telemetry and behavior analytics.
- NIST control objectives often map directly to detection logic (e.g., logging for privileged access, multi-factor authentication events, audit transitions). Your SIEM must provide field-level coverage and correlation rules tied to those controls.
- NIST supports profile-based maturity mapping — use this to drive SOC capabilities from basic log collection to advanced UEBA and automated response.
Control Coverage and Assurance Model — Practical Mapping
Map controls to telemetry and proof. For every control you intend to claim, define:
- Required telemetry types (auth logs, network flows, EDR trace, cloud API events, application logs).
- Required retention and integrity mechanisms (WORM, checksums, encryption).
- Evidence artifacts: dashboards, incident timelines, playbook execution logs, and audit exports.
Threat Hawk SIEM supports prebuilt control mappings for ISO Annex A, NIST CSF categories, and PISF control sets so that SOC teams can trace each control to live telemetry, analytical detections, and incident evidence.
Framework Comparison Table
Download Official Framework Documents
PISF 2025 aur NCERT dono frameworks free download karein — compliance, audits, aur implementation planning ke liye.
PISF 2025
Pakistan Information Security Framework — complete control matrix & compliance guidelines
Download PISF PDFNCERT Framework
National Cyber Emergency Response Team — incident response procedures & reporting templates
Download NCERT PDF| Framework | Primary Focus | Operational Implications | Best For |
|---|---|---|---|
| PISF | National regulatory alignment for Pakistani organizations | Requires tamper-evident logs, local TTP detections, sectoral compliance reporting | Finance, telecom, government agencies in Pakistan |
| ISO 27001 | Information Security Management System (ISMS) certification | Demands documented processes, continuous monitoring, scheduled evidence exports | International business, certification requirements |
| NIST (CSF/800-series) | Technical depth and maturity scaling | Field-level telemetry coverage, behavior analytics, profile-based maturity mapping | Technical maturity, detailed control implementation |
SIEM as the Operational Bridge Between Frameworks
Frameworks define what you must do; SIEM defines how you do it operationally. A modern SIEM performs four critical functions in a compliance context:
- Log aggregation and normalization — bringing disparate telemetry into a common schema for search, analytics, and reporting.
- Real-time cross-domain correlation — producing high-confidence detections that map directly to controls and reduce false positives.
- Automation and orchestration — executing playbooks for containment, evidence capture, notification, and post-incident reporting.
- Compliance reporting and evidence packaging — generating auditable records aligned to framework requirements.
Without a SIEM that is architected to support control mapping and evidence generation, compliance becomes a repetitive manual exercise that burdens SOC analysts and increases audit risk.
Log Ingestion and Normalization — The Technical Foundation
Operationally, successful framework alignment begins with telemetry. The SIEM must ingest logs from:
- Network devices (firewalls, IDS/IPS, load balancers) — usually via syslog or NetFlow/IPFIX.
- Endpoints — EDR telemetry, Windows Event Log (WEC/Winevent), macOS/Linux logs.
- Cloud services — AWS CloudTrail, Azure Activity Logs, GCP audit logs via API or streaming.
- Applications and databases — JSON, audit tables, JDBC connectors.
- Identity systems — AD logs, LDAP, SSO providers, IAM activity.
Normalization means mapping disparate fields into a canonical schema (timestamp, source, destination, user, action, outcome, context). This enables correlation rules and analytics to work reliably across domains. Time synchronization, timezone normalization, and consistent event IDs are core operational requirements. Threat Hawk SIEM deploys parsing pipelines that convert vendor-specific formats into a unified schema with metadata tags that map to framework control IDs.
Cross-Domain Correlation and Real-Time Analytics
Correlation transforms data into actionable detections. Practical techniques include:
- Rule-based correlation — deterministic rules for known TTPs, mapped to control outcomes (e.g., multiple failed LDAP binds followed by successful privileged change).
- Entity-centric timelines — building user and asset histories that reveal anomalous sequences across time and environments.
- Statistical baselining and anomaly detection — identifying deviations from established behavior for users, services, and endpoints.
- Threat intelligence integration — enriching events with CTI to raise confidence levels and prioritize response.
Well-implemented correlation reduces MTTD by generating high-fidelity incidents that the SOC can investigate and resolve quickly. Threat Hawk's analytics combine deterministic detections with UEBA and CTI enrichment to reduce false positives and surface the incidents that matter most to compliance and risk reduction.
