PISF Essential System & Communication Protection: Implementation Guide
Immediate problem: enterprises implementing PISF "System & Communication Protection" controls routinely struggle to convert policy language into operational, measurable defenses. Gaps appear as inconsistent host hardening, fragmented TLS controls, unmanaged east-west traffic, and disconnected logs across on-prem, hybrid, and cloud estates. Those gaps enable lateral movement, data exfiltration, and compliance failures. This guide maps PISF control objectives to concrete architectural patterns, controls, and SIEM-driven operations so security teams can implement scalable system protection PISF measures and robust network security controls that reduce MTTD, MTTR, and audit friction.
System Protection PISF: Objectives and Operational Priorities
PISF system protection focuses on preventing unauthorized change or access to systems, ensuring integrity of communications, and enabling detection and response across the entire environment. Operational priorities derived from those objectives are:
- Establish a single source of truth for security telemetry (log aggregation and normalization).
- Enforce consistent baselines and configurations (CMDB, baselines, automated remediation).
- Control and monitor privileged access and administrative channels.
- Protect confidentiality and integrity of communications (encryption, PKI, TLS policy).
- Detect cross-domain attacks through correlation (host + network + identity + cloud).
- Provide auditable evidence and automated reporting for PISF compliance monitoring.
Threat Model Implications
System protection failures are most consequential when an attacker reaches a foothold and leverages weak communication controls to move laterally or exfiltrate data. Prioritize controls that: (1) harden endpoints to stop initial compromise, (2) make lateral movement expensive via segmentation and flow visibility, and (3) deliver high-fidelity signals into the SOC through centralized telemetry so correlation rules can detect the attack chain early. Threat Hawk SIEM is purpose-built to surface these signals across every environment layer.
See How Threat Hawk SIEM Eliminates Cyber Silos
Centralized visibility, real-time log correlation, and SOC-focused automation — purpose-built for PISF compliance and cross-domain threat detection.
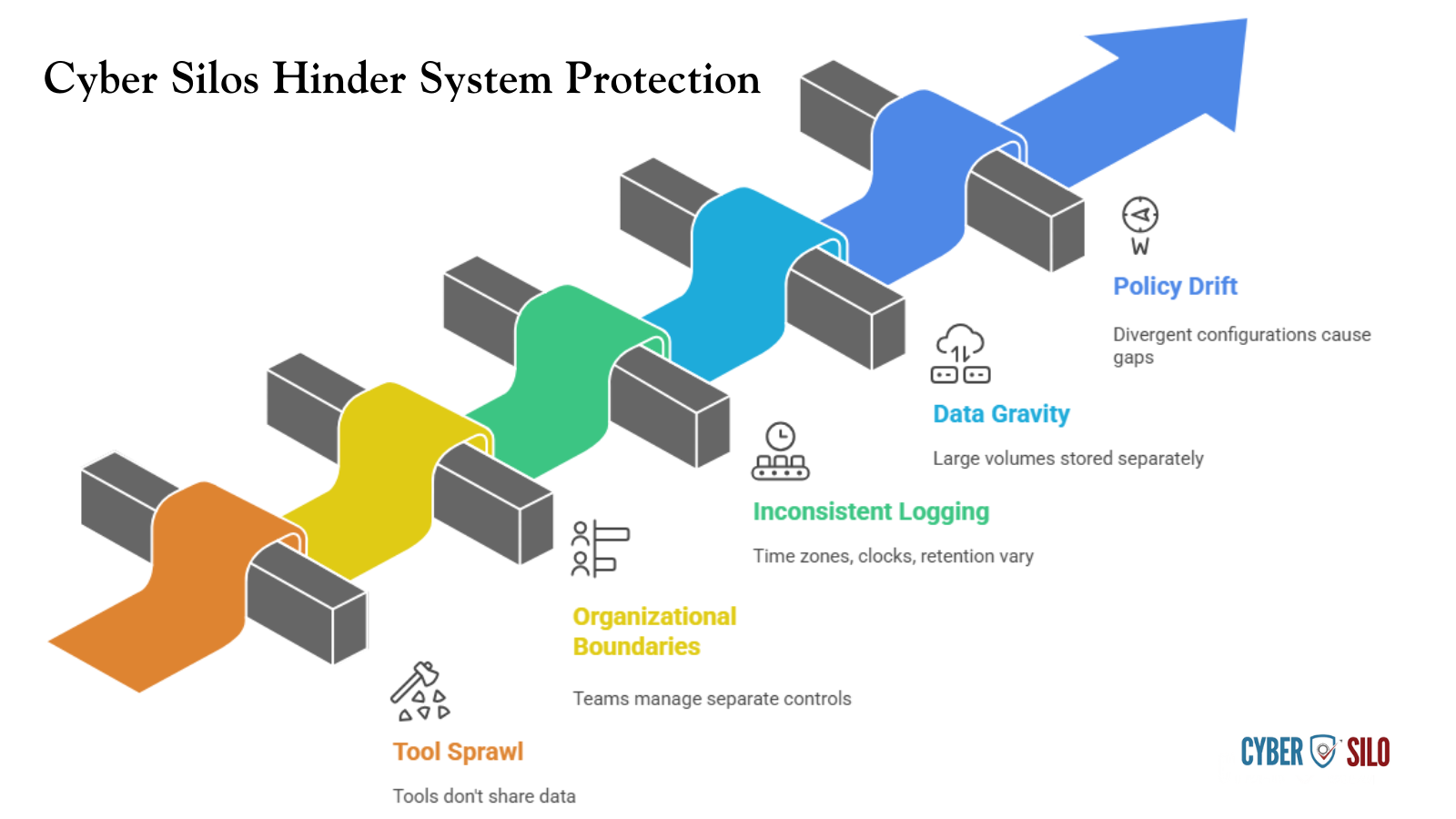
Why System Protection Fails at Scale: How Cyber Silos Form
Cyber silos form when tooling, teams, and telemetry are fragmented. Common patterns include:
- Tool sprawl: multiple endpoint agents, cloud-native tools, network appliances, and point solutions that don't share logs or contextual metadata.
