If your charter is to deliver PISF 2025 compliance for an enterprise environment, this is not a theoretical exercise — it is an operational program that must close 38 specific, mandatory gaps across people, process, and technology. Below is a precise PISF compliance checklist and a detailed explanation of each mandatory control, focused on how a modern SIEM and mature SOC make these controls auditable, sustainable, and measurable.
How to Use This PISF Compliance Checklist
This PISF compliance checklist is organized to map directly to operational workstreams: governance, identity & access, endpoints, network, cloud, logging & SIEM, detection & response, vulnerability & change management, third-party risk, and continuity. For each mandatory control we explain what must be done, how to instrument it, which logs and telemetry matter, measurable outputs (MTTD/MTTR, coverage, false positive rate), and how Threat Hawk SIEM accelerates implementation and ongoing evidence collection.
PISF 2025 Compliance Checklist: 38 Mandatory Actions Explained
Governance, Policy & Auditability
1. Establish an Executive-Signed Security Policy Framework
Mandatory action: document and obtain executive sign-off on a security policy framework aligned to PISF requirements. Operationalize via policy automation and version control. Evidence: signed policies, policy change logs, roles mapped to policy owners. A central SIEM can ingest policy change events and provide immutable audit trails for compliance reviewers.
2. Maintain a Formal Risk Register with Acceptable Risk Decisions
Create and track a risk register with assigned owners, risk ratings, and risk acceptances. Integrate risk outputs into SOC prioritization and playbooks so compensating controls are clear. Threat Hawk SIEM can map prioritized risks to detection rules, ensuring high-risk areas have corresponding telemetry and alerting.
3. Appoint an Information Security Officer and Incident Commander
Designate and document roles with escalation matrices. Integrate role-based access within toolsets and log all role changes. SIEM correlation rules should generate alerts when critical role assignments change or when multiple role-based failures occur, feeding into incident response workflows.
Identity, Authentication & Access Controls
4. Enforce MFA on All Administrative and Remote Access
Mandate multi-factor authentication everywhere administrative or remote access exists. Monitor authentication telemetry for bypass attempts, failed MFA pushes, and anomalous MFA patterns. Ingestion of identity provider (IdP) logs into Threat Hawk SIEM enables real-time correlation between successful authentication, context, and subsequent privileged activity.
5. Least Privilege and Just-in-Time (JIT) Privileged Access
Implement least privilege across systems and JIT for high-risk access. Audit entitlement changes and JIT session logs. SIEM should correlate privilege elevations with asset criticality and unusual session behavior to reduce misuse window and assist investigators.
6. Centralize Identity and Access Logging
Centralize logs from AD/LDAP, cloud IdPs, SSO, PAM, and service accounts. Normalize identity fields for cross-system correlation. Proper normalization in Threat Hawk SIEM eliminates identity silos and supports account-centric detection.
Ready to Streamline Your PISF Compliance?
Discover how Threat Hawk SIEM can help you centralize logs, automate detections, and meet all 38 mandatory controls with ease.
Contact Our Security TeamEndpoint & Application Hardening
7. Deploy Endpoint Detection and Response (EDR) Across the Estate
EDR must be deployed to cover 100% of managed endpoints and critical servers. Collect process, file, registry, and network process telemetry. Correlate EDR indicators with network and authentication logs to differentiate malicious from benign activity and reduce alert fatigue.
8. Enforce Application Whitelisting for Critical Systems
Implement allow-listing where practicable. Log policy violations and blocked execution attempts. SIEM rules should escalate repeated allow-list violations tied to high-risk assets.
9. Secure Software Development Lifecycle (SSDLC) Controls
Mandate secure coding, code reviews, SCA (software composition analysis), and CI/CD pipeline security. Ingest CI/CD logs and SCA findings to central monitoring so newly introduced vulnerabilities or risky dependencies generate detection and change review workflows.
Network Controls & Segmentation
10. Enforce Network Segmentation and Zoning
Segment production, administrative, and user networks. Monitor cross-segment flows and abnormal lateral movement. Threat Hawk SIEM should aggregate flow and firewall logs to detect policy violations and microsegmentation bypass attempts.
11. Harden Perimeter and Egress Filtering
Implement strict egress controls and DNS filtering. Log and correlate DNS anomalies, proxy logs, and firewall egress events to detect data exfiltration and command-and-control behavior.
