PISF 2025 Complete Guide: Pakistan Information Security Framework Explained — Immediate Operational Imperative
PISF 2025 (Pakistan Information Security Framework) and the nCERT framework set explicit expectations for how enterprises in Pakistan must detect, respond to, and govern cyber risk. The core operational challenge is not merely passing an audit; it is converting prescriptive controls into continuous, measurable security operations. If your organisation still relies on point tools, manual log reviews, or disconnected playbooks, PISF 2025 will expose those gaps in days — and regulators and customers will measure outcomes in incident metrics, not checkboxes. This guide translates PISF 2025 into SOC-level requirements and shows how a centralized SIEM architecture — exemplified by Threat Hawk SIEM — eliminates cyber silos, reduces MTTD and MTTR, and delivers evidence-ready compliance aligned to the nCERT framework.
What PISF 2025 Requires: Operational Controls, Evidence, and Outcomes
PISF 2025 defines control domains across governance, risk management, asset protection, identity and access, network and endpoint security, supply chain resilience, and incident handling. The nCERT framework frames an operational baseline for national critical infrastructure and private enterprises, calling for continuous monitoring, timely incident escalation, and auditable evidence trails. For security leaders the implication is clear: you must produce continuous detection, repeatable response, and proof of compliance at scale.
Key PISF 2025 Expectations That Drive SIEM Requirements
- Real-time visibility across on-premise, cloud, and OT/IoT assets.
- Comprehensive log aggregation with defined retention and integrity safeguards.
- Cross-domain correlation to detect multi-stage attacks and insider threats.
- Automated incident response playbooks and forensic data capture.
- Formalized evidence collection mapped to nCERT control statements.
- Scalable architecture to support rapid growth in telemetry volume.
Ready to Achieve PISF 2025 Compliance?
Discover how Threat Hawk SIEM can transform your security operations and ensure regulatory compliance.
Get Your Free Gap Assessment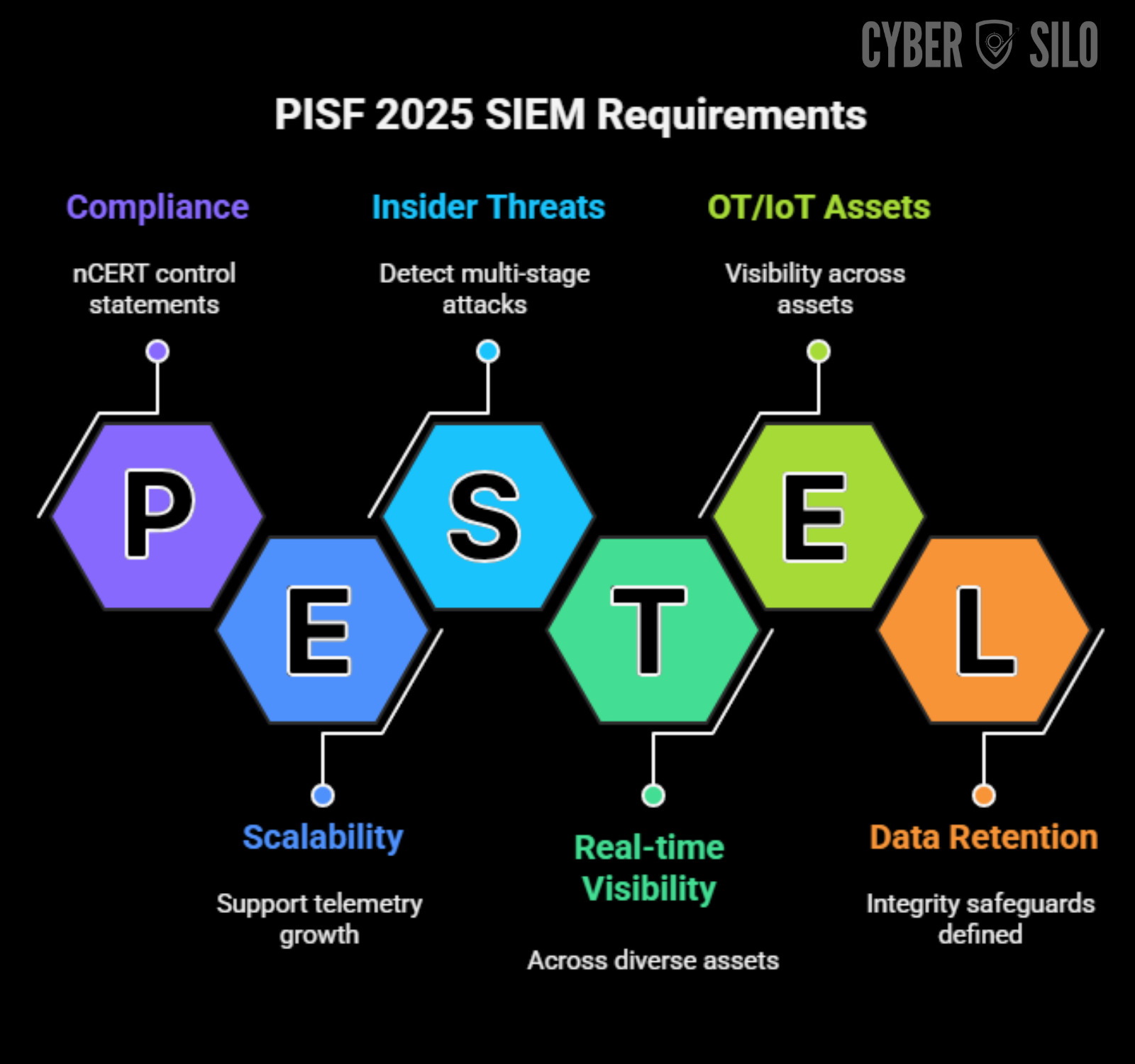
Why Organizations Struggle: How Cyber Silos Form and Why Fragmented Tooling Fails
Pakistan Information Security Framework (PISF 2025)
Official PISF 2025 framework document — complete control matrix, compliance requirements, and implementation guidelines for Pakistani organisations. Free to download.
