How CyberSilo's TEM Platform Addresses PISF 2025 Requirements

PISF 2025 raises the bar for continuous monitoring, vulnerability management, and auditable incident response. The challenge for enterprise security leaders is not the existence of controls on paper but operationalizing them across fragmented estates—on‑premise data centers, hybrid clouds, remote work endpoints, and third‑party integrations. CyberSilo's Threat Hawk SIEM, as the analytics and orchestration core of our TEM (Threat Event Management) platform, is designed to turn PISF 2025 requirements into repeatable SOC workflows: eliminate cyber silos, centralize visibility, accelerate detection and response, and produce compliant evidence without overwhelming analysts.
What PISF 2025 Demands from Security Operations
PISF 2025 emphasizes continuous risk reduction through measurable controls. Key operational demands that map directly to SOC capabilities include:
Meeting PISF 2025 is not a checklist exercise; it requires a platform that integrates telemetry, enriches context, executes runbooks, and generates auditable evidence continuously.
Why Cyber Silos Kill PISF Readiness
Cyber silos form when monitoring, vulnerability scanning, identity feeds, and ticketing live in disconnected tools. Operationally, silos create three core failures:
- Blind spots: Events that span identity and network logs are invisible if correlation is absent.
- Alert deluge: Duplicate or low‑value alerts flood analysts when enrichment and deduplication are missing.
- Manual evidence assembly: Auditors get PDFs and spreadsheets instead of a reproducible trail.
Fragmented tooling fails at scale because human operators cannot quickly correlate thousands of events per second into a coherent incident narrative. The downstream costs are measurable: longer dwell times, missed SLAs, and failed audits. For PISF, where timely vulnerability mitigation and demonstrable incident handling are mandatory, those costs translate directly into regulatory exposure and higher residual risk.
Eliminate Cyber Silos with Threat Hawk SIEM
Discover how Threat Hawk SIEM centralizes visibility and accelerates your PISF 2025 compliance journey.
Request a DemoThreat Hawk SIEM: PISF Compliance Tools and Centralized Security Backbone
Threat Hawk SIEM functions as the central nervous system for TEM: unified log aggregation, normalization, enrichment, correlation, automated response, and compliance reporting. It was built with three operational imperatives in mind—eliminate silos, reduce mean time to detect (MTTD), and shorten mean time to respond (MTTR)—while producing auditable evidence aligned with PISF 2025.
Log Ingestion and Normalization
Threat Hawk accepts telemetry from any source: syslog, Windows Event Forwarding, cloud service logs, API connectors, network taps, endpoint agents, and message queues. Ingestion pipelines use schema mapping to normalize disparate fields into a consistent event model. Benefits:
- Field‑level normalization enables cross‑source correlation without custom scripting.
- Parsing pipelines include built‑in and extensible parsers for common formats and bespoke application logs.
- High‑throughput collectors buffer and forward securely to protect against transient outages, ensuring log completeness for audit purposes.
Cross‑Domain Correlation and Enrichment
Correlation is where detection becomes actionable. Threat Hawk combines deterministic correlation rules and statistical models:
- Deterministic rules tie authentication failures, privilege escalations, and lateral movement indicators into high‑confidence incidents.
- Anomaly detection uses historical baselines for accounts, devices, and network flows to surface deviations that deterministic rules miss.
- Enrichment integrates asset inventories, vulnerability feeds, identity sources, and threat intelligence to contextualize alerts—turning raw events into prioritized incidents for SOC analysts.
Real‑Time Analytics and Prioritized Alerting
Real‑time stream processing applies both signature and behavior analytics to sliding windows of events. The system outputs alerts with a calculated risk score that factors in:
- Exploitability (e.g., known exploit observed in threat intel)
- Exposure (vulnerable asset criticality and network reachability)
- Business impact (identity context: privileged account vs. service account)
Prioritized alerting reduces alert fatigue by ensuring analysts only investigate incidents above defined risk thresholds; less urgent items can be routed to vulnerability management queues or handled via automation.