12. Continuous Network Telemetry and Flow Collection
Collect NetFlow/PCAP/telemetry for critical segments. Normalize flow fields and correlate with host events to identify stealthy lateral movement and beaconing that escapes signature-based controls.
Logging, SIEM & Data Retention
13. Centralize Log Aggregation with Defined Retention Policies
Mandate centralized ingestion for all critical log sources with retention aligned to PISF requirements. Define retention by class (auth logs, audit trails, flow). Threat Hawk SIEM supports tiered storage and immutable retention to satisfy audits.
14. Normalize and Enrich Logs at Ingestion
Standardize fields (timestamp, user, asset, geo, process) and enrich with asset-criticality and business owner metadata. Normalization ensures consistent cross-domain correlation and accurate alerting across hybrid environments.
15. Implement Immutable Audit Trails and Tamper Evidence
Ensure logs are write-once and tamper-evident. Use append-only storage, cryptographic hashing, or secure log-forwarding to centralized SIEM. Immutable trails are essential for forensic investigations and regulatory proof.
16. Define and Monitor Log Health and Coverage KPIs
Establish KPIs for log coverage, ingestion rates, parsing success, and gaps. Automate alerts for missing sources or drops. Threat Hawk SIEM's telemetry health dashboards reduce blind spots that invite compliance violations.
Threat Detection & Intelligence
17. Implement a Threat Model Aligned to Institutional Risk
Construct a tailored threat model and map it to detection requirements. Prioritize detections for likely adversary TTPs. Using the model, create use-case-driven correlation rules within the SIEM for focused MTTD improvements.
18. Centralize Threat Intelligence and Feeds
Ingest curated threat feeds, internal IOCs, and industry sharing (where permitted). Normalize threat intel data and apply scoring for automated enrichment of alerts. Threat Hawk SIEM integrates TI to cut false positives and speed triage.
19. Deploy Behavioral and Anomaly-Based Detections
Supplement signature rules with behavioral analytics that learn baselines for user and device behavior. Anomaly detection identifies novel attacks and supports early detection where conventional rules fail.
20. Maintain a Catalogue of Use Cases and Detection Rules
Document and version every detection use case, mapping it to log sources, false positive tuning, and validation tests. This catalogue is the audit artifact and operational playbook for the SOC team.
Alerting, Triage & SOC Operations
21. Define Alert Severity, Escalation and SLA Matrices
Standardize alert severities, response SLAs, and escalation paths. Map SLAs to incident types and integrate them into the SIEM workflows. Monitor SLA compliance and alert aging to lower MTTR.
22. Reduce Alert Fatigue Through Contextualization
Enrich alerts with asset criticality, business impact, risk scoring, and threat intelligence. Context-rich alerts reduce false positives and speed SOC decision-making. Use SIEM automation to suppress low-risk, repetitive alerts.
23. Implement Playbooks and SOAR Orchestration for Common Incidents
Formalize playbooks for containment, eradication, and recovery. Automate repeatable triage steps (isolation, enrichment, ticketing) to shorten MTTD and MTTR while preserving analyst oversight.
24. Establish Continuous SOC Training and Red-Blue Exercises
Run regular tabletop and live exercises tied to the detection catalogue. Capture lessons learned and refine detection rules and playbooks. Evidence of ongoing training is a compliance requirement and operational necessity.
Learn More About SIEM Best Practices
Explore our comprehensive guide on the top SIEM tools and discover which solution fits your enterprise security needs.
Read the SIEM Tools GuideIncident Response & Forensics
25. Maintain an Incident Response Plan with Defined RTO/RPO
IR plans must document roles, communication channels, forensic preservation steps, and RTO/RPO for critical services. Link telemetry retention and forensic collection policies to ensure evidence availability during investigations.
26. Forensic Readiness: Endpoint & Network Artifact Collection
Ensure EDR, network capture, and log storage retain artifacts necessary for root-cause analysis. Automate artifact collection when incidents are declared and make all collections identifiable and auditable by the SIEM.
27. Post-Incident Review and Remediation Tracking
Conduct formal lessons-learned reviews and track remediation actions to closure. Correlate remediation timelines with risk register to demonstrate continuous improvement and compliance closure.
Vulnerability, Patch & Configuration Management
28. Continuous Vulnerability Scanning with Prioritized Remediation
Deploy authenticated scanning and integrate findings into a prioritized remediation backlog. Map vulnerabilities to asset criticality and threat intelligence to focus fixes. SIEM should consume scan results to identify exploited or unpatched assets in real time.