Build Your Custom Compliance Roadmap
Get expert guidance on aligning your SOC capabilities with PISF, ISO 27001, and NIST requirements tailored to your environment.
Contact Our Security Team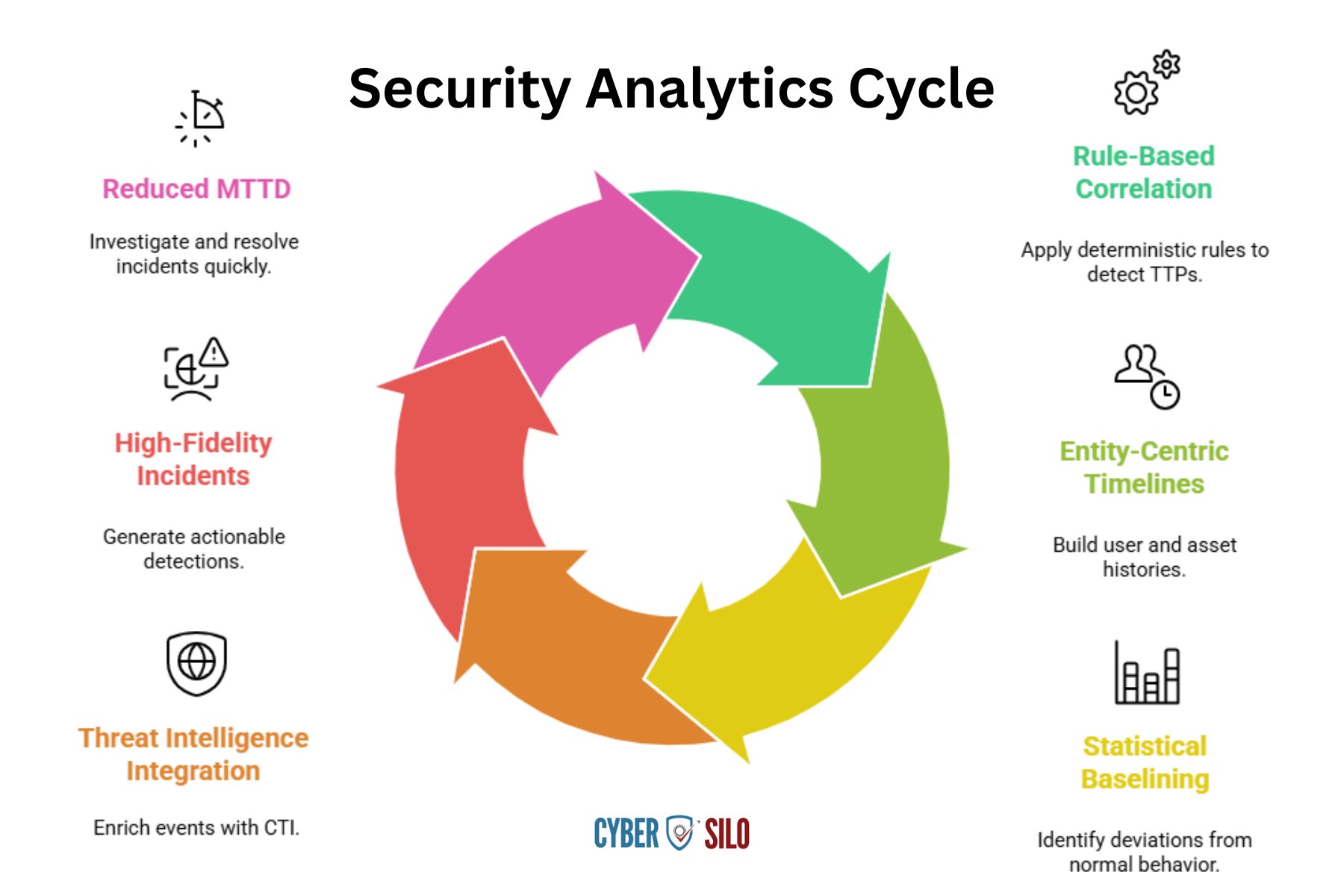
Automation, Orchestration, and Reducing MTTR
Speed is an audit artifact. Frameworks expect not just detection but demonstrable response capabilities. Automation and orchestration deliver repeatable, auditable response actions:
- Automated enrichment — appending asset owner, risk rating, vulnerability data, and past incidents to speed triage.