Threat Intelligence and Contextualization
Threat Hawk ingests internal and external threat intelligence feeds and uses deterministic matching and enrichment to attach relevant indicators (IOCs), TTP mappings, and confidence scores to events. This approach speeds attribution, facilitates containment decisions, and feeds compliance evidence that shows intelligence‑driven decision making.
Scalable, Resilient Architecture
Threat Hawk runs on a distributed architecture that scales by ingestion throughput and compute. Deployment models include on‑premise, hybrid, and cloud instances to meet data residency and sovereignty needs in PISF environments. Key operational features:
- Elastic ingestion nodes with backpressure handling.
- Indexed storage for rapid search and immutable WORM archives for compliance retention.
- High availability across control and data planes with role‑based access and multi‑tenancy support for complex organizational structures.
Integrating Vulnerability Management PISF Requirements into TEM Workflows
PISF 2025 elevates vulnerability management from periodic scanning to continuous lifecycle management: discovery, prioritization, remediation, and validation. CyberSilo's TEM integrates vulnerability management PISF requirements into detection and response workflows so that vulnerabilities become first‑class context during incident handling.
Asset Discovery and Continuous Inventory
An accurate, continuously updated asset inventory is the foundation for effective vulnerability management. Threat Hawk consolidates asset data from network discovery, endpoint agents, cloud inventories, and CMDBs. Each asset record contains:
- Unique identifiers and ownership metadata
- Software composition and installed packages
- Network topology and exposure profiles
- Historical vulnerability scan results and patch status
By resolving identity and asset context, Threat Hawk converts vulnerability scanner outputs into prioritized remediation tasks based on business impact and exploitable attack paths.
Prioritization: From CVSS to Contextual Risk
CVSS is a starting point but not a decision driver on its own. Threat Hawk applies multi‑factor risk scoring that blends CVSS with: asset criticality, exploit availability, presence of mitigations, network segmentation, and threat intel indicating active exploitation. The resulting risk score drives SLAs, urgency flags, and automated remediation routes.
Workflow Integration and Patch Orchestration
Vulnerabilities feed into ticketing and orchestration systems with the necessary remediation context: affected hosts, proof of existence, exploitability evidence, and recommended fix actions. For PISF compliance, Threat Hawk provides:
- SLA enforcement and escalation for critical CVEs
- Automated patch orchestration or configuration changes via integration with remediation tools
- Verification loops that confirm patches applied and vulnerabilities closed
Vulnerability Validation and Post‑Remediation Evidence
Validation is essential for auditability. Threat Hawk performs follow‑up scans and monitors telemetry for indicators that demonstrate successful remediation. Every validation step is timestamped and appended to an immutable incident record, providing auditors with a clear chain of custody from detection to closure.
Explore More SIEM Solutions
Learn about the top 10 SIEM tools and how they compare to Threat Hawk SIEM for PISF compliance.
Join Our Webinar Learn About UsAutomated Playbooks and Orchestration for PISF Workflows
PISF 2025 expects documented and repeatable incident handling. Threat Hawk's automation engine translates runbooks into executable playbooks that combine detection, response, and compliance tasks.
Example Playbook: Critical Remote Code Execution (RCE) Vulnerability
- Trigger: Vulnerability scanner identifies RCE on externally facing asset and threat intel reports active exploitation.
- Enrichment: Correlate with ingress firewall logs, antivirus alerts, and recent anomalous SSH sessions.
- Containment Actions: Quarantine host, block IP ranges, and revoke service credentials via identity provider integration.
- Remediation Actions: Initiate patch orchestration or service restart through configuration management API.
- Validation: Re‑scan host and monitor for regression telemetry; record proof in incident dossier.
- Compliance Output: Generate report mapping actions to PISF control sections with timestamps and signed audit entries.