29. Enforce Configuration Baselines and Automated Drift Detection
Apply hardened baselines and monitor for configuration drift. Generate alerts on deviations and automate remediation where appropriate. Baseline enforcement reduces attack surface and supports compliance audits.
30. Patch Management with Risk-Based SLAs
Define patching SLAs by severity and criticality. Track patch deployment telemetry and correlate successful and failed patching attempts into the SIEM to identify at-risk assets.
Cloud & Hybrid Infrastructure Controls
31. Enforce Cloud Security Posture Management (CSPM) and Continuous Monitoring
Implement CSPM controls, monitor cloud configuration changes, and ingest cloud provider logs (CloudTrail, Azure AD, GCP audit logs). Normalize cloud telemetry so the SIEM can correlate cross-cloud events with on-prem detections.
32. IAM and Key Management Controls for Cloud Services
Harden cloud IAM policies, rotate keys, and monitor service account usage. Log and correlate suspicious role assumptions and key usage with anomalous activity detection.
33. Encrypt Data at Rest and in Transit with Key Lifecycle Controls
Mandate encryption and key management controls. Audit cryptographic key usage and log key management events into SIEM for detection of unauthorized key access or misuse.
Third-Party Risk, Supply Chain & Contracts
34. Assess and Monitor Third-Party Security Posture
Implement ongoing assessments and contract clauses for security obligations. Ingest vendor telemetry or service logs where possible and establish detection for third-party access anomalies to critical systems.
35. Enforce Least-Privilege and Time-Bound Third-Party Access
Grant third-party access only through controlled, monitored channels, with logging and JIT access where possible. SIEM should flag expired or excessive third-party entitlements and anomalous vendor activity.
Continuity, Backup & Physical Security
36. Implement Immutable Backups with Regular Recovery Tests
Enforce immutable backup storage and test recoveries against RTO/RPO. Monitor backup success/failure logs and correlate backup anomalies with potential ransomware activity to support rapid recovery actions.
37. Physical Security Controls Coordinated with Logical Access
Integrate physical access logs (badging, CCTV) with logical access and SIEM telemetry to detect coordinated physical-logical compromises. Correlation across domains reduces investigation time and prevents missed indicators.
People, Training & Continuous Compliance
38. Security Awareness, Phishing Simulations and Role-Based Training
Deliver continuous awareness programs and simulate phishing campaigns. Track user risk scores and remediation training completions. Feed user behavior signals into the SIEM to adjust detection thresholds and prioritize human-targeted attacks.

Why Cyber Silos Create Compliance and Security Failures
Pakistan Information Security Framework (PISF 2025)
Official PISF 2025 framework document — complete control matrix, compliance requirements, and implementation guidelines for Pakistani organisations. Free to download.
Download PISF 2025 PDFFragmented tooling — separate identity logs in IdP, network flows in a different platform, EDR on endpoints with local consoles — creates blind spots. Siloed data prevents cross-domain correlation, enabling stealthy lateral movement and delayed detection. For compliance, silos multiply evidence collection effort and raise the risk of incomplete audit trails. A centralized SIEM eliminates these silos by ingesting normalized telemetry, enriching with contextual metadata, and applying correlation logic across domains.
How SIEM Unifies Detection, Response, and Governance
A modern SIEM performs four essential functions that directly address PISF mandatory controls: log aggregation and normalization, real-time cross-domain correlation, automated orchestration through SOAR integrations, and audit-ready retention and reporting. Operationally, this translates to lower MTTD through advanced correlation and behavioral analytics, lower MTTR by automating containment and enrichment actions, and a single source of truth for compliance evidence.
Log Ingestion and Normalization Explained
Central ingestion involves standardized parsing rules and enrichment pipelines that attach asset criticality, business owner, vulnerability score, and identity context. Normalized events enable rule authors to write detections once and have them apply across on-prem, hybrid, and cloud estates. Failure to normalize results in duplicate rules, inconsistent alerts, and increased analyst cognitive load.
Cross-Domain Correlation and Real-Time Analytics
Correlating authentication anomalies, suspicious process execution, and egress DNS anomalies in real time is what distinguishes effective detection from noise. The SIEM must support stateful correlation windows, temporal sequencing, and scoring so alerts reflect the composite risk rather than isolated indicators. This reduces false positives and focuses the SOC on true incidents.