- Organizational boundaries: infrastructure teams manage network controls, application teams own app logs, security teams get limited visibility or inconsistent data formats.
- Inconsistent logging: different time zones, unsynchronized clocks, and varied retention policies degrade correlation accuracy.
- Data gravity: large telemetry volumes stored separately (cloud vs. on-prem) without a single, centralized index for searching and correlation.
- Policy drift: divergent configuration baselines across OS versions and cloud regions cause protection gaps.
These silos lead to alert fatigue, missed context during triage, and long dwell times. The corrective path is architectural: unify telemetry ingestion, enforce a common data model, and orchestrate automated workflows to operationalize PISF controls. Explore the top 10 SIEM tools to understand how platforms compare on silo elimination.
Key PISF System & Communication Protection Controls and Technical Mapping
This section maps PISF control requirements to concrete technical controls and operational practices. Each control is followed by the telemetry the SOC must collect and how the SIEM should use it.
Endpoint Hardening and Integrity
- Controls: secure baselines, application allowlisting/whitelisting, full-disk encryption, secure boot, TPM attestation, EDR with behavioral detection.
- Telemetry: EDR process creation, driver loads, binary hashes, Windows Security Event logs (4624/4625/4688/4689), Linux auditd events, BitLocker/cryptsetup status.
- SIEM use: normalize process creation events, enrich with hash reputation and asset criticality, trigger high-confidence alerts when unapproved binaries execute on critical hosts.
Patch and Configuration Management
- Controls: prioritized patching by asset criticality, configuration drift detection, automated remediation for known vulnerabilities.
- Telemetry: CMDB records, vulnerability scanner results, configuration management tool logs (Chef/Ansible), OS patch logs.
- SIEM use: correlate vulnerability scan exceptions with exploit attempts and EDR alerts to raise priority incidents.
Privileged Access and Session Protection
- Controls: least privilege, MFA for admin access, just-in-time (JIT) privilege elevation, bastion hosts, privileged session recording.
- Telemetry: PAM logs, authentication logs, MFA assertions, bastion session recordings, sudo/audit events.
- SIEM use: detect anomalous privilege elevation, concurrent sessions, or privilege use outside approved windows; automate session termination when risk thresholds exceed policy.
Network Security Controls
- Controls: segmentation (VLANs, microsegmentation), NGFW with threat signatures, IDS/IPS, encrypted tunnels (IPsec), ZTNA for remote access, DNS security, email controls.