Operationalizing Compliance: Evidence, Audit Trails, and Reporting
PISF audits demand verifiable evidence that controls are implemented and effective. Threat Hawk produces machine‑readable and human‑friendly artifacts aligned to compliance checkpoints:
- Immutable event logs with cryptographic signing and retention policies aligned to PISF timelines.
- Role‑based access controls and separation of duties with complete audit trails for who viewed or altered incident records.
- Pre‑mapped control coverage reports that translate telemetry and actions into PISF control IDs for auditor review.
- Continuous compliance dashboards that surface control drift, overdue remediation, and audit readiness metrics.
Automated evidence collection removes the common need to manufacture compliance artifacts at audit time and demonstrates continuous control operation—exactly what PISF 2025 auditors will expect.
Cutting MTTD and MTTR: Concrete Mechanisms and Expected Outcomes
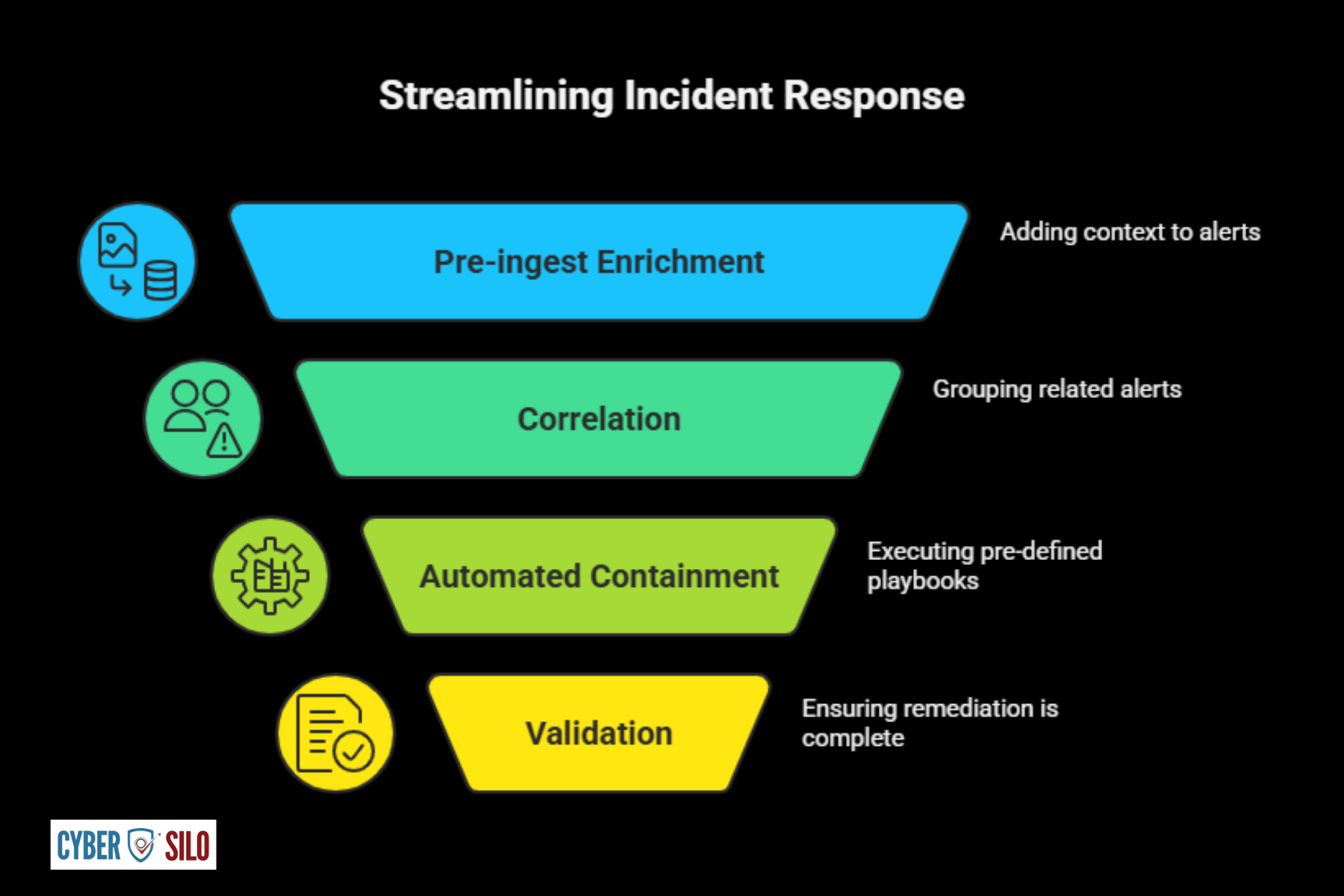
Reducing MTTD and MTTR requires instrumented telemetry, prioritized alerts, and automated remediation. Threat Hawk accomplishes this in several ways:
- Pre‑ingest enrichment reduces analyst lookup time by supplying asset, identity, and vulnerability context with each alert.