Automation and Orchestration to Reduce MTTD/MTTR
Automate routine investigative steps: enrichment (WHOIS, geolocation, TI lookup), containment (network isolation, AD disable), and ticket creation. Automation preserves analyst time for high-value decisions and compresses reaction time. SOAR playbooks must be auditable and reversible where required by policy.
Operational Challenges SOCs Face and How to Overcome Them
Download Official Framework Documents
PISF 2025 aur NCERT dono frameworks free download karein — compliance, audits, aur implementation planning ke liye.
PISF 2025
Pakistan Information Security Framework — complete control matrix & compliance guidelines
Download PISF PDFNCERT Framework
National Cyber Emergency Response Team — incident response procedures & reporting templates
Download NCERT PDFSOCs confront resource constraints, signal overload, composable tech stacks, and the need for continuous tuning. Address these through: prioritized detections aligned to risk, automated enrichment to reduce mean analyst handling time, simulation-driven validation of detections, and a unified data model to remove integration drag. Threat Hawk SIEM is designed to remove integration complexity and provide SOC-visible KPIs for coverage, false positive rate, and rule efficacy.
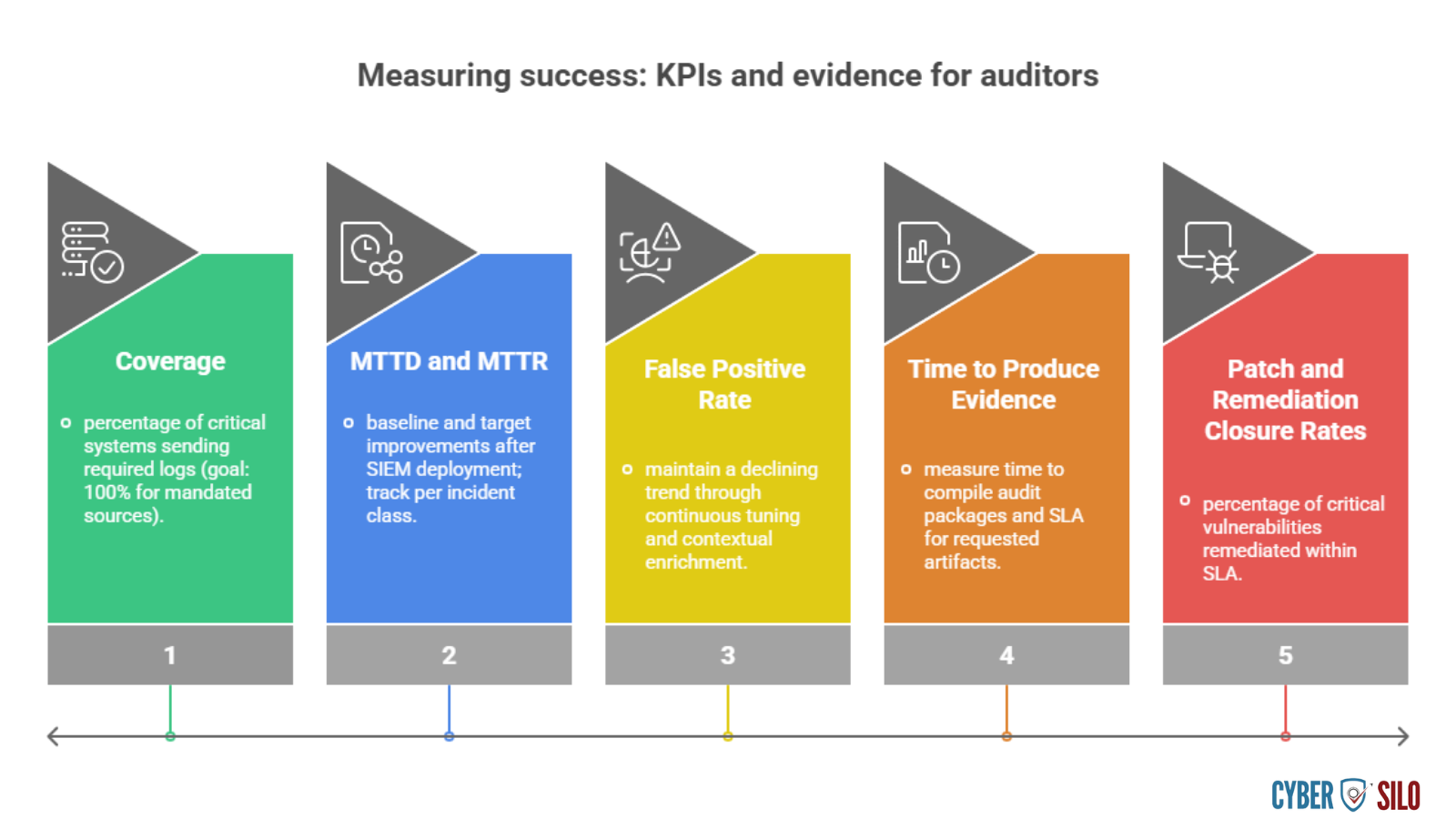
Measuring Success: KPIs and Evidence for Auditors
| KPI Metric | Description | Target Goal |
|---|---|---|
| Coverage | Percentage of critical systems sending required logs | 100% for mandated sources |
| MTTD and MTTR | Baseline and target improvements after SIEM deployment; track per incident class | Continuous reduction trend |
| False Positive Rate | Maintain a declining trend through continuous tuning and contextual enrichment | Below 10% for critical alerts |
| Time to Produce Evidence | Measure time to compile audit packages and SLA for requested artifacts | Under 24 hours for standard requests |
| Patch and Remediation Closure Rates | Percentage of critical vulnerabilities remediated within SLA | 95% within defined SLA window |
Operationalizing the Checklist with Threat Hawk SIEM
National Cyber Emergency Response Team (NCERT) Framework
Complete NCERT incident response framework — procedures, reporting templates, and coordination guidelines for critical infrastructure operators in Pakistan.