- Telemetry: firewall allow/deny logs, NetFlow/IPFIX, IDS alerts, proxy and web gateway logs, VPN concentrator logs, DNS query/response logs.
- SIEM use: perform cross-correlation — e.g., low-volume data exfil combined with DNS tunneling patterns and anomalous TLS sessions should escalate immediately. See how leading SIEM platforms handle cross-domain network correlation.
Encryption and Communication Integrity
- Controls: organizational TLS policies, cipher suites and protocol version enforcement, PKI lifecycle management, perfect forward secrecy, secure service-to-service mTLS in microservices.
- Telemetry: TLS handshake metadata (cipher, SNI, cert chain), PKI issuance logs, OCSP/CRL checks, mTLS authentication events.
- SIEM use: flag expired or weak certificates, unexpected self-signed certs, or services reverting to deprecated cipher suites; couple with asset owner data to automate renewal workflows.
Data Loss Prevention and Exfiltration Controls
- Controls: egress controls, DLP at endpoints and gateways, content inspection, behavioral analytics on data transfers.
- Telemetry: DLP incidents, large file transfers from endpoints, cloud storage audit logs, anomalous S3 API calls, email attachments and headers.
- SIEM use: correlate DLP events with identity anomalies and unusual network flows to establish exfiltration timelines and automate containment.
Explore Our Upcoming PISF & SIEM Webinars
Join CyberSilo security engineers for live sessions on implementing cross-domain correlation, automating PISF compliance evidence, and tuning detection rules to reduce false positives. Practical, hands-on, and free to attend.
Log Ingestion, Normalization, and Cross-Domain Correlation
Effective system protection PISF implementation depends on a precise telemetry pipeline. A robust pipeline ensures the SOC can connect indicator events across host, network, identity, and cloud domains.
Ingestion Architecture
- Agents vs. agentless: use lightweight agents where low-latency host telemetry is required (EDR, endpoint syslogs); use syslog collectors and cloud-native APIs for appliances and SaaS.
- Network taps and flow collection: deploy TAPs or SPAN ports, collect NetFlow/IPFIX, and keep selective packet capture for high-risk segments.
- Time synchronization and integrity: enforce NTP across environments; sign logs where legal/regulatory requirements demand non-repudiation.
Normalization and Common Schema
Create a canonical data model that standardizes fields such as timestamp, source/destination IP, username, asset ID, process hash, event severity, and correlation IDs. Normalization enables deterministic correlation, faster searches, and reusable detection logic. Typical parsing tasks include extracting SIDs and UIDs, canonicalizing IPv6/IPv4 addresses, and normalizing user identity across LDAP, SAML, and cloud identity providers.
Cross-Domain Correlation Strategies
- Enrich logs with CMDB and asset criticality so correlation rules can weigh signals based on business impact.
- Use identity as the glue: tie host events to user directory attributes and cloud identity tokens to build a complete incident timeline.
- Chain events across stages: reconnaissance (scanning logs) → initial compromise (phishing/mail logs + EDR) → lateral movement (SMB, RDP logs + NetFlow) → persistence (scheduled tasks, registry writes).
Real-Time Analytics, Automation, and Reducing Alert Fatigue
Reducing alert fatigue while improving detection accuracy requires layered analytics — rule-based correlation, behavioral analytics, and threat intelligence fusion — plus automation that takes low-risk actions without human intervention.
Detection Engineering Principles
- High-fidelity signals: prefer detections combining multiple telemetry types (e.g., firewall allow to rare external IP + anomalous process spawn + identity risk) to increase precision.
- Use scoring rather than binary alerts: assign contextual risk scores from 0–100 for each event and trigger incidents only when cumulative risk crosses thresholds.
- Statistical baselining: build per-asset and per-user baselines for typical activity; treat deviations as signals rather than immediate alerts.
Orchestration and Automated Containment
SOAR playbooks should automate common containment steps: block IP on NGFW, quarantine endpoint via EDR, revoke risky sessions, and open incident tickets with pre-populated evidence. Automation must include safety nets: execute low-impact automated tasks first, escalate to human operators for broader changes, and provide one-click rollback in case of false positives.