- Correlation of multi‑vector indicators reduces noisy, disjointed alerts into single incidents with higher signal‑to‑noise ratios.
- Automated containment playbooks remove manual steps for common incidents, lowering MTTR for repeatable scenarios.
- Playbooks coupled with validation loops ensure remediation is completed and documented—reducing rework and verifying compliance.
In practice, environments that adopt centralized detection and orchestrated response typically see MTTD reductions of an order of magnitude for high‑confidence incidents and proportional MTTR improvements once playbooks replace manual escalation paths. Those performance gains translate into lower dwell times, fewer compromised systems, and more defensible audit positions under PISF.
Implementation Considerations for Complex Enterprise Environments
Successful TEM adoption requires realistic planning beyond feature checklists. Key considerations for enterprise deployments include:
Data Residency and Sovereignty
PISF may impose constraints on where sensitive logs and forensic evidence can be stored. Threat Hawk supports regionally isolated deployments and hybrid storage models that segregate sensitive telemetry while enabling centralized analytics.
Event Volume and Sizing
Plan for peak events per second (EPS) and retention windows driven by compliance. Threat Hawk supports tiered storage—hot for fast search, warm for investigative timelines, and cold/worm for long‑term retention—balancing cost and accessibility.
Integration with Existing Toolchains
Replace only where necessary. Threat Hawk integrates with endpoint detection platforms, vulnerability feeds, cloud service logs, identity providers, and ITSM systems so existing investments remain valuable while enabling centralized correlation and automation.
Operational Readiness and Training
Platform capability is only as good as operator skill. CyberSilo provides SOC readiness packages: playbook libraries aligned to PISF controls, analyst training modules, and runbook templates that speed adoption and reduce human error.
High Availability and Disaster Recovery
Threat Hawk supports geographic redundancy and automated failover for both ingestion and query planes. For PISF, disaster recovery plans include preservation of audit evidence and forensic artifacts during failover events.
Detection‑to‑Remediation Scenarios: Practical Workflows
Below are representative scenarios demonstrating how Threat Hawk converts telemetry into compliant remediation.
Scenario A: Lateral Movement After Phishing
- Detection: Abnormal authentication sequences, suspicious process creation on an endpoint, and SMB enumeration events correlate as lateral movement.
- Enrichment: Threat Hawk attaches user role, recent vulnerability posture of endpoint, and existing MFA status.
- Response: Automated playbook disables compromised account, isolates endpoint at the network layer, spins up forensic snapshot, and opens ITSM ticket for remediation.
- Compliance: All actions logged, snapshots hashed, and a timeline report generated mapping steps to PISF incident reporting requirements.
Scenario B: Exploited Critical Vulnerability in Public‑Facing Application
- Detection: Web server logs show anomalous payload patterns matched to a known exploit signature; vulnerability inventory shows an unpatched CVE.