Download NCERT Framework PDFThreat Hawk SIEM centralizes log aggregation, normalization, threat intelligence, orchestration, and immutable retention in a platform built for hybrid enterprise scale. It reduces cyber silos by providing unified asset and identity context, pre-built PISF-aligned use cases, and an out-of-the-box evidence collection capability that maps directly to the 38 mandatory controls above. Using Threat Hawk SIEM, SOC teams can automate compliance evidence collection, maintain live dashboards for auditors, and enforce SLAs for detection and response.
Implementation Roadmap and Quick Wins
Prioritize actions to reduce risk and establish evidentiary controls quickly:
- Phase 1 (30 days): Centralize logs for authentication, EDR, and firewall; enforce MFA for admins; establish executive-signed policies.
- Phase 2 (60–90 days): Deploy core detections, implement playbooks for top incident types, instrument vulnerability-to-detection mapping.
- Phase 3 (90–180 days): Automate evidence retention, integrate third-party telemetry, and run red-team exercises to validate detection coverage.
Each phase should produce concrete artifacts for auditors: signed policies, SIEM dashboards, retention proofs, detection validation reports, and incident post-mortems.
Practical Tips for Audit Readiness
Pakistan Information Security Framework (PISF 2025)
Official PISF 2025 framework document — complete control matrix, compliance requirements, and implementation guidelines for Pakistani organisations. Free to download.
Download PISF 2025 PDF- Maintain a living compliance map that links each PISF control to concrete evidence locations and responsible owners.
- Automate periodic evidence exports (logs, detection tuning history, incident timelines) to immutable storage.
- Run internal audits quarterly that simulate regulator requests — measure time to collect and present required artifacts.
- Use detection playbooks that include evidence collection steps as part of the incident lifecycle.
Get Expert Guidance on PISF Compliance
Our cybersecurity experts at CyberSilo can help you implement a comprehensive PISF compliance program tailored to your organization's needs.