How SIEM Unifies Detection, Response, and Governance
SIEM is the integrator: collecting telemetry, enabling cross-domain correlation, and providing the SOC with searchable context and automated workflows. A mature SIEM reduces MTTD by surfacing correlated attack patterns, and reduces MTTR by pre-building containment playbooks and evidence packaging. Review the top 10 SIEM tools to benchmark platform capabilities against your requirements.

Operational Role of Threat Hawk SIEM
Threat Hawk SIEM from CyberSilo is designed to eliminate cyber silos through centralized visibility, real-time log correlation, and SOC-focused operational features. Key capabilities to prioritize in implementation:
- Unified ingestion across on-prem, cloud, and hybrid sources with native parsers and API connectors.
- Real-time correlation engine that supports cross-domain chain detection and scoring to reduce false positives.
- Integrated SOAR for automated containment workflows and case management, reducing manual follow-up.
- Compliance-ready reporting templates, audit trails, and evidence export designed for PISF mapping.
- Scalable storage tiers and indexing strategies to meet retention SLAs without sacrificing query performance.
Reducing MTTD and MTTR With Correlated Telemetry
Example: correlating an EDR fileless execution detection (host) with a spike in DNS NXDOMAIN responses (network) and a cloud IAM policy change event (cloud) can convert three single-discipline alerts into a single high-severity incident. That conversion reduces triage time and prevents analyst time wasted on separate tickets. Threat Hawk's correlation graphs and enrichment reduce the mean time to detection (MTTD) and mean time to respond (MTTR) by streamlining the SOC's investigative path.
Operationalizing SOC Workflows: Detection to Remediation
Translate controls into operational workflows that the SOC executes daily. Each workflow must define inputs, enrichment sources, decision points, remediation actions, and audit artifacts.
Triage and Escalation
- Tier 1: automated enrichment and suppression — combine contextual data and apply suppressions for known benign activity.
- Tier 2: human investigation — use correlation timelines and session recordings for rapid root-cause analysis.
- Tier 3: incident response — execute containment automation and invoke incident commanders for potential breaches.
Playbooks and Evidence Collection
Playbooks should list required artifacts: process execution chain, network flows, host forensic snapshot, authentication logs, and privileged session recordings. Store artifacts in the SIEM case with cryptographic integrity checks to satisfy PISF audit demands and legal preservation requirements.
Avoiding and Resolving Cyber Silos: Practical Governance and Architecture
Technical fixes alone will not dissolve silos. Governance, operational agreements, and data ownership are equally important.
Governance and SLAs
- Define ingestion SLAs for each data owner (latency, format, retention).
- Establish a data catalog and data stewardship roles for telemetry producers.
- Mandate a canonical log schema and version it; require new tooling to ship with compatible connectors.
Integration Roadmap
- Phase 1: ingest critical telemetry (EDR, firewall, AD, cloud audit logs).
- Phase 2: expand to network flows, proxy logs, email gateways, and DLP.
- Phase 3: full enrichment with CMDB, vulnerability feeds, and business context.
Operationally, maintain an integration backlog with estimated effort and priority based on asset criticality and risk. Contact our security team to assess your current telemetry gaps and build a prioritized integration plan.
Data Lifecycle, Storage and Cost-Efficient Indexing
Design retention tiers aligned to PISF requirements and forensic needs. Typical architecture:
Apply selective indexing — index metadata for all logs but only full-text index event types required for investigations. Encrypt data at rest and in transit, and maintain key rotation policies aligned with PKI and PISF mandates.
Compliance Mapping: What Auditors Will Look For and How to Produce Evidence
Auditors will want to see both control implementation and proof the controls are working. Produce evidence that ties controls to telemetry and processes:
- Configuration baselines and change logs showing applied hardening.
- Patch reports linked to vulnerability scanner findings and remediation tickets.
- PAM logs and session recordings demonstrating privileged access controls.
- TLS and PKI reports showing certificate expirations and renewals.
- SIEM-generated incident reports and timelines with attached raw logs and hashes for chain-of-custody.
- Retention policy documentation and storage architecture showing how logs are protected and archived.
Threat Hawk SIEM provides built-in compliance templates and automated evidence packaging to speed audits and reduce manual evidence collection time.