Download PISF 2025 PDFCyber silos emerge from organisational structure, procurement practices, and technology sprawl. Different teams buy tools for specific problems — EDR for endpoints, a firewall for perimeter control, cloud-native logs for cloud workloads, and home-grown scripts for compliance reports. Each tool produces valuable telemetry, but when those data streams remain isolated, essential attack context evaporates.
Common Failure Modes In Fragmented Security Environments
- Log fragmentation: disparate formats and retention policies prevent end-to-end investigations.
- Alert fatigue: dozens of point-product alerts lack prioritisation and context, overwhelming analysts.
- Blind spots: cloud-native services, OT networks, and third-party systems are commonly under-instrumented.
- Slow investigations: manual correlation across tools extends MTTR and increases business impact.
- Compliance gaps: evidence is inconsistent and audit trails are incomplete or unverifiable.
These failures are not hypothetical. SOC teams routinely report that most time is spent hunting through multiple consoles and reconciling inconsistent timestamps and identifiers. Under PISF 2025, that operational overhead converts into regulatory risk and remediation costs.
How a Modern SIEM Becomes the Operational Spine for PISF 2025 and the nCERT Framework
A SIEM is not a checkbox product. Properly deployed, it is the unified data plane where telemetry, threat intelligence, and orchestration converge. For PISF 2025 compliance, the SIEM must provide continuous log aggregation, normalization, correlation, real-time analytics, case management, and automated evidence packaging. Threat Hawk SIEM is designed to operate as that spine, removing cyber silos and streamlining SOC workflows.
Essential SIEM Functions Required by PISF 2025
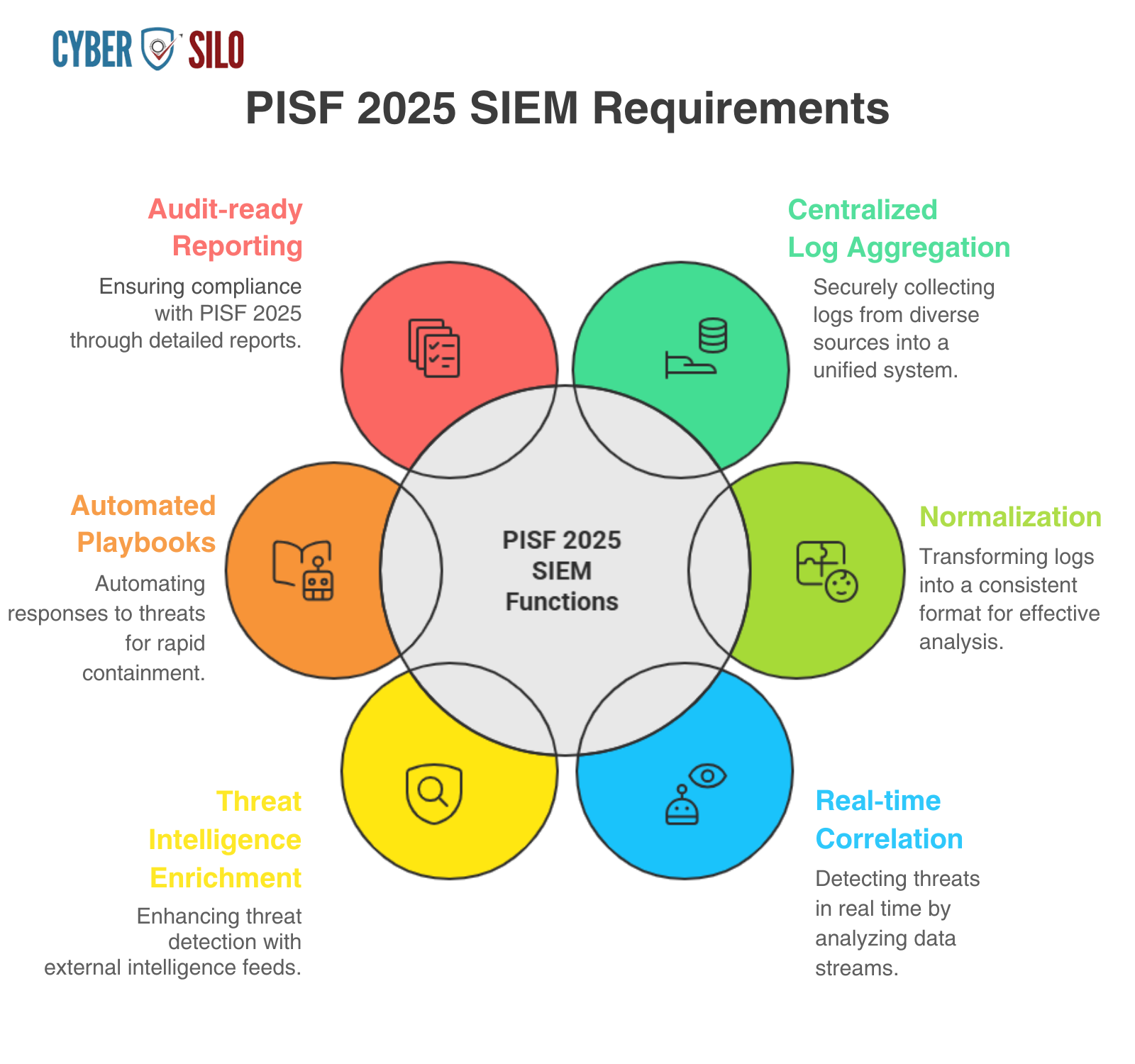
Threat Hawk SIEM: Technical Capabilities That Address PISF 2025 Demands
Threat Hawk SIEM focuses on enterprise operational needs rather than feature checklists. Its architecture supports high-throughput log ingestion, schema-driven normalization, and an indexing strategy optimized for forensic search. The correlation engine supports both signature-based rules and behavioural analytics (UEBA), enabling detection of lateral movement, privilege escalation, and cross-domain attack chains. Integration points include EDR, cloud IAM logs, network flow collectors, OT telemetry, and third-party risk feeds — eliminating the data silos that undermine PISF 2025 compliance.