Schedule a Consultation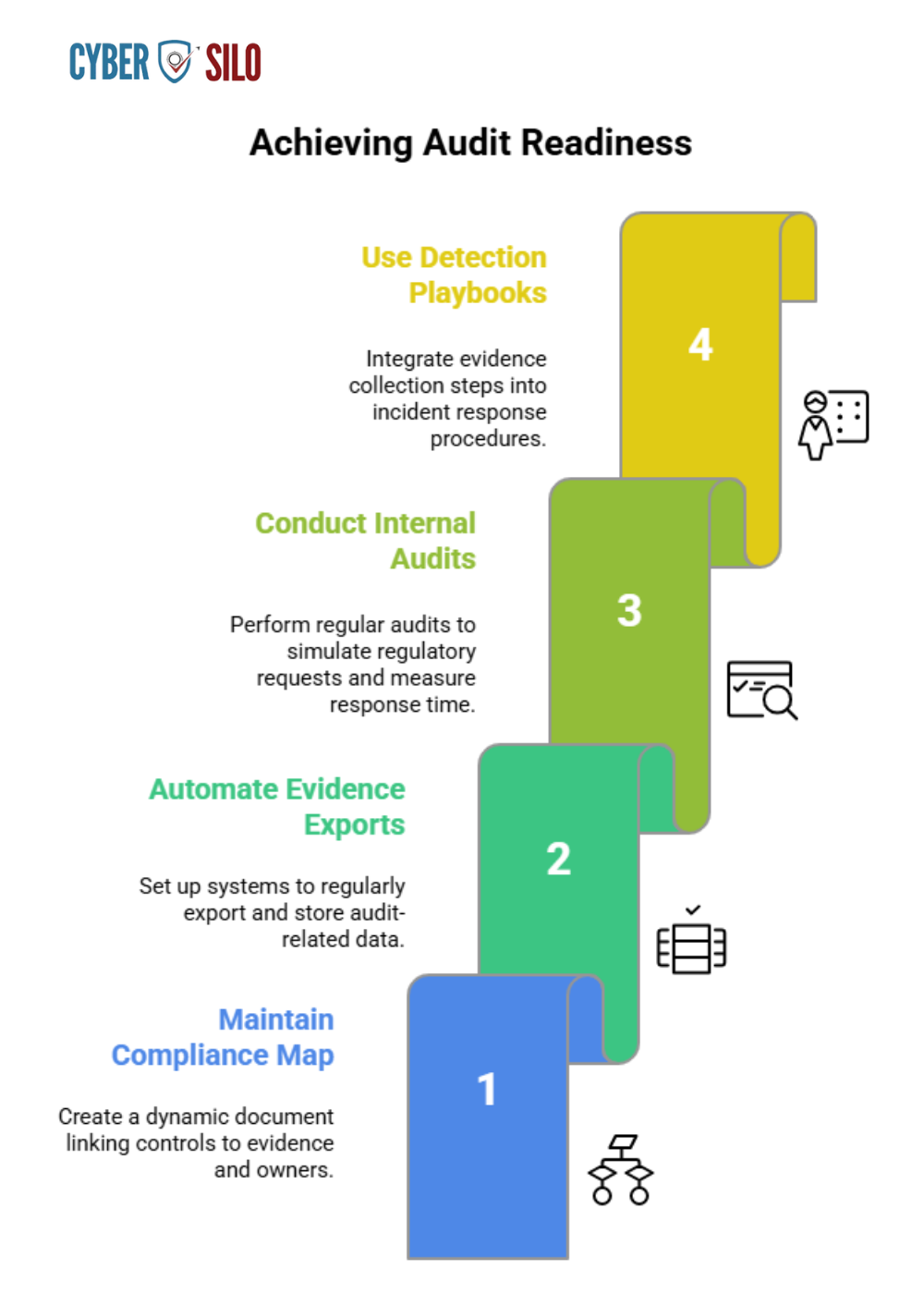
Final Recommendations and Next Steps
PISF 2025 compliance is achievable when controls are treated as operational programs, not one-off checklist items. Prioritize centralization of telemetry, normalization, and enrichment so your SOC can correlate across identity, network, endpoint, and cloud. Reduce alert fatigue by focusing on risk-aligned detections, and automate repeatable response procedures to improve MTTD and MTTR. Threat Hawk SIEM from CyberSilo provides the centralized visibility, real-time correlation, and compliance automation required to close the 38 mandatory controls at enterprise scale.
If you want an implementation-ready version of this PISF compliance checklist — mapped to telemetry sources, SIEM rules, and SOC playbooks — download the operational checklist that accompanies this guidance. Download Checklist to convert each mandatory control into prioritized workstreams, audit artifacts, and measurable KPIs.
Closing — PISF Compliance Checklist, Mandatory Controls PISF
Adopt a unified, evidence-first approach: centralize logs, normalize identity and asset context, apply risk-based detection, and automate response. Doing so lowers MTTD and MTTR, eliminates cyber silos, and provides the auditable trail regulators expect. Use the PISF compliance checklist above to guide tactical remediation and long-term security maturity — and leverage Threat Hawk SIEM where centralized visibility and SOC efficiency are critical to success. For more insights on selecting the right SIEM solution, explore our guide on the top 10 SIEM tools. To learn more about CyberSilo's mission and join our upcoming educational sessions, visit our webinars page.