- Response: Immediate WAF rule application to block exploit vectors, temporary redirect to a maintenance page, and orchestration to apply patch on validated hosts.
- Audit: Post‑remediation scans confirm closure; mitigation timeline and evidence are automatically packaged into an auditor‑ready report.
Scenario C: Insider Data Exfiltration Attempt
- Detection: Large outbound transfers from a user outside usual hours, concurrent with privileged access changes.
- Enrichment: Data classification tags, user role, and prior anomaly history appended to the incident.
- Response: Automated content hold on email/cloud storage, escalation to legal and HR workflows, and initiation of formal incident response with full chain‑of‑custody documentation for investigatory use.
- Compliance: Sensitive data handling and notification steps are tracked against PISF timelines and reporting obligations.
KPIs, SLAs, and Metrics to Demonstrate PISF Readiness
To demonstrate operational maturity and readiness for PISF 2025, SOC leaders should track and report the following metrics:
- Mean Time to Detect (MTTD) by severity tier
- Mean Time to Respond (MTTR) and mean time to remediate for vulnerabilities
- Percentage of critical vulnerabilities remediated within PISF SLAs
- Alert triage rate and analyst time saved through automation
- False positive rate and improvements due to correlation and enrichment
- Number of audit‑ready incidents with complete evidence packs
- Coverage metrics: percent of assets ingesting logs and percent of critical services monitored
These indicators give boards and auditors confidence that controls are not only implemented but are effective and measurable.
See Threat Hawk SIEM in Action
Experience how CyberSilo's TEM platform transforms PISF 2025 compliance from obligation to operational advantage.
Contact Our Security TeamWhy CyberSilo's TEM and Threat Hawk SIEM Fit PISF 2025 Operational Needs
Threat Hawk is engineered for operational realism. Its design assumes incomplete inventories, noisy telemetry, constrained SOC resources, and the need to produce auditable artifacts on demand. CyberSilo complements the platform with SOC playbooks aligned to PISF, integration accelerators for enterprise toolchains, and professional services to operationalize runbooks and training. The result is a platform that focuses on outcomes: fewer blind spots, measurable reductions in MTTD/MTTR, and continuous evidence generation for auditors.