How Threat Hawk SIEM Improves SOC Efficiency and Detection Accuracy
- Centralized visibility eliminates console hopping and reduces analyst context-switching.
- Real-time log correlation reduces MTTD through streaming analytics and stateful detections.
- Automated enrichment cuts mean-time-to-investigation by attaching identity, asset criticality, and prior incident history to alerts.
- Built-in case management and playbooks accelerate MTTR through consistent orchestration and audit trails.
- Scalable architecture supports retention policies necessary for regulatory evidence and forensic timelines.
Log Ingestion and Normalization: The Foundation of Reliable Detection
Download Official Framework Documents
PISF 2025 aur NCERT dono frameworks free download karein — compliance, audits, aur implementation planning ke liye.
PISF 2025
Pakistan Information Security Framework — complete control matrix & compliance guidelines
Download PISF PDFNCERT Framework
National Cyber Emergency Response Team — incident response procedures & reporting templates
Download NCERT PDFPISF 2025 requires auditable evidence and continuous monitoring. You cannot correlate what you do not collect, and you cannot trust detection without consistent timestamps, identifiers, and schema. Building a reliable ingestion and normalization pipeline is a technical discipline combining collectors, parsers, enrichment, and storage strategy.
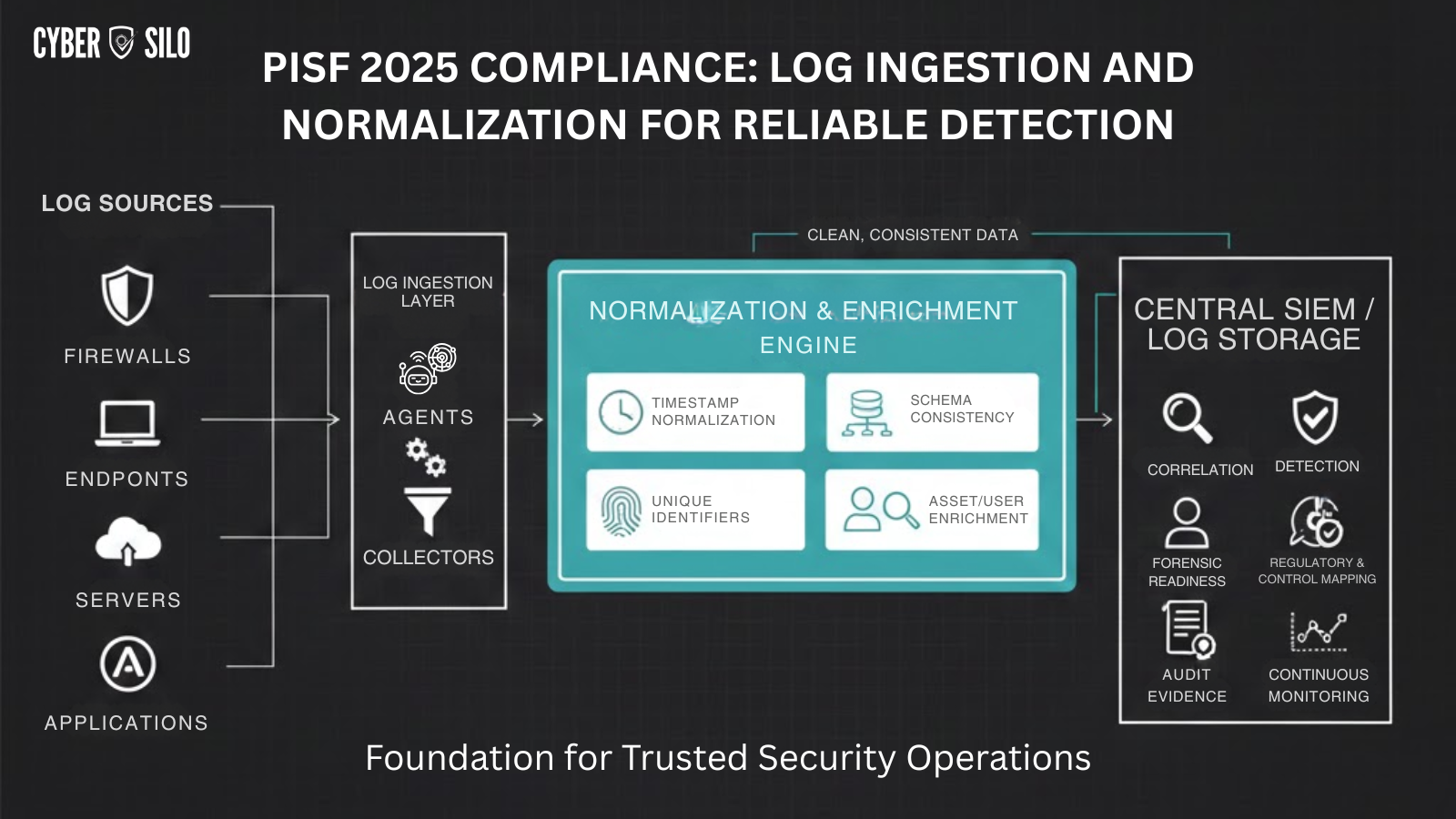
Collector Strategies and Secure Ingestion
- Agent-based collectors for hosts and endpoints for guaranteed delivery and rich context (process, parent-child, command line).