- Conditional playbooks — automated containment steps based on severity and impact (block IP, isolate host, disable account) with logged approvals where required by policy.
- Evidence capture — automated packaging of relevant logs, forensic snapshots, and timeline exports for post-incident review and audits.
These actions reduce MTTR by minimizing analyst-driven manual tasks and ensuring every response produces auditable records that map back to framework incident response requirements.
Operational Metrics That Matter to Both SOCs and Auditors
National Cyber Emergency Response Team (NCERT) Framework
Complete NCERT incident response framework — procedures, reporting templates, and coordination guidelines for critical infrastructure operators in Pakistan.
Download NCERT Framework PDF| Metric | Description | Purpose |
|---|---|---|
| MTTD (Mean Time to Detect) | Target measurable reductions after SIEM tuning and correlation rules are deployed | Demonstrates detection effectiveness and continuous improvement |
| MTTR (Mean Time to Respond) | Track time to containment and full remediation after detection | Shows response capability and operational efficiency |
| Alert Triage Time | Average time an analyst spends to validate a detection | Measures automation impact on SOC productivity |
| False Positive Rate | Percentage of alerts that do not represent genuine incidents | Indicates detection quality and tuning effectiveness |
| Control Coverage Rate | Percentage of defined controls that have verifiable telemetry mapped in the SIEM | Audit evidence of framework compliance implementation |
These metrics are not just operational KPIs; they form the evidence base for audits and demonstrate the ISMS or security program is functioning as designed.
Implementing Threat Hawk SIEM for PISF, ISO 27001, and NIST Compliance
Threat Hawk SIEM from CyberSilo is built with SOC operations and compliance integration at its core. Its design addresses the operational needs identified above:
- Elimination of cyber silos via centralized visibility: unified ingestion pipelines and a canonical event schema unify telemetry across on-prem, hybrid, and cloud.
- Real-time log correlation and threat detection accuracy: layered analytics combining deterministic rules, UEBA, and CTI reduce false positives and shorten MTTD.
- SOC efficiency gains: automated enrichment, role-based workflows, and playbook-driven orchestration cut analyst time per incident and materially improve MTTR.
- Compliance readiness: prebuilt mappings to ISO Annex A, NIST CSF categories, and PISF controls with exportable evidence packages and tamper-evident log storage.
- Scalability: elastic ingestion, hot and cold storage tiers, and multi-tenant architectures that match enterprise scale and retention policies without compromising performance.
Threat Hawk's SIEM comes with detection libraries and playbooks designed for the region, including local threat TTPs and regulatory reporting formats required by Pakistani sectors. This operational alignment reduces the time between framework selection and demonstrable compliance.
Practical Deployment Architecture
A recommended enterprise deployment pattern for Pakistani organizations includes:
- Distributed collectors — lightweight agents or aggregator nodes near data sources to minimize log loss and maintain performance for high-throughput systems.
- Central ingestion and parsing pipeline — canonical schema transformation with enrichment layers for asset context, vulnerability data, and identity mapping.
- Indexing and search tiers — hot storage for recent data with fast search for investigations and cold storage for long-term retention and forensic access.
- RBAC and encryption — strict role separation, KMS-backed encryption at rest, TLS for transport, and field-level redaction where privacy requires it.
- High availability and disaster recovery — redundant collectors, replicated indices, and defined RTO/RPO aligned to business continuity requirements.
- Integration fabric — connectors to EDR, IAM, cloud APIs, ticketing, and orchestration systems for end-to-end SOC workflows.
Threat Hawk is designed to fit this pattern, with hardened deployment templates for on-prem, hybrid, and public cloud infrastructural models commonly found in Pakistani enterprises.
Use Case Examples: Translating Detections Into Framework Evidence
Three short use cases illustrate how SIEM-driven detections translate to compliant operations:
- Privileged account misuse: Correlate AD logs, VPN session records, EDR elevation events, and privileged access requests. Detection triggers a high-confidence incident, which invokes a playbook that captures a forensic snapshot, disables the account, notifies governance, and produces an audit export that links each action to a specific control in ISO, NIST, or PISF.
- Cloud lateral movement: Combine CloudTrail events, VPC Flow Logs, and API activity to flag abnormal cross-account accesses. Automated containment isolates the affected workload, and the SIEM packages the timeline and log evidence to satisfy regulatory reporting obligations.