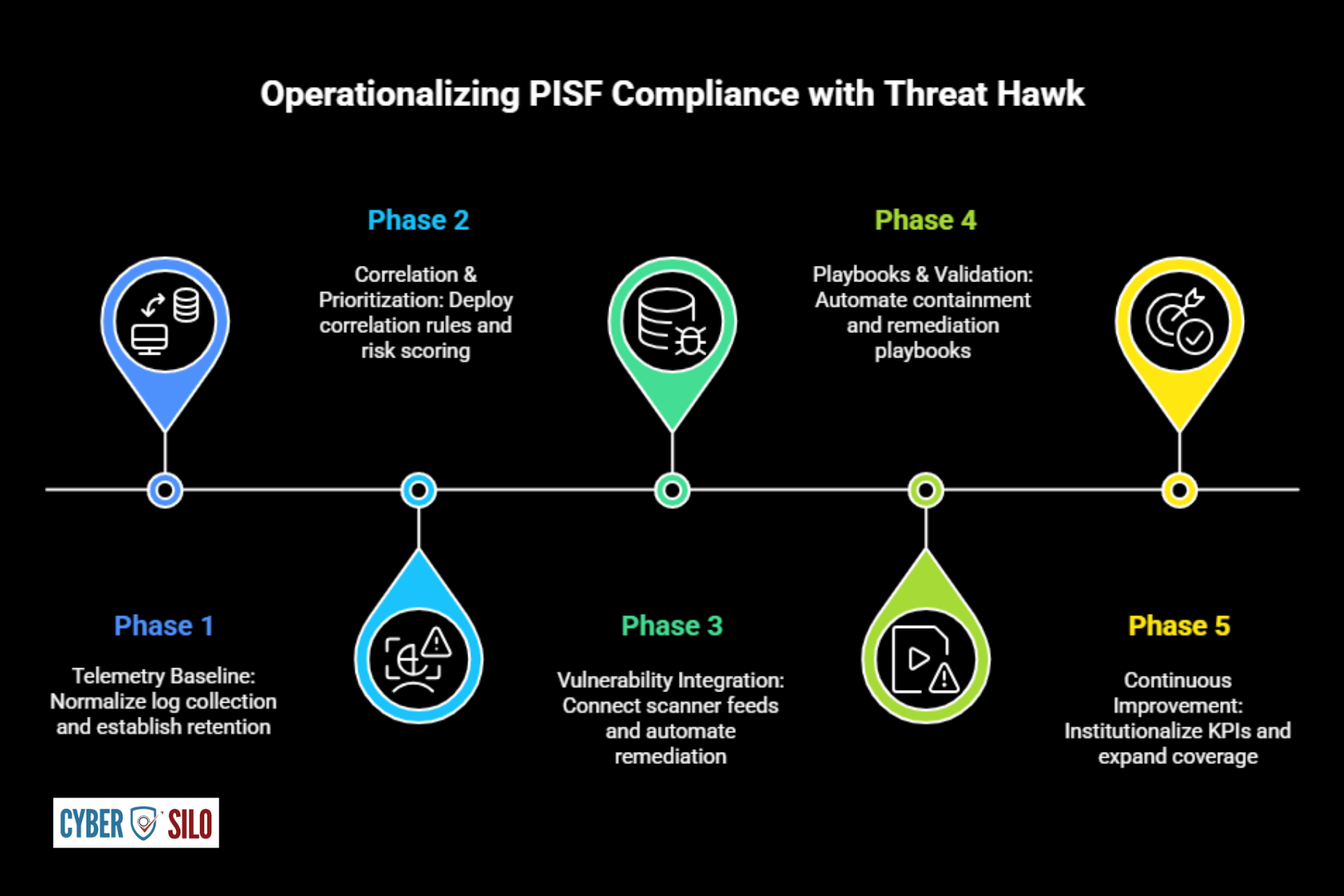
Next Steps to Operationalize PISF Compliance with Threat Hawk
Adopting a centralized TEM approach is an incremental program, not a single project. Recommended phased approach:
- Phase 1 — Telemetry Baseline: Normalize log collection across high‑risk assets and establish immutable retention.
- Phase 2 — Correlation & Prioritization: Deploy correlation rules and risk scoring to reduce alert noise.
- Phase 3 — Vulnerability Integration: Connect scanner feeds, implement prioritization logic, and automate remediation tickets.
- Phase 4 — Playbooks & Validation: Automate containment and remediation playbooks with verification and compliance reporting.
- Phase 5 — Continuous Improvement: Institutionalize KPIs, tune detection, and expand coverage to remaining assets.
Each phase produces auditable artifacts that align to PISF control objectives, turning compliance into an operational capability rather than a one‑time exercise.
Conclusion and Action
PISF 2025 requires more than controls on paper; it requires an operational platform that unifies telemetry, prioritizes risk, automates response, and produces auditable evidence continuously. Threat Hawk SIEM—embedded in CyberSilo's TEM—addresses these needs with centralized visibility, real‑time correlation, vulnerability management PISF alignment, and orchestration that reduces MTTD and MTTR while making compliance demonstrable.
To see how these capabilities map to your environment—asset coverage, EPS sizing, and PISF control mappings—schedule a hands‑on session. Request Demo to evaluate threat detection accuracy, SOC efficiency gains, and compliance readiness in a sandbox with your own telemetry and controls. Operational improvements and measurable risk reduction start with a practical demonstration of how Threat Hawk converts fragmented signals into auditable security outcomes. Contact our security team to get started.