- Syslog and network collectors for NIDS/NIPS, firewalls, and routers; apply buffering and TLS to prevent data loss.
- Cloud-native collectors and APIs to capture IAM, VPC flow, and platform telemetry; handle rate-limits and batch windows.
- Passive network taps and flow exporters for OT/ICS environments where agents are not feasible.
Normalization and Enrichment
Normalization converts heterogeneous records into a consistent schema — canonical fields for timestamp, source/destination IP, user identity, host identifier, process, and action. Enrichment attaches contextual data: asset criticality, business owner, vulnerability scores, and threat intelligence hits. Critical normalization tasks include time normalization (NTP alignment), deduplication, and canonical user mapping across identity sources (LDAP, SSO, cloud IAM).
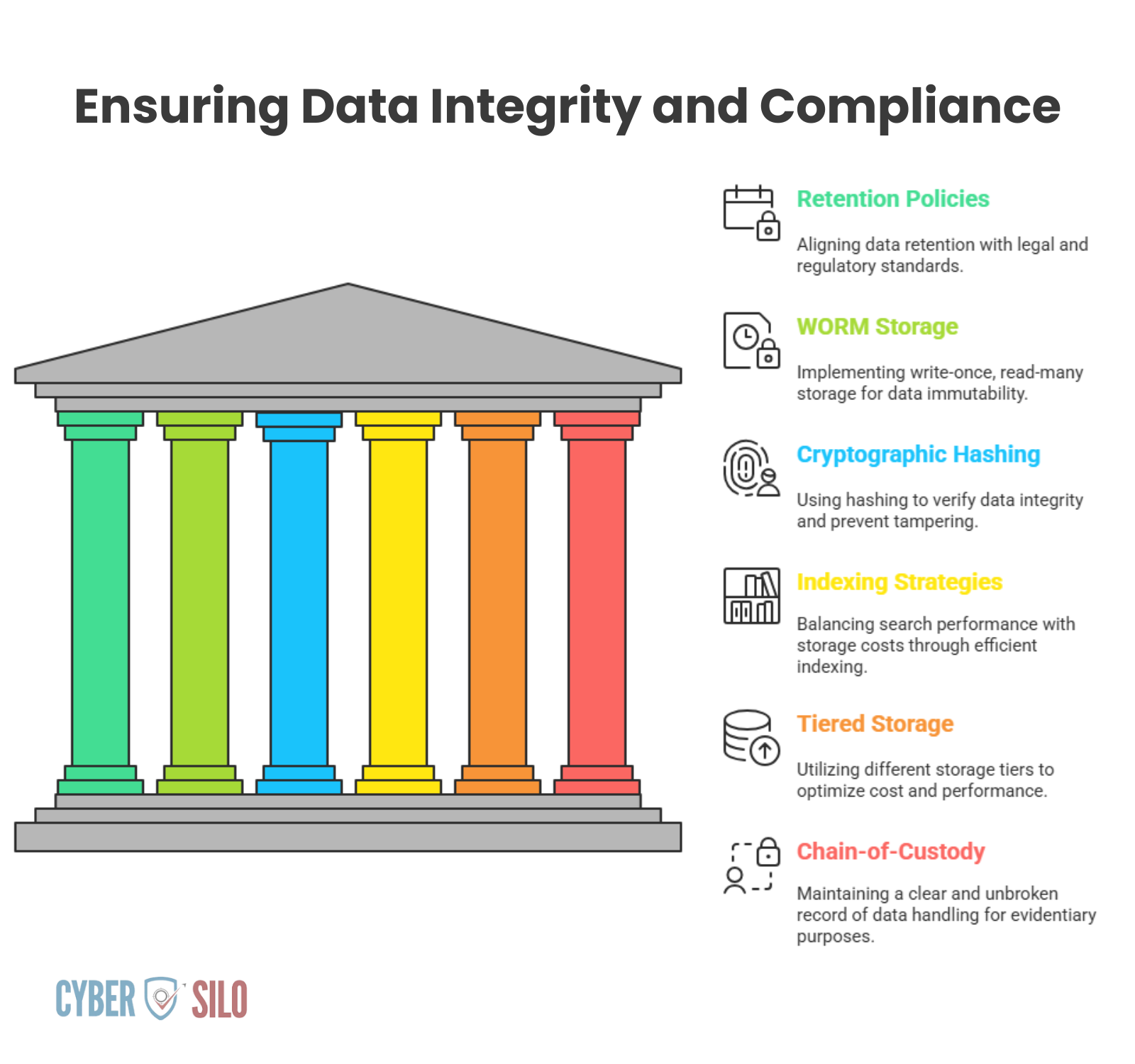
Storage, Retention, and Integrity
Retention policies should be driven by PISF 2025 control requirements and legal obligations. Implement write-once, read-many (WORM) storage or cryptographic hashing to ensure log integrity. Indexing strategies must balance search performance against storage cost; archive cold data with fast retrieval paths for forensic replay. Threat Hawk SIEM supports tiered storage models and ensures chain-of-custody preservation for evidentiary needs.