- Payment environment fraud attempt: Cross-correlate web application firewall logs, transaction anomalies, and endpoint telemetry to detect and block a fraudulent transaction path. The incident timeline, detection rule versions, and remediation steps are archived for auditor review.
Each use case demonstrates how a SIEM reduces time-to-detect and time-to-respond while creating auditable evidence aligned to framework expectations.
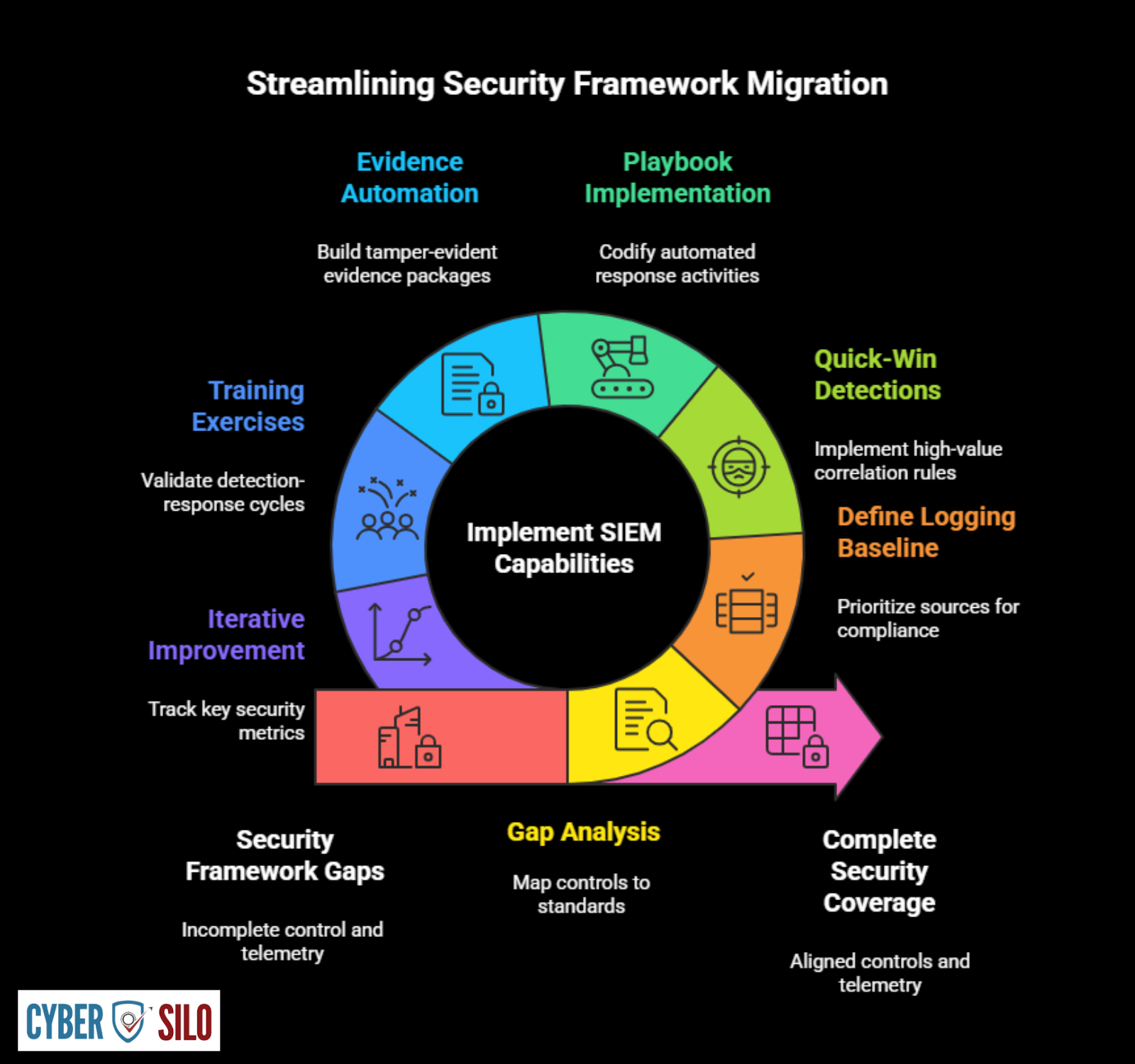
Migration and Mapping Strategy: Practical Steps for Pakistani Enterprises
Pakistan Information Security Framework (PISF 2025)
Official PISF 2025 framework document — complete control matrix, compliance requirements, and implementation guidelines for Pakistani organisations. Free to download.