Implementation Roadmap and Checklist
A phased approach reduces risk and builds momentum. Suggested timeline for enterprise-scale implementation (6–12 months depending on org size):
Phase 0 — Assessment (Weeks 0–4)
- Inventory critical assets, telemetry sources, and existing controls.
- Define PISF control mapping and prioritize based on business impact.
Phase 1 — Foundation (Weeks 4–12)
- Deploy centralized log collectors and time sync (NTP), onboard EDR, AD, NGFW logs.
- Implement CMDB and asset tagging for enrichment.
- Baseline configurations and apply hardened images for critical hosts.
Phase 2 — Detection and Response (Weeks 12–24)
- Develop initial correlation rules and automated playbooks for common incidents.
- Implement privileged access controls and session recording.
- Begin phased network segmentation and deploy NetFlow collection.
Phase 3 — Scale and Optimize (Months 6–12)
- Add cloud audit logs, SaaS connectors, DLP, and advanced analytics.
- Refine detection engineering, reduce false positives, implement tiered retention.
- Run tabletop exercises and continuously tune playbooks.
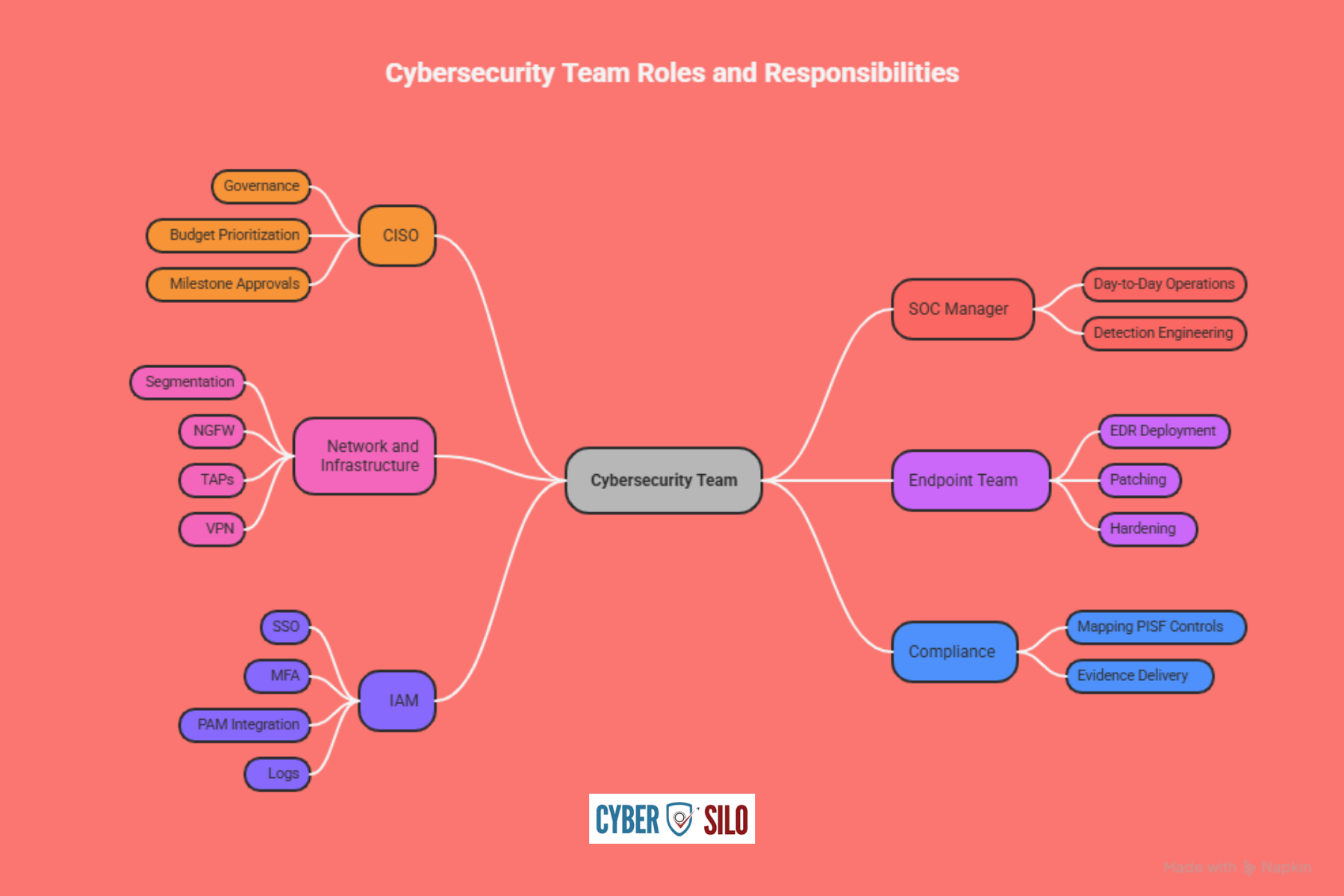
Roles and Responsibilities
- CISO: governance, budget prioritization, and milestone approvals.