Cross-Domain Correlation and Real-World Detection Use Cases
Single-source signals rarely indicate sophisticated attacks. Detection effectiveness under PISF 2025 depends on cross-domain correlation: linking identity anomalies to endpoint telemetry, lateral movement on the network, and privilege changes in directory services. Correlation stitches these signals into actionable incidents with contextual scoring.
Practical Cross-Domain Detection Patterns
Mapping Detections to MITRE ATT&CK and PISF Controls
Attaching ATT&CK technique identifiers to detections accelerates incident triage and remediation. For PISF 2025, map each detection to specific nCERT control statements and produce automated evidence packages that include raw logs, enriched timelines, and analyst notes. This crosswalk simplifies audits and demonstrates repeatable compliance posture enforcement.
Want to Learn More About SIEM Solutions?
Explore our comprehensive guide on the top 10 SIEM tools to find the best fit for your organization.
Join Our Webinar Learn About Us
Real-Time Analytics, Streaming Detection, and Reducing MTTD
National Cyber Emergency Response Team (NCERT) Framework
Complete NCERT incident response framework — procedures, reporting templates, and coordination guidelines for critical infrastructure operators in Pakistan.
Download NCERT Framework PDFReducing Mean Time To Detect (MTTD) requires streaming analytics that operate on live telemetry with stateful evaluation. Batch-oriented systems miss the lead time where containment is most effective. Practical streaming analytics combine sliding window correlation, anomaly detection, and prioritized alerting.
Streaming Detection Mechanics
- Stateful rules evaluate sequences of events over defined windows (e.g., 5–60 minutes) to identify multi-step attacks.
- Anomaly detection profiles baseline behaviour per user, host, and network segment to find deviation beyond dynamic thresholds.
- Adaptive risk scoring aggregates signals into a single risk score to prioritise incidents for SOC attention.
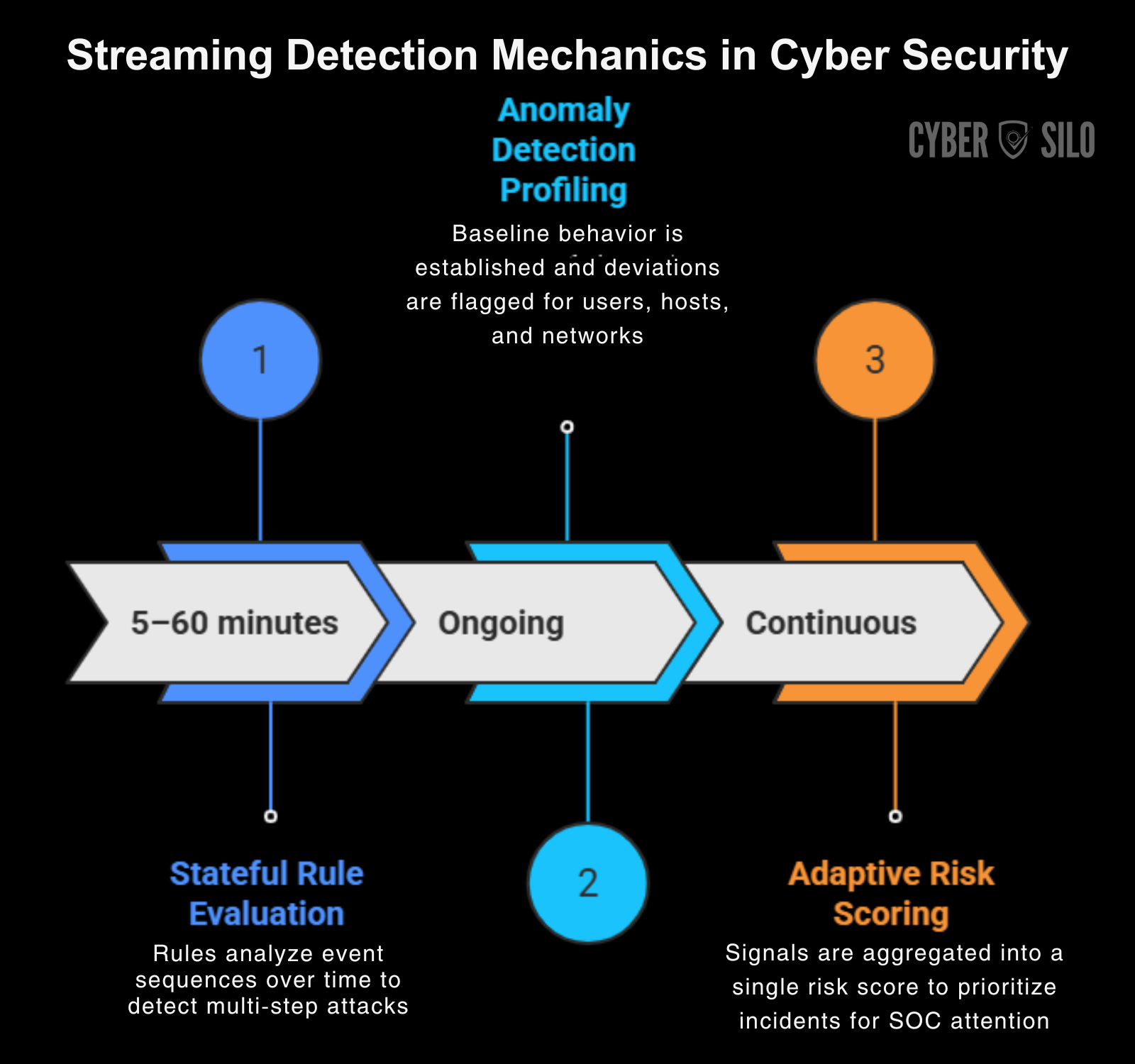
Effective streaming reduces MTTD by enabling earlier detection of reconnaissance and initial foothold activity. Threat Hawk SIEM's streaming engine supports complex state machines and low-latency alerting suitable for high-velocity environments.