Download PISF 2025 PDFMoving from one framework to another, or aligning multiple frameworks, requires a disciplined approach that centers SIEM capabilities. A prioritized roadmap looks like this:
- Gap analysis and control mapping — map current controls and telemetry to PISF, ISO, and NIST control sets to identify coverage and gaps.
- Define logging baseline — required sources, fields, retention, and integrity mechanisms; prioritize sources that close the largest compliance gaps first.
- Quick-win detections — implement high-value correlation rules (privileged misuse, lateral movement, exfil patterns) that significantly reduce MTTD.
- Playbook implementation — codify automated response activities for top incident types and enforce evidence capture for each playbook execution.
- Evidence automation — build exportable, tamper-evident evidence packages for auditors that include control mapping, detection logic versions, and playbook execution logs.
- Training and tabletop exercises — validate detection-response cycles against realistic scenarios and refine playbooks and reports based on outcomes.
- Iterative improvement and measurement — track control coverage rates, MTTD, MTTR, and false positive rates; make detection engineering a recurring resource allocation.
Common Pitfalls and How to Avoid Them
Organisations commonly stumble on:
- Collecting too much without normalization — costly storage and analysis overhead without usable signals. Remedy: define a logging baseline with field-level priorities and selective enrichment.
- Under-collecting critical telemetry — missing the one data source that would link an alert to a control. Remedy: use the gap analysis phase to prioritize the most impactful sources.
- Ineffective tuning — leaving generic vendor rules active creates noise. Remedy: invest in detection engineering and tune rules to your environment and threat model.
- Ignoring privacy and data sovereignty — improper handling of personal data that violates local laws. Remedy: deploy field-level redaction and regionally compliant storage tiers.
Compliance Operations Playbook for Pakistani CISOs
A concise operational playbook to align SIEM and SOC with PISF, ISO 27001, and NIST:
- Governance: assign control owners and ensure ISMS integration with SOC governance. Map each control to SIEM artifacts and owners.
- Telemetry Strategy: implement a phased ingestion plan starting with identity, network, and critical applications. Establish retention and tamper-evidence policies.
- Detection Engineering: prioritize top 20 detections that reduce risk fastest, tune, and onboard into the SIEM with test datasets.
- Playbooks: implement automated and human-in-the-loop playbooks for common incidents with audit logs and evidence packaging.
- Reporting: build dashboards that map controls to live telemetry and generate evidence exports for auditors and regulators.
- Continuous Improvement: schedule quarterly control reviews, detection tuning cycles, and yearly tabletop exercises aligned to regulatory reporting windows.
Accelerate Your Framework Compliance Journey
Learn how the right SIEM solution can help you meet PISF, ISO 27001, and NIST requirements while improving your security posture.
Explore Top SIEM ToolsConclusion — Choosing the Right Path and Operational Partner
For Pakistani organizations, the decision among PISF, ISO 27001, and NIST should be driven by business objectives and operational realities. PISF offers national regulatory alignment, ISO 27001 delivers certification and international trust, and NIST provides technical depth for maturity scaling. Regardless of framework choice, the operational backbone of a compliant security program is a SIEM that unifies telemetry, correlation, automation, and evidence management.
CyberSilo's Threat Hawk SIEM is purpose-built to eliminate cyber silos, centralize visibility, and deliver real-time log correlation and detection accuracy at enterprise scale. It integrates across on-prem, hybrid, and cloud deployments to improve SOC efficiency, reduce MTTD, shorten MTTR, and produce auditable evidence for PISF, ISO, and NIST alignment. If your leadership needs a pragmatic path from framework selection to measurable security outcomes, consider a structured engagement to build a Custom Compliance Roadmap tailored to your environment. The roadmap will prioritize telemetry, map controls to detections, design playbooks for automated response, and define metrics that demonstrate risk reduction and security maturity progression.
Contact CyberSilo to start a Custom Compliance Roadmap that aligns operational SOC capability with PISF, ISO 27001, and NIST requirements — reducing detection time, improving response, and delivering the evidence auditors and regulators expect. Learn more about our mission and join our upcoming educational sessions at our webinars page.