- SOC Manager: day-to-day operations, detection engineering.
- Network and Infrastructure: segmentation, NGFW, TAPs, VPN.
- Endpoint Team: EDR deployment, patching, hardening.
- IAM: SSO, MFA, PAM integration and logs.
- Compliance: mapping PISF controls to evidence delivered by the SIEM.
Practical Detection Scenario: Credential Theft to Exfiltration
Walkthrough of how a well-instrumented environment detects and mitigates an attack chain:
- Initial signal: EDR flags anomalous PowerShell execution with encoded command and new parent-child process relationship. SIEM enriches with hash reputation and host criticality.
- Network correlation: NetFlow shows an unusual spike in outbound connections to a rare external IP; DNS logs show rapid subdomain generation (possible DNS tunneling).
- Identity correlation: AD logs reveal multiple failed authentications for the same account from different hosts, followed by a successful authentication from an unusual location. MFA logs show bypass or failed prompts.
- Automated action: SOAR playbook quarantines host, revokes user sessions, blocks the external IP on NGFW, and opens an incident with pre-populated artifacts.
- Investigation: SOC analyst reviews session recordings, EDR forensic snapshot, and SIEM timeline; root cause identified as credential reuse combined with delayed patching on a privileged admin host.
- Remediation and lessons learned: enforce MFA for all admin accounts, patch vulnerable host, rotate credentials, add a new correlation rule to detect similar patterns earlier.
That single chain demonstrates the value of cross-domain correlation and why system protection PISF controls must be backed by unified telemetry and automation. Watch our webinar on detection engineering to see this scenario replayed in a live environment.
Is Your SOC Ready to Detect a Credential Theft Chain?
Don't wait for a breach to find the gaps. Contact our security team for a complimentary PISF telemetry gap assessment and see exactly where your detection coverage falls short.
Conclusion: Turning PISF Requirements Into Operational Security
System protection PISF controls are achievable when organizations treat telemetry, governance, and automation as integrated disciplines rather than independent projects. The combination of consistent baselines, robust network security controls, and a SIEM platform that centralizes visibility and automates response changes security from reactive to proactive.
Threat Hawk SIEM provides the ingestion, correlation, SOAR, and compliance tooling required to stitch host, network, identity, and cloud signals into actionable incidents — eliminating cyber silos, improving detection accuracy, and shortening MTTD and MTTR.
If your priority is to convert PISF policy into measurable operational capability — improving SOC efficiency, reducing risk, and demonstrating compliance — schedule a TEM Demo to see CyberSilo's Threat Hawk applied to your telemetry. The demo focuses on how centralized correlation, automated playbooks, and compliance-ready reporting can accelerate your security maturity and reduce the time between compromise and containment.
Implementation Checklist (Quick Reference)
- Centralize log ingestion (EDR, FW, AD, cloud logs) and enforce NTP/clock sync.
- Normalize telemetry to a common schema and enrich with CMDB and identity context.
- Deploy prioritized endpoint hardening and EDR across critical hosts.
- Implement segmentation and collect NetFlow/packet captures for high-risk segments.
- Enforce TLS/PKI policies and monitor certificate lifecycle; log TLS metadata.
- Establish PAM, MFA, and session recording for privileged accounts.
- Build correlation rules that combine host, network, and identity signals; apply scoring to reduce false positives.
- Automate containment actions through SOAR with safety checks and rollback options.
- Define retention tiers aligned to PISF and ensure encryption at rest and in transit.
- Prepare compliance evidence packages and run regular tabletop exercises.