Automation and Orchestration to Reduce MTTR and Ensure Consistency
Once detection occurs, time becomes critical. Manual containment is slow and error-prone. Automation and orchestration — when carefully governed — reduce Mean Time To Respond (MTTR) and preserve evidence chains required by PISF 2025.
Automation Playbook Patterns
- Enrichment playbook: automatically attach identity, asset value, and vulnerability context to new alerts.
- Containment playbook: escalate high-risk incidents and trigger EDR quarantine, firewall block, and NAC segmentation.
- Investigation playbook: collect full process trees, memory snapshots, and network captures for forensic analysis.
- Notification playbook: escalate to legal, privacy, or executive stakeholders according to incident classification.
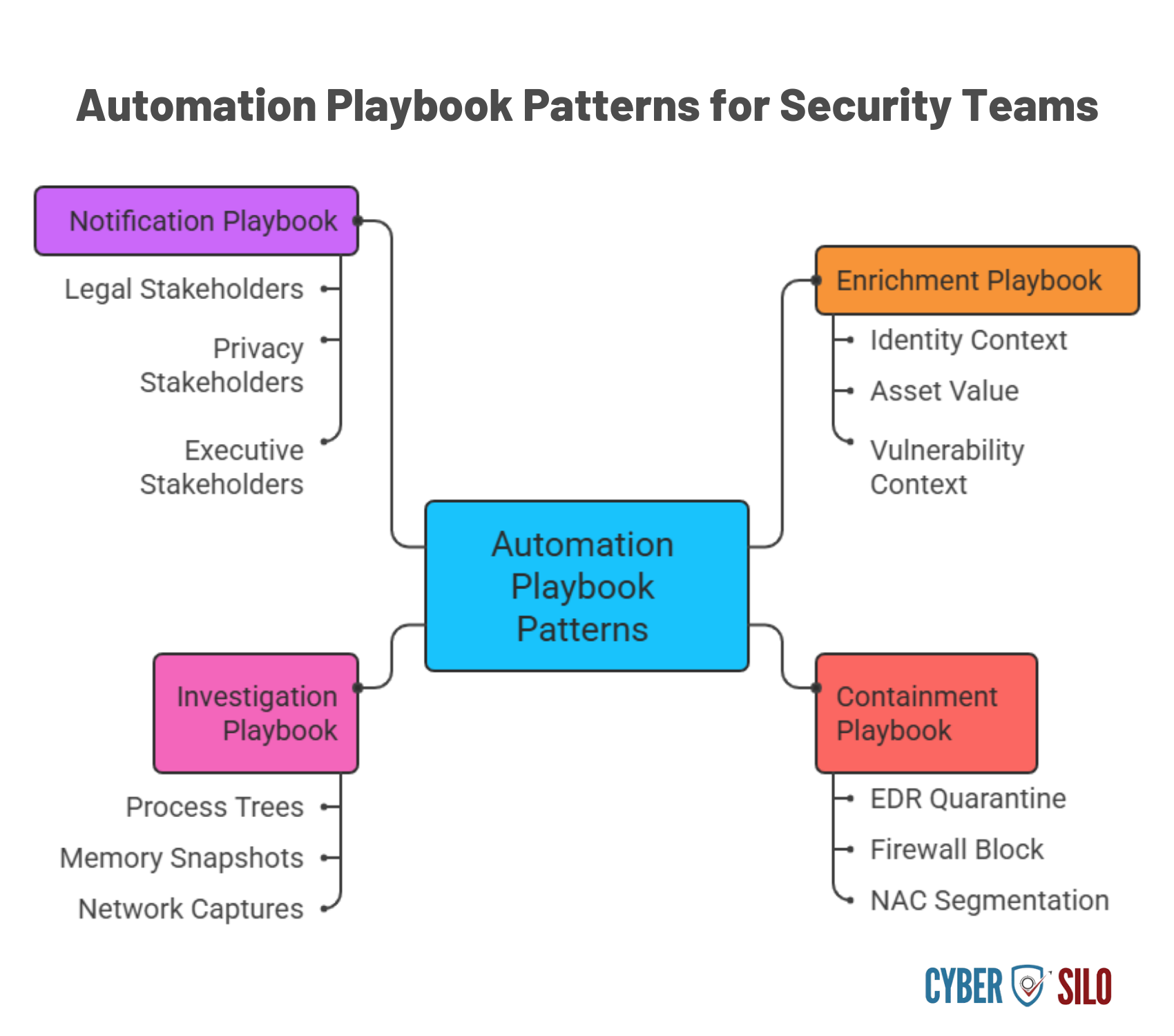
Playbooks must include human-in-the-loop checkpoints for high-impact actions. The objective is consistent response that reduces error, speeds remediation, and preserves required audit trails under PISF 2025.
Operationalizing Compliance: Evidence Collection, Reporting, and Continuous Monitoring
Pakistan Information Security Framework (PISF 2025)
Official PISF 2025 framework document — complete control matrix, compliance requirements, and implementation guidelines for Pakistani organisations. Free to download.
Download PISF 2025 PDFPISF 2025 requires more than periodic reports; it requires continuous evidence that controls are operating effectively. A SIEM converts telemetry into auditable proof by automating control checks, maintaining immutable logs, and producing regulator-ready reports.
Control-to-Evidence Mapping
Create a control matrix that maps each PISF 2025 and nCERT control to:
- Required telemetry sources (e.g., IAM logs, firewall logs, endpoint telemetry).
- Detections and KPIs that demonstrate control effectiveness (e.g., number of blocked brute force attempts, patch compliance rates).
- Report templates and retention requirements for audit evidence.
Continuous Compliance Mechanics
- Automated control audits run on schedule and when changes occur in the environment.
- Drift detection to identify configuration or policy changes that erode compliance posture.
- Evidence packages that include sanitized logs, timeline reconstructions, and chain-of-custody metadata for each incident.
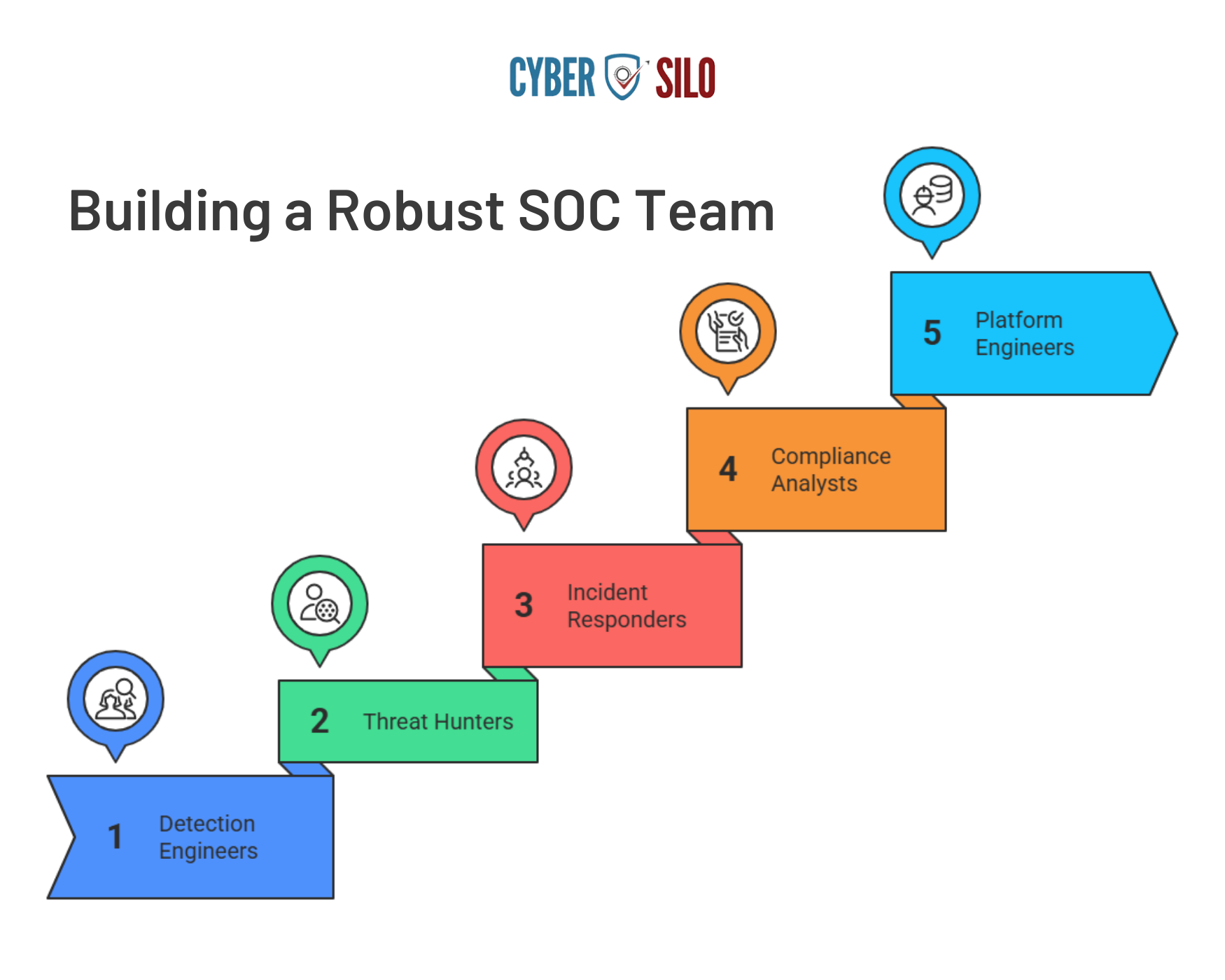
SOC Workflows and Organizational Changes Required by PISF 2025
Technology alone does not deliver compliance. PISF 2025 requires changes to SOC roles, processes, and measurements. Expect to shift from a reactive, alert-driven model to a proactive, risk-based operations model.
Recommended SOC Roles and Responsibilities
Operational KPIs to Track
- MTTD and MTTR for critical incidents.
- Percent of alerts triaged to closure within SLA.
- False positive rate and tuning iterations per quarter.
- Control coverage percentage mapped to PISF/nCERT requirements.
- Time to evidence package creation for audit requests.
Reducing Alert Fatigue Through Prioritization and Risk Scoring
Alert fatigue is a primary driver of missed incidents. Implement prioritization that combines business criticality (asset value), vulnerability exposure, and threat intelligence severity. Suppress noisy signals with tuned thresholds and use enrichment to elevate true positives. Continuous feedback loops — where analysts annotate detections and the system learns from those annotations — are essential to sustained reduction in noise.
Scalability, Data Sovereignty, and Hybrid Environments
PISF 2025 emphasises data protection and jurisdictional requirements. Many organisations operate hybrid environments: on-premise data centres, public/private cloud, and remote users. Your SIEM must provide consistent policy enforcement and data handling across these domains while respecting data residency and encryption rules.
Key Technical Requirements for Hybrid Scale
- Distributed collectors to minimize network egress while ensuring secure delivery to central analytics.
- Edge processing capabilities for pre-filtering and enrichment in bandwidth-constrained locations.
- Support for region-specific storage and retention to meet data sovereignty constraints.
- Elastic compute for peak ingestion periods with predictable cost models.

Threat Hawk SIEM supports hybrid deployments, enabling local log buffering and encrypted transport to central analytics, with configuration options for data residency and tiered retention aligned to PISF 2025 policies.
Measurable Business Benefits and Cost-of-Delay Analysis
Decision-makers must justify SIEM investments with measurable outcomes. The two clearest metrics are time-to-detect and time-to-contain. Each day of delayed detection adds exponential risk and cost.
Illustrative Cost-of-Delay Scenario
- Average data breach lifecycle without centralized detection: MTTD = 45 days, MTTR = 60 days; median cost per incident rises with dwell time.
- After SIEM deployment and automation: MTTD reduced to 8–24 hours, MTTR reduced to 24–72 hours for high-risk incidents.
- Reduced dwell time lowers incident remediation costs, legal exposure, and reputational damage; it also reduces required notification scope under regulatory regimes.
Beyond incident costs, centralized SIEM reduces operational inefficiencies: fewer consoles, standardized playbooks, and automated reporting lower overhead and free skilled analysts for proactive tasks like hunting and tuning.
Implementation Roadmap for PISF 2025 Compliance with Threat Hawk SIEM
Successful implementation requires sequencing technical work with organisational change. Below is a pragmatic roadmap designed for rapid risk reduction and sustained maturity growth.
Phase 0 — Rapid Gap Assessment
- Inventory telemetry sources, identify control gaps relative to PISF 2025 and the nCERT framework.
- Prioritise critical assets and regulatory obligations.
- Deliver a remediation roadmap with measurable milestones.
Phase 1 — Foundation: Ingestion, Normalization, and Baselines (0–3 Months)
- Deploy collectors for high-value sources (directory, firewall, EDR, cloud logs).
- Normalize schemas and align timestamps; implement retention baseline for critical logs.
- Establish SLAs for ingestion reliability and data integrity checks.
Phase 2 — Detection and Orchestration (3–6 Months)
- Implement prioritized correlation rules mapped to nCERT controls and ATT&CK techniques.
- Deploy SOAR playbooks for containment and evidence collection for the top 10 use cases.
- Start automated compliance reporting for auditors and leadership dashboards.
Phase 3 — Optimization and Continuous Improvement (6–12 Months)
- Refine risk scoring and reduce false positives via tuning and analyst feedback loops.
- Expand telemetry coverage to OT, third parties, and cloud-native services.
- Institutionalize threat hunting and red-team feedback cycles to validate detections.
Quick Wins vs Long-Term Investments
- Quick wins: centralize identity and firewall logs, deploy a small set of high-confidence rules, automate evidence collection for critical incidents.
- Long-term investments: implement UEBA, archive strategies, integrate vendor risk telemetry, and build continuous control testing pipelines.
Start Your PISF 2025 Compliance Journey Today
CyberSilo is here to help you navigate the complexities of PISF 2025 compliance with our proven Threat Hawk SIEM solution.
Contact Our Security TeamConclusion: From Compliance Requirement to Operational Advantage
PISF 2025 and the nCERT framework represent a shift from periodic compliance to continuous security operations. The organisations that succeed will be those that convert policy into measurable SOC outcomes: lower MTTD, faster MTTR, auditable evidence, and demonstrable control effectiveness. Centralizing telemetry and detection in a modern SIEM eliminates the cyber silos that create blind spots and operational friction.
Threat Hawk SIEM, as implemented by CyberSilo's operational teams, delivers the centralized visibility, real-time correlation, and automation required to meet PISF 2025 obligations while driving SOC efficiency and reducing business risk. If your priority is to close critical gaps quickly and build a sustainable security operations capability aligned to the nCERT framework, start with a practical assessment that yields immediate remediation actions and a roadmap to full compliance.
Next Step: Free Gap Assessment (Operational, Not Theoretical)
Request a Free Gap Assessment to map your current telemetry and control posture to PISF 2025 and the nCERT framework. The assessment provides:
- A prioritized list of control gaps tied to operational impact (MTTD/MTTR influence).
- An ingestion and detection roadmap aligned to Threat Hawk SIEM deployment patterns.
- Estimated timelines and resource plans for quick wins and long-term maturity.
Use the assessment to convert compliance obligations into practical SOC deliverables: fewer silos, better detection accuracy, faster incident handling, and regulator-ready evidence. Contact our security team to get started.







